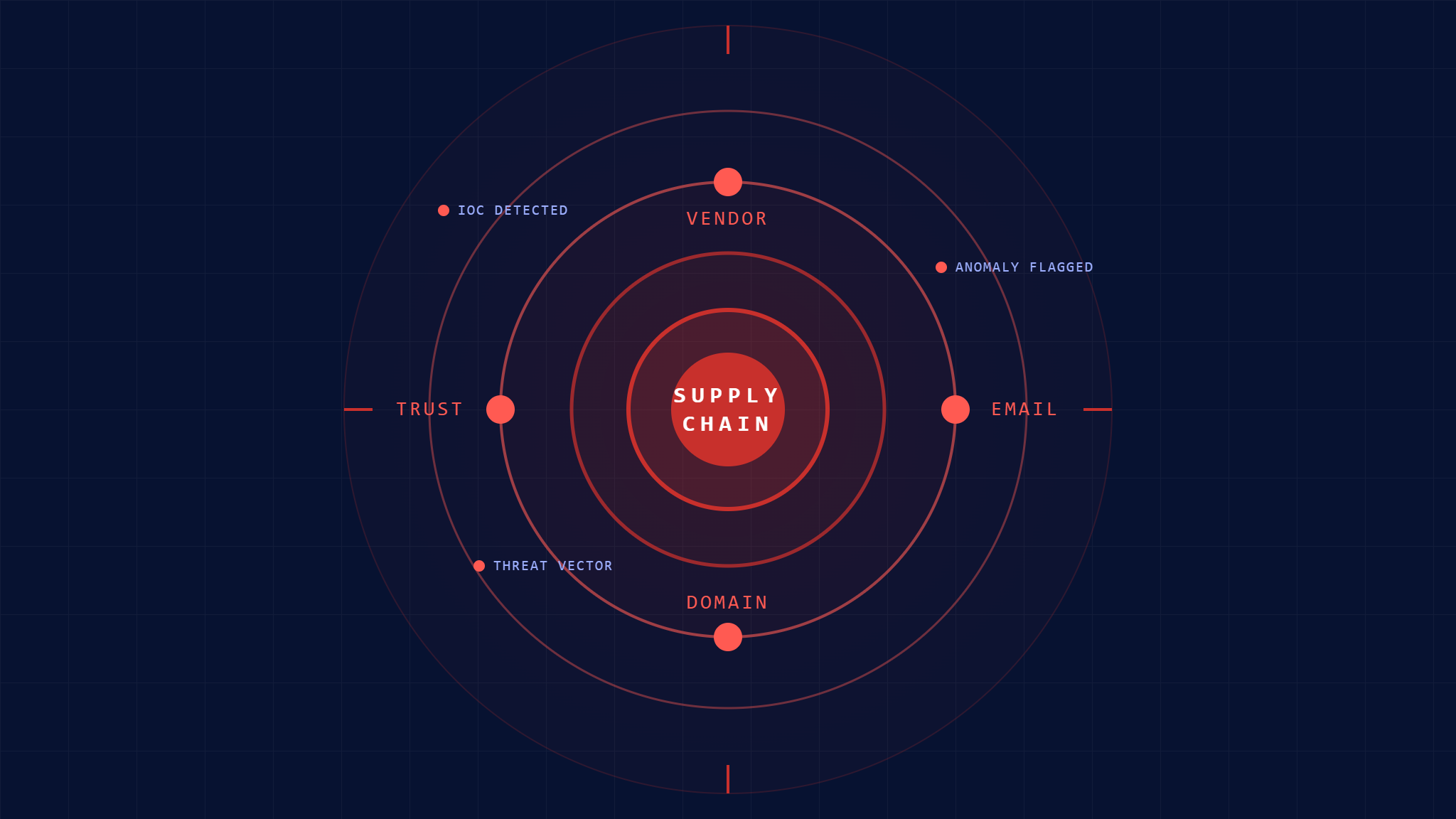
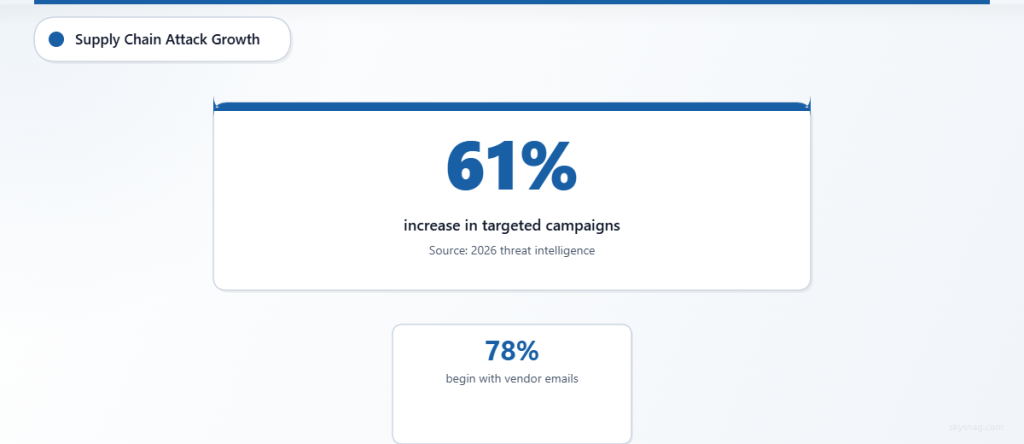
Supply chain email attacks have become the preferred weapon of sophisticated threat actors, with a staggering 61% increase in targeted campaigns observed throughout 2026. These attacks exploit trusted vendor relationships and compromised legitimate accounts to bypass traditional security controls, making them particularly dangerous for organizations of all sizes.
