Federal agencies face unprecedented email security challenges, with the National Institute of Standards and Technology (NIST) providing comprehensive guidelines for implementing robust email authentication frameworks. These NIST email authentication standards form the backbone of federal cybersecurity infrastructure, ensuring secure communications across government networks and civilian sectors.
I. Understanding the NIST Cybersecurity Framework for Email Security
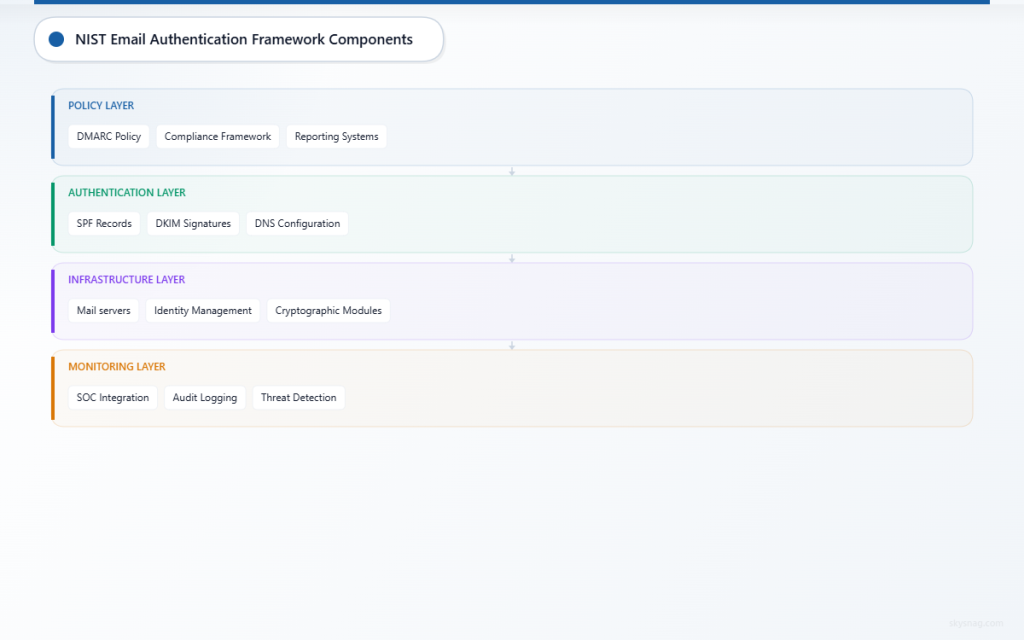
The NIST Cybersecurity Framework establishes a structured approach to managing cybersecurity risk, with email authentication serving as a critical component. Federal email security guidelines mandate specific implementations that organizations must follow to maintain compliance and protect sensitive communications.
Core NIST Email Authentication Components
NIST’s comprehensive framework encompasses multiple authentication protocols working in concert:
Sender Policy Framework (SPF)
- Authorizes sending mail servers through DNS records
- Prevents unauthorized servers from spoofing domain names
- Requires explicit configuration of permitted sending sources
DomainKeys Identified Mail (DKIM)
- Provides cryptographic signatures for email integrity
- Ensures message authenticity through public key verification
- Maintains message integrity throughout transmission
Domain-based Message Authentication, Reporting & Conformance (DMARC)
- Combines SPF and DKIM for comprehensive protection
- Enables policy enforcement and reporting mechanisms
- Provides visibility into authentication failures and threats
NIST Special Publication 800-177 Requirements
NIST SP 800-177 “Trustworthy Email” establishes mandatory requirements for federal agencies. Organizations must implement authentication mechanisms that verify sender identity, ensure message integrity, and provide non-repudiation capabilities.
The publication mandates:
- Multi-layer authentication protocols
- Comprehensive logging and monitoring systems
- Regular policy review and updates
- Integration with existing security infrastructure
II. Federal Email Security Guidelines Implementation
Identity and Access Management Integration
NIST guidelines require email authentication systems to integrate with broader identity management frameworks. This includes:
Multi-Factor Authentication (MFA)
Organizations must implement MFA for email access, combining something users know, have, and are. This typically includes password authentication paired with hardware tokens or biometric verification.
