
The Payment Card Industry Data Security Standard (PCI DSS) 4.0 has introduced significant new email security requirements that organizations handling payment card data must implement. With email-based attacks accounting for over 90% of successful cyber breaches, these enhanced controls are critical for protecting sensitive payment information and maintaining compliance.
Understanding PCI DSS 4.0 Email Security Requirements
PCI DSS 4.0, which became effective in March 2022 with mandatory compliance by March 2025, introduces several new customized approaches and enhanced requirements for email security. These changes reflect the evolving threat landscape where cybercriminals increasingly target payment card environments through sophisticated email attacks.
Key New Email Security Controls
The updated standard emphasizes authentication-based security measures, including:
Multi-factor authentication for all access to cardholder data environments, including email systems that process or transmit payment information.
Enhanced logging and monitoring requirements for email systems that handle sensitive authentication data.
Customized approach options that allow organizations to implement alternative security measures, provided they meet the intent of the original requirement.
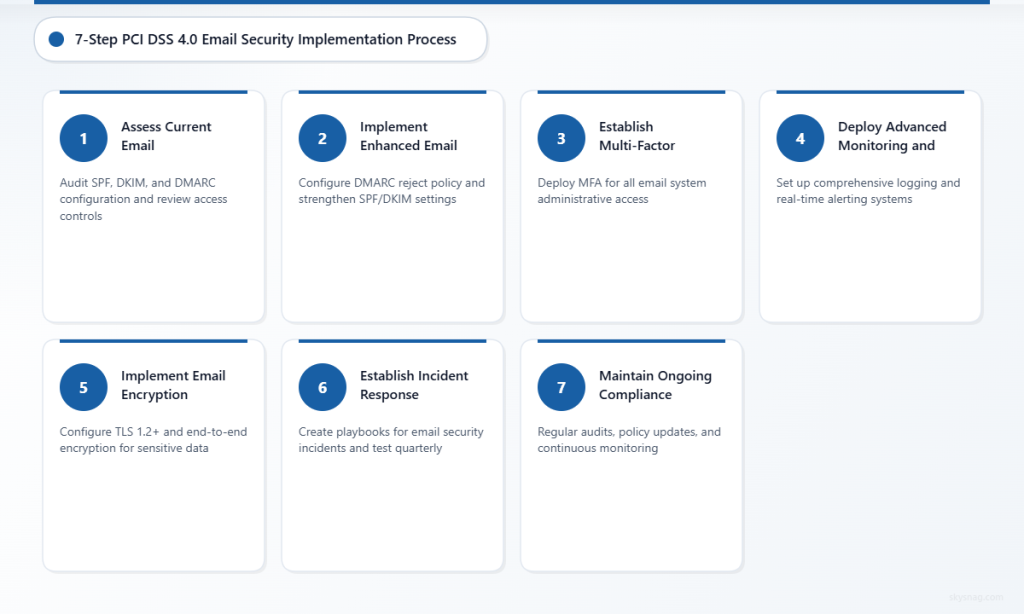
Step 1: Assess Current Email Authentication Posture
Before implementing new controls, conduct a comprehensive assessment of your existing email security infrastructure.