I. Understanding Supply Chain Email Attack Vectors
Supply chain email attacks leverage compromised vendor accounts, hijacked email threads, and spoofed trusted domains to infiltrate target organizations. Unlike standard phishing campaigns, these attacks exploit existing business relationships and communication patterns, making detection significantly more challenging.
Recent threat intelligence indicates that 78% of successful supply chain compromises begin with a seemingly legitimate email from a known vendor or partner, according to cybersecurity research from leading threat intelligence firms. These attacks often remain undetected for months, allowing attackers to establish persistent access and move laterally through interconnected networks.
II. Assessment: Critical IoCs to Monitor
Email Header Anomalies
Monitor these specific indicators in email headers that suggest compromise:
SPF, DKIM, and DMARC Failures
- Sudden SPF failures from previously legitimate senders
- DKIM signature mismatches on vendor communications
- DMARC policy violations from trusted domains
- Authentication bypasses using subdomain spoofing
Routing and Timestamp Irregularities
- Unusual mail server hops in message routing
- Timestamp discrepancies suggesting relay through compromised infrastructure
- Modified or missing message tracking headers
- Suspicious originating IP addresses from vendor domains
Content and Communication Pattern Changes
Language and Format Deviations
- Subtle changes in communication style or terminology
- Unexpected urgency in routine vendor communications
- Grammar or spelling inconsistencies from professional contacts
- Unusual attachment types or file naming conventions
Business Process Anomalies
- Requests for process changes outside normal approval channels
- Unexpected payment redirection or banking detail updates
- Unusual access requests or credential sharing attempts
- Off-schedule or unplanned system maintenance notifications
Technical Indicators
Attachment and Link Analysis
- Executables disguised with double extensions
- Password-protected archives from unexpected sources
- Shortened URLs or suspicious redirect chains
- Documents with embedded macros from non-macro users
Network and Infrastructure Signals
- Communications from backup or disaster recovery domains
- Emails originating from recently registered lookalike domains
- Traffic routing through suspicious geographic locations
- SSL certificate anomalies on vendor websites or portals
III. Actions: Immediate Response Protocols
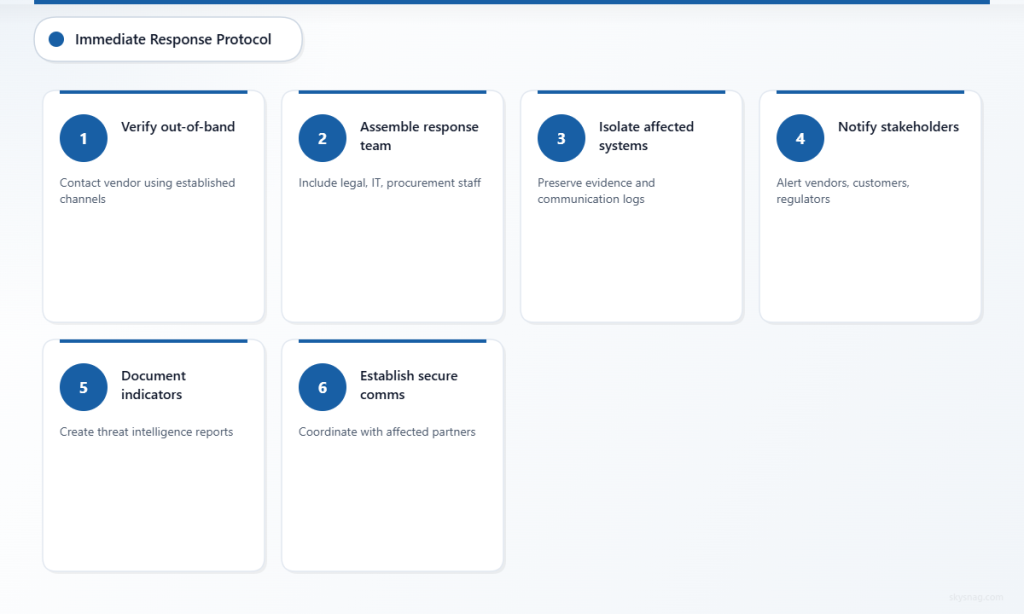
Verification and Validation
Implement out-of-band verification for any suspicious vendor communications. Contact vendors directly using previously established phone numbers or communication channels to confirm legitimate requests. Never use contact information provided within suspicious emails for verification purposes.