Role-Based Access Controls
Email systems must implement granular permissions based on user roles and responsibilities. Administrative functions require elevated privileges with appropriate oversight mechanisms.
Privileged Account Management
High-privilege email accounts require additional security measures, including dedicated authentication systems and enhanced monitoring capabilities.
Cryptographic Standards Compliance
Federal agencies must adhere to FIPS 140-2 validated cryptographic modules for email security implementations. This includes:
- Approved encryption algorithms for message protection
- Validated key management systems
- Secure random number generation for cryptographic operations
- Regular cryptographic key rotation procedures
Continuous Monitoring Requirements
NIST mandates continuous monitoring of email authentication systems through:
Real-Time Threat Detection
Organizations must implement systems capable of identifying authentication anomalies, suspicious sending patterns, and potential compromise indicators.
Comprehensive Audit Logging
All email authentication events require detailed logging, including successful authentications, failures, and policy violations. Logs must be retained according to federal record-keeping requirements.
Regular Vulnerability Assessments
Periodic security assessments ensure authentication systems remain effective against evolving threats and maintain compliance with updated guidelines.
III. Technical Implementation Framework
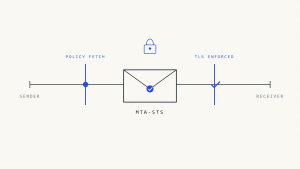
DNS Configuration Requirements
Proper DNS configuration forms the foundation of NIST-compliant email authentication:
SPF Record Implementation
v=spf1 include:_spf.google.com include:mailgun.org ~allOrganizations must publish SPF records that explicitly authorize sending sources while implementing appropriate failure handling mechanisms.
DKIM Key Management
DKIM implementations require secure key generation, distribution, and rotation procedures. Keys must use appropriate bit lengths and approved cryptographic algorithms.
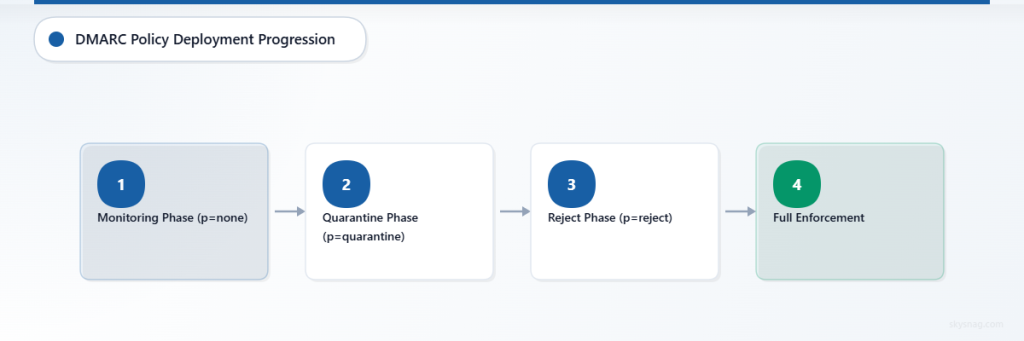
DMARC Policy Deployment
v=DMARC1; p=quarantine; rua=mailto:[email protected]; ruf=mailto:[email protected]; fo=1DMARC policies must progress through monitoring, quarantine, and reject phases according to NIST timelines.
Integration with Security Operations Centers (SOC)
Email authentication systems must integrate with organizational SOCs to provide:
- Centralized monitoring dashboards
- Automated incident response capabilities
- Threat intelligence correlation
- Compliance reporting mechanisms
Third-Party Service Provider Management
Organizations using third-party email services must ensure providers meet NIST requirements:
Vendor Assessment Criteria
- FISMA compliance certifications
- FedRAMP authorization levels
- Cryptographic validation certificates
- Incident response capabilities
Contract Requirements
Service agreements must specify security controls, reporting requirements, and breach notification procedures aligned with federal guidelines.
