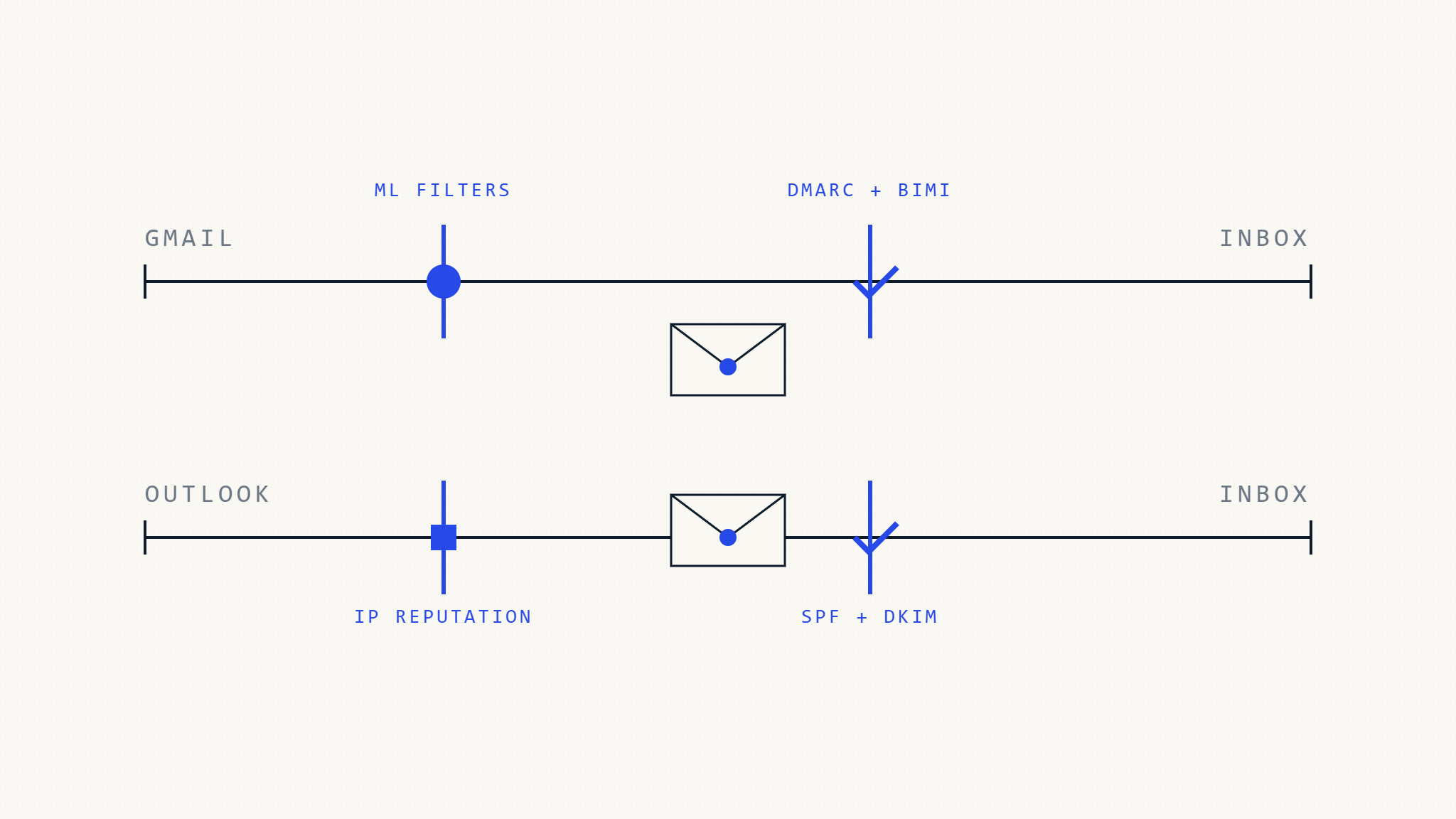
Gmail and Outlook use different filtering algorithms and authentication requirements. Learn platform-specific optimization strategies to maximize deliverability.
Filed 21 Apr 2026 · 6 min read
Read the analysisThe standards that prove who you are — and the practices that keep you in the inbox.