Create a rapid response team protocol that includes legal, IT security, procurement, and business relationship managers. This cross-functional approach ensures comprehensive evaluation of potential supply chain compromises while maintaining business continuity.
Containment and Investigation
Immediately isolate affected systems and accounts showing compromise indicators. Preserve email evidence and communication logs for forensic analysis. Notify relevant stakeholders including vendors, customers, and regulatory bodies as required by compliance frameworks.
Document all indicators observed and create threat intelligence reports for sharing with industry peers and security communities. This collaborative approach strengthens the broader ecosystem against similar attack patterns.
Communication and Coordination
Establish secure communication channels with affected vendors and partners. Coordinate incident response activities to prevent attackers from adapting their tactics across multiple organizations within the same supply chain.
Implement temporary additional verification procedures for all vendor communications until normal trust relationships can be reestablished and validated.
IV. Automate: Technology Solutions
Email Security Automation
Deploy advanced email security solutions capable of analyzing communication patterns and detecting subtle changes in vendor correspondence. Modern email security platforms use machine learning to identify anomalous communication patterns that human analysts might miss.
Skysnag Comply provides comprehensive email authentication monitoring and DMARC policy enforcement specifically designed to detect and prevent supply chain email attacks. The platform automatically identifies authentication failures and suspicious communication patterns that indicate potential vendor account compromise.
Integration and Orchestration
Integrate threat intelligence feeds with security information and event management (SIEM) platforms to automatically correlate supply chain attack indicators across multiple data sources. This integration enables rapid identification of coordinated attack campaigns targeting multiple organizations within connected supply chains.
Implement automated incident response workflows that trigger containment procedures when specific IoC thresholds are met. These workflows should include stakeholder notifications, evidence preservation, and coordination with affected vendors.
Continuous Monitoring
Establish baseline communication patterns for all vendor relationships and implement anomaly detection algorithms to identify deviations. Monitor for changes in email authentication postures of trusted domains and vendors.
Deploy real-time monitoring for newly registered domains that closely resemble trusted vendor domains, enabling proactive identification of potential spoofing infrastructure before attacks commence.
V. Advanced Detection Strategies
Behavioral Analytics
Implement user and entity behavior analytics (UEBA) solutions to establish normal communication patterns with vendors and detect subtle deviations that might indicate account compromise. These systems learn typical interaction patterns and flag unusual requests or communication timing.
Monitor for changes in attachment patterns, link sharing behaviors, and communication frequency that might indicate compromised accounts or social engineering attempts.
Threat Intelligence Integration
Maintain current threat intelligence feeds focused specifically on supply chain attack techniques and known compromised vendor infrastructures. Integrate these feeds with email security solutions to proactively block communications from known malicious infrastructure.
Participate in industry-specific threat intelligence sharing programs to receive early warnings about supply chain attacks targeting similar organizations or industry verticals.
VI. Key Takeaways
Supply chain email attacks represent a critical threat requiring comprehensive detection and response capabilities. Organizations must implement layered security controls that combine technology solutions with human verification processes to effectively defend against these sophisticated attacks.
Regular assessment of vendor communication patterns, implementation of robust email authentication protocols, and deployment of automated monitoring solutions provide the foundation for effective supply chain attack prevention. The integration of threat intelligence and behavioral analytics enhances detection capabilities while reducing false positive rates.
Success in defending against supply chain email attacks requires ongoing vigilance, regular security awareness training, and collaborative defense approaches with vendors and industry peers. Organizations that implement comprehensive IoC monitoring and automated response procedures significantly reduce their exposure to these evolving threats.