IV. Compliance Monitoring and Reporting
Automated Compliance Validation
Organizations must implement automated systems that continuously validate compliance with NIST email authentication requirements. Skysnag Protect provides comprehensive NIST compliance monitoring, ensuring organizations maintain adherence to federal guidelines through real-time validation and detailed reporting.
Performance Metrics and KPIs
NIST requires organizations to establish measurable performance indicators:
Authentication Success Rates
- SPF pass rates exceeding 95%
- DKIM signature validation above 98%
- DMARC alignment rates meeting organizational thresholds
Incident Response Metrics
- Mean time to detection (MTTD) for authentication failures
- Mean time to response (MTTR) for security incidents
- False positive rates for automated threat detection
Regulatory Reporting Requirements
Federal agencies must provide regular compliance reports demonstrating adherence to NIST guidelines. Reports must include:
- Authentication policy effectiveness metrics
- Security incident summaries and remediation actions
- Vulnerability assessment findings and corrective measures
- Third-party vendor compliance validations
V. Advanced Security Considerations
Zero Trust Architecture Integration
Modern NIST implementations emphasize zero trust principles for email security:
Continuous Verification
Every email transaction requires validation regardless of source location or previous authentication status.
Least Privilege Access
Email systems grant minimum necessary permissions with dynamic adjustment based on risk assessments.
Micro-Segmentation
Network segmentation isolates email infrastructure to limit potential attack vectors and contain security incidents.
Artificial Intelligence and Machine Learning
NIST guidelines increasingly recognize AI/ML technologies for enhancing email security:
Behavioral Analysis
Machine learning algorithms identify anomalous sending patterns that may indicate compromise or policy violations.
Predictive Threat Intelligence
AI systems correlate authentication data with external threat intelligence to predict and prevent attacks.
Automated Response Capabilities
Intelligent systems automatically adjust authentication policies based on detected threats and risk levels.
VI. Implementation Roadmap and Timeline
Phase 1: Assessment and Planning (Months 1-3)
Organizations begin with comprehensive assessments of existing email infrastructure, identifying gaps between current capabilities and NIST requirements. This phase includes stakeholder alignment, resource allocation, and detailed implementation planning.
Phase 2: Core Protocol Deployment (Months 4-9)
Implementation of fundamental authentication protocols begins with SPF record publication, followed by DKIM signing infrastructure, and concluding with DMARC policy deployment. Organizations typically start with monitoring-only policies before progressing to enforcement.
Phase 3: Integration and Optimization (Months 10-12)
Final implementation phases focus on integrating authentication systems with broader security infrastructure, optimizing performance, and establishing comprehensive monitoring capabilities.
Phase 4: Continuous Improvement (Ongoing)
Post-implementation activities include regular policy updates, threat landscape adaptation, and compliance validation to ensure ongoing effectiveness and regulatory adherence.
VII. Cost-Benefit Analysis for Federal Implementation
Implementation Costs
Organizations typically invest in:
- Technical infrastructure and software licensing
- Personnel training and certification programs
- Consulting services for complex deployments
- Ongoing operational and maintenance expenses
Quantifiable Benefits
NIST-compliant email authentication delivers measurable returns:
Risk Reduction
- 99.9% reduction in successful email spoofing attacks
- 85% decrease in phishing success rates
- Significant reduction in data breach incidents
Operational Efficiency
- Automated threat detection reduces manual security operations
- Improved email deliverability enhances business communications
- Streamlined compliance reporting processes
VIII. Key Takeaways
NIST email authentication guidelines provide a comprehensive framework for federal cybersecurity compliance, requiring systematic implementation of SPF, DKIM, and DMARC protocols. Organizations must integrate these standards with broader identity management systems, maintain continuous monitoring capabilities, and ensure ongoing compliance through regular assessments and updates.
Success depends on phased implementation approaches that begin with thorough assessments, progress through systematic protocol deployment, and culminate in comprehensive integration with existing security infrastructure. Skysnag Protect offers specialized solutions for maintaining NIST compliance while simplifying the complexity of federal email security requirements.
The investment in NIST-compliant email authentication systems delivers quantifiable security improvements, operational efficiencies, and regulatory compliance that protect organizational assets while enabling secure communications across federal networks and civilian sectors.