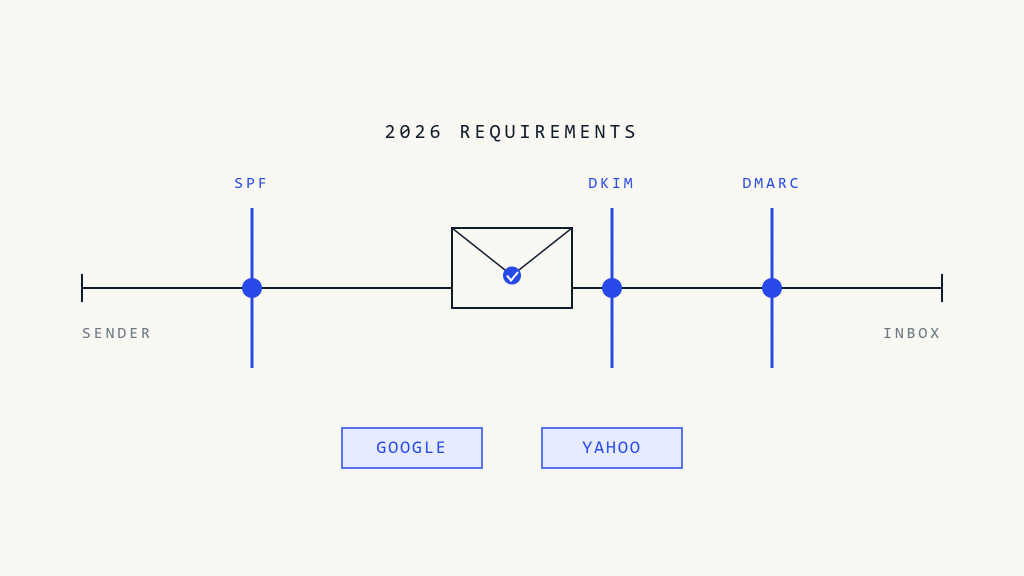
Master Google and Yahoo's latest email authentication requirements for 2026. Complete guide to SPF, DKIM, and DMARC compliance for bulk…
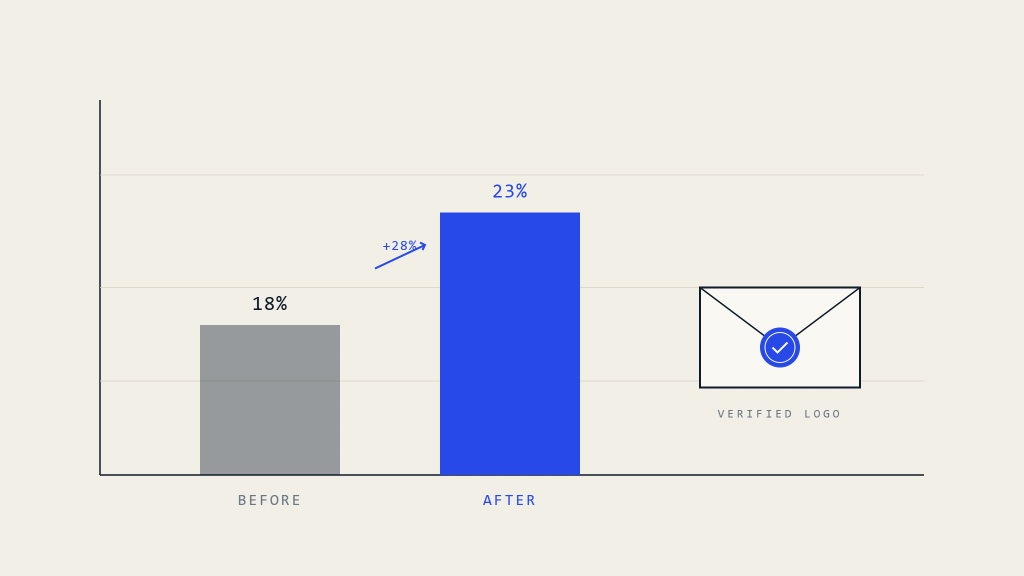
Research-backed analysis shows BIMI implementation increases email open rates by 15-25% through verified brand logos that enhance recipient trust and…