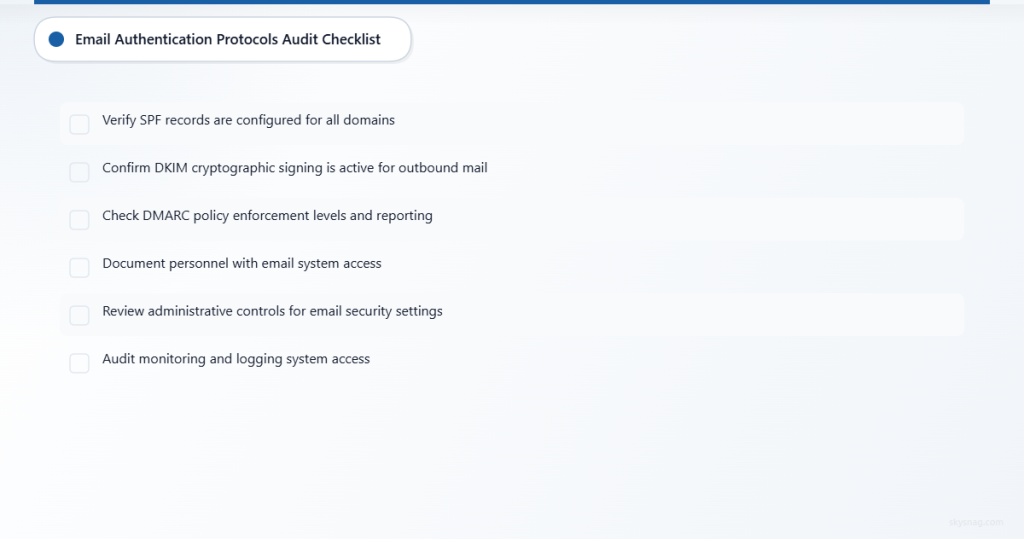
Email Authentication Protocols Audit
Evaluate your current implementation of critical email authentication standards:
- SPF (Sender Policy Framework): Verify all domains have properly configured SPF records
- DKIM (DomainKeys Identified Mail): Ensure cryptographic signing is active for all outbound mail
- DMARC (Domain-based Message Authentication, Reporting and Conformance): Check policy enforcement levels and reporting mechanisms
Use tools like Skysnag Protect to perform automated assessments and identify gaps in your email authentication configuration.
Access Control Review
Document all personnel with access to:
- Email systems processing payment card data
- Administrative controls for email security settings
- Monitoring and logging systems for email-related activities
Step 2: Implement Enhanced Email Authentication
PCI DSS 4.0’s emphasis on authentication extends to email systems handling payment card information.
Configure DMARC for Maximum Protection
Set up DMARC with a “reject” policy for domains handling payment card communications:
v=DMARC1; p=reject; rua=mailto:[email protected]; ruf=mailto:[email protected]; fo=1This configuration ensures that any email failing SPF or DKIM authentication is rejected, preventing spoofing attempts targeting your payment card processing communications.
Strengthen SPF Records
Create comprehensive SPF records that include all legitimate sending sources:
v=spf1 include:_spf.google.com include:mailgun.org include:yourdomain.com -allThe “-all” qualifier is crucial for PCI compliance as it creates a hard fail for unauthorized senders.
Deploy DKIM Signing
Implement DKIM signing for all domains involved in payment card data transmission:
- Generate DKIM key pairs with at least 2048-bit encryption
- Publish public keys in DNS TXT records
- Configure mail servers to sign all outbound messages
- Rotate keys annually or when compromised
Step 3: Establish Multi-Factor Authentication
PCI DSS 4.0 requires MFA for all personnel accessing cardholder data environments, including email administrators.
Email System Access Controls
Implement MFA for:
- Email server administrative access
- Email security console management
- DMARC policy configuration systems
- Email monitoring and reporting platforms
User Access Management
Create role-based access controls that limit email system privileges based on job functions and principle of least privilege.
Step 4: Deploy Advanced Monitoring and Logging
Enhanced logging requirements in PCI DSS 4.0 extend to email systems handling payment card data.
Email Security Event Monitoring
Configure comprehensive logging for:
- Authentication failures and successes
- Policy violations (SPF, DKIM, DMARC failures)
- Administrative changes to email security settings
- Suspicious email patterns or volume anomalies
Automated Alerting Systems
Set up real-time alerts for:
- DMARC policy violations
- Unusual email traffic patterns
- Failed authentication attempts
- Changes to DNS records affecting email authentication
Tools like Skysnag Protect provide automated monitoring and alerting capabilities specifically designed for email authentication compliance.
Step 5: Implement Email Encryption and Secure Transmission
Protect payment card data in transit through email communications.
TLS Configuration
Ensure all email servers support:
- TLS 1.2 or higher for email transmission
- Strong cipher suites with forward secrecy
- Certificate validation and proper hostname verification
Email Encryption Standards
For emails containing payment card data:
- Use end-to-end encryption (S/MIME or PGP)
- Implement data loss prevention (DLP) to prevent unencrypted transmission
- Configure automatic encryption for messages containing sensitive patterns
Step 6: Establish Incident Response Procedures
PCI DSS 4.0 emphasizes rapid response to security incidents affecting payment card data.