Compare DMARC forensic and aggregate reports to understand RUA vs RUF implementation, privacy implications, and use cases for effective email…
If not addressed, email authentication issues can trigger a domino effect that harms deliverability, damages your domain reputation, and reduces…

DMARC isn’t just about email security, it’s a powerful driver of marketing ROI. Businesses lose millions each year to phishing…

Struggling with low email deliverability? Uncover the common reasons your emails aren't reaching inboxes—like authentication failures, spam filters, and DNS…

Learn 7 essential steps to protect your organization from phishing attacks with comprehensive email security strategies and actionable prevention measures.
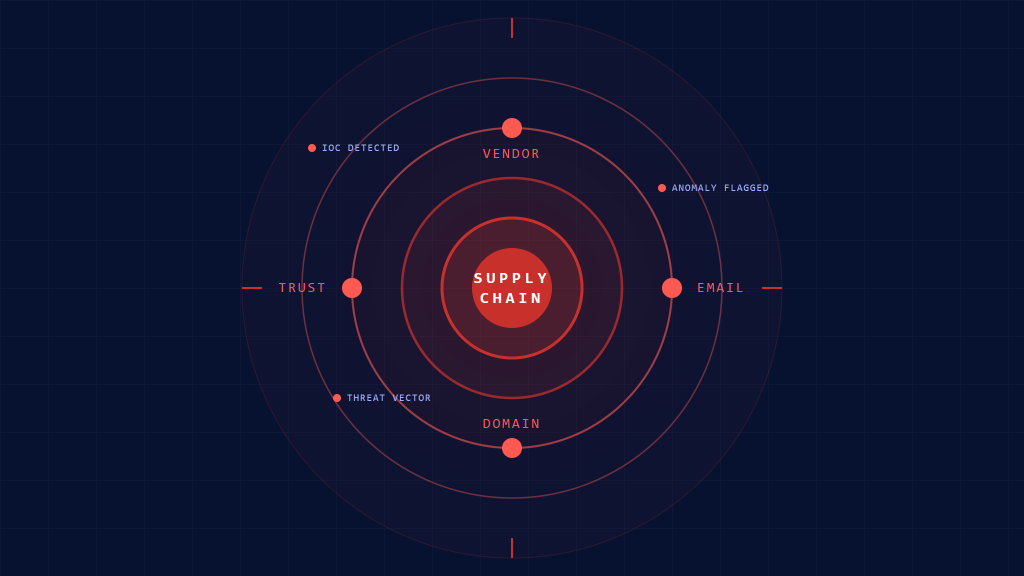
Essential indicators of compromise for detecting supply chain email threats. Complete checklist for identifying and responding to sophisticated vendor-based attacks.

The Louvre’s jewel heist exposed more than a security breach - it revealed a digital failure. Outdated systems, weak passwords,…
Complete checklist for implementing SOC 2 Type II email security controls. Essential authentication, encryption, and monitoring requirements for compliance certification.
Email authentication plays a critical role in helping businesses meet data privacy and compliance requirements. By implementing standards like SPF, DKIM, and DMARC, organizations can prevent email spoofing, reduce the risk of data breaches, and demonstrate proactive protection of customer datasupporting compliance with regulations such as GDPR and other global privacy laws.
This comprehensive guide explains the NIST Cybersecurity Framework and how it supports DMARC implementation to secure your email domain. Learn actionable strategies to defend against phishing, improve cyber resilience, and align with security best practices.
New Zealand’s Secure Government Email Framework sets a mandatory October 2025 deadline for implementing DMARC, SPF, DKIM, MTA-STS, and TLS-RPT. Whether you're a government agency or supplier, compliance is essential to avoid bounced emails, spoofing, and reputational risk.
Hands-on technical guides and notes on industry solutions from the team.
In enterprise environments, maintaining control of email security depends less on individual protocols and more on clear ownership and consistent management of authentication controls.
The newsroom feed — Skysnag platform releases and what's moving in email security, filed as it happens.
Discover how confidence-scored SPF enforcement with guided operator control centers revolutionizes DNS security management and email protection.
Skysnag releases its Look-Alike Domain Checker, empowering businesses to detect impersonation threats, prevent phishing, and protect their brand identity.
The Skysnag Integrations Center makes it easy for marketers to protect and improve email deliverability. With autonomous integrations to thousands of sending services, you can resolve issues faster and ensure…
Skysnag has launched a new blog dedicated to email authentication, security, and compliance. Discover expert insights, industry updates, and best practices on DMARC, SPF, and DKIM to help organizations strengthen…
Discover what MSSPs need from a DMARC solution in 2026, including email authentication standards, provider requirements, multi-tenant management, and high-margin revenue opportunities.
Cybercrime in 2026 is evolving into a patient, human-driven threat. From AI-generated phishing to identity leaks, attackers are using precision and psychology to exploit trust. Discover how businesses can strengthen…
As organizations expand, their digital footprint grows, so do their risks. Mismanaged domains and subdomains can become hidden entry points for phishing and impersonation attacks. Learn how consistent email authentication,…
BEC attacks exploit trust to bypass traditional defenses. Learn how to secure your domain with proactive email authentication that stops impersonation at the source.
A weekly dispatch for security leaders, MSPs, and deliverability engineers. Threat advisories, standards movement, and one piece of long-form analysis — edited by the Skysnag research group.
No marketing sequences. Unsubscribe in one click. Skysnag's privacy posture is SOC 2 Type II & GDPR-aligned.