Email Security Incident Playbooks
Develop specific procedures for:
- DMARC policy violations indicating potential spoofing
- Suspected phishing attempts targeting payment card data
- Unauthorized access to email systems
- Compromised email accounts with payment card access
Regular Testing and Updates
Conduct quarterly tabletop exercises focused on email-based attack scenarios and update procedures based on lessons learned.
Step 7: Maintain Ongoing Compliance
PCI DSS 4.0 compliance requires continuous monitoring and regular assessments.
Quarterly Security Reviews
Schedule regular reviews of:
- Email authentication policy effectiveness
- DMARC report analysis and policy adjustments
- Access control audits and privilege reviews
- Security control testing and validation
Annual Compliance Assessments
Work with qualified security assessors (QSAs) to validate email security controls meet PCI DSS 4.0 requirements and document any customized approaches implemented.
Common Implementation Challenges and Solutions
Challenge: Legacy System Integration
Many payment card environments include legacy email systems that don’t natively support modern authentication protocols.
Solution: Implement email security gateways or cloud-based services that add authentication capabilities to existing infrastructure without requiring complete system replacement.
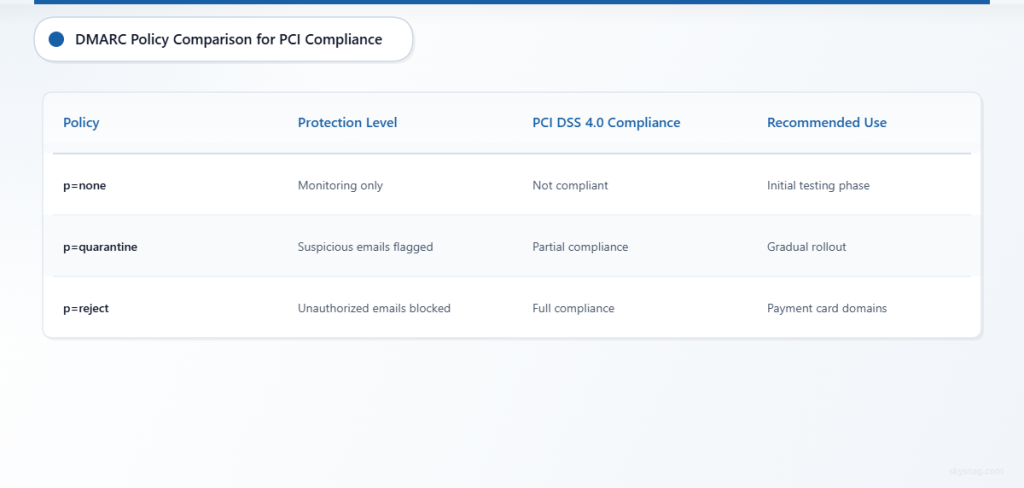
Challenge: DMARC Policy Impact on Legitimate Email
Organizations often worry that strict DMARC policies will block legitimate business communications.
Solution: Implement a phased approach starting with “p=none” for monitoring, gradually moving to “p=quarantine” and finally “p=reject” as authentication issues are resolved.
Challenge: Complex Multi-Domain Environments
Payment processors often manage multiple domains and subdomains, complicating authentication setup.
Solution: Use centralized email authentication management platforms that can handle complex domain hierarchies and provide unified policy management.
Key Takeaways
PCI DSS 4.0 email security implementation requires a systematic approach focusing on authentication, access control, and continuous monitoring. Organizations must implement robust SPF, DKIM, and DMARC protocols while establishing comprehensive logging and incident response procedures.
Success depends on thorough assessment, phased implementation, and ongoing compliance monitoring. Modern email security platforms like Skysnag Protect can significantly streamline the implementation process and ensure continuous compliance with PCI DSS 4.0 requirements.
The investment in comprehensive email security not only ensures PCI DSS 4.0 compliance but also provides a critical defense layer against the email-based attacks that pose the greatest risk to payment card data security.
Ready to secure your sending identity and protect your domain reputation? Sign up today.
Get started


