SOC 2 Type II compliance demands security controls that protect sensitive data throughout its lifecycle. Email systems present a particular challenge they’re both essential for data transmission and frequent attack vectors. For compliance teams working toward SOC 2 certification, email security controls must align with the Trust Service Criteria while addressing real operational risks.
This checklist helps IT and compliance teams implement email security controls that strengthen SOC 2 programs. The approach focuses on practical steps that auditors recognize and security teams can actually maintain.
I. Understanding SOC 2 Email Security Requirements

SOC 2 evaluates controls across five Trust Service Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. The framework doesn’t mandate specific email technologies, but it does require controls that prevent unauthorized access and maintain data integrity.
Email authentication controls DMARC, SPF, and DKIM directly support SOC 2 objectives. They prevent domain spoofing and protect data transmission integrity, demonstrating your commitment to the Security criterion by reducing phishing risks and blocking unauthorized communications.
The FBI’s Internet Crime Report shows business email compromise caused $2.9 billion in losses. Most organizations pursuing SOC 2 certification include email authentication in their evidence portfolio, but many implement these controls incorrectly or incompletely.
II. Assessment: Current Email Security Posture
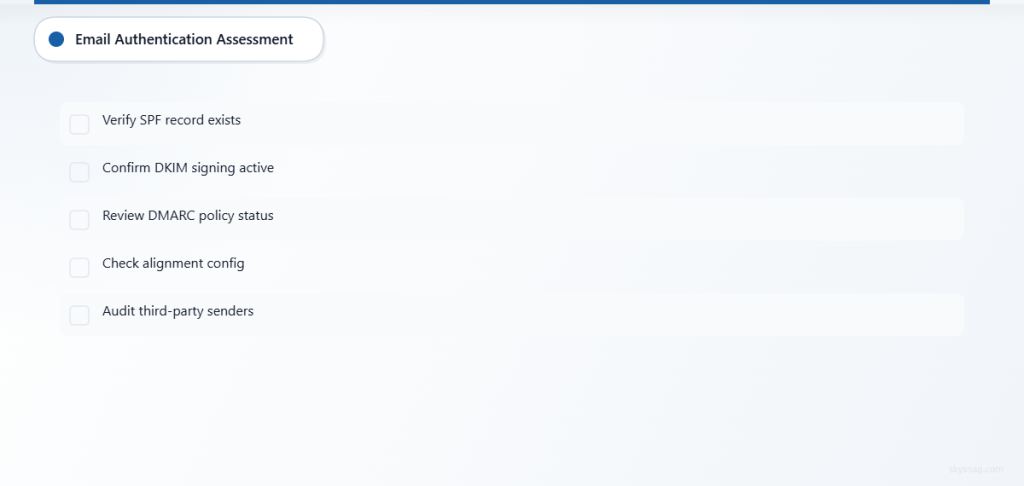
Email Authentication Status
- [ ] SPF Record Analysis: Verify current SPF record exists and includes all authorized sending sources
- [ ] DKIM Implementation: Confirm DKIM signing is active for all outbound email domains
- [ ] DMARC Policy Review: Assess current DMARC policy status (none, quarantine, or reject)
- [ ] Authentication Alignment: Evaluate SPF and DKIM alignment with DMARC requirements
- [ ] Third-Party Sender Audit: Identify all legitimate third-party email services requiring authorization
Security Controls Evaluation
- [ ] Access Controls: Document email system administrator access and approval processes
- [ ] Encryption Status: Verify TLS encryption for email transmission and at-rest protection
- [ ] Monitoring Capabilities: Assess current email security monitoring and alerting systems
- [ ] Incident Response: Review email-related security incident procedures and documentation
- [ ] Data Classification: Evaluate how sensitive data handling aligns with email usage policies
Compliance Documentation
- [ ] Policy Documentation: Review email security policies for SOC 2 alignment
- [ ] Control Evidence: Inventory existing email security control documentation
- [ ] Vendor Management: Assess email service provider SOC 2 compliance status
- [ ] Risk Assessment: Document email-related risks and mitigation strategies
- [ ] Training Records: Verify security awareness training includes email security components
III. Actions: Implementing SOC 2 Email Security Controls
Email Authentication Implementation
SPF Configuration
- [ ] Create SPF record including all authorized IP addresses and domains
- [ ] Implement SPF “~all” or “-all” mechanism for unauthorized sender rejection
- [ ] Document SPF record changes and maintain authorized sender inventory
- [ ] Test SPF validation using email authentication testing tools
- [ ] Establish SPF record review and update procedures
Most organizations underestimate the complexity of maintaining accurate SPF records. Third-party services frequently change IP addresses without notice, breaking authentication. Build regular review processes into your change management procedures.
DKIM Deployment
- [ ] Generate DKIM key pairs for all sending domains
- [ ] Configure DKIM signing on email servers or service providers
- [ ] Publish DKIM public keys in DNS TXT records
- [ ] Implement key rotation procedures for ongoing security
- [ ] Monitor DKIM signature validation rates and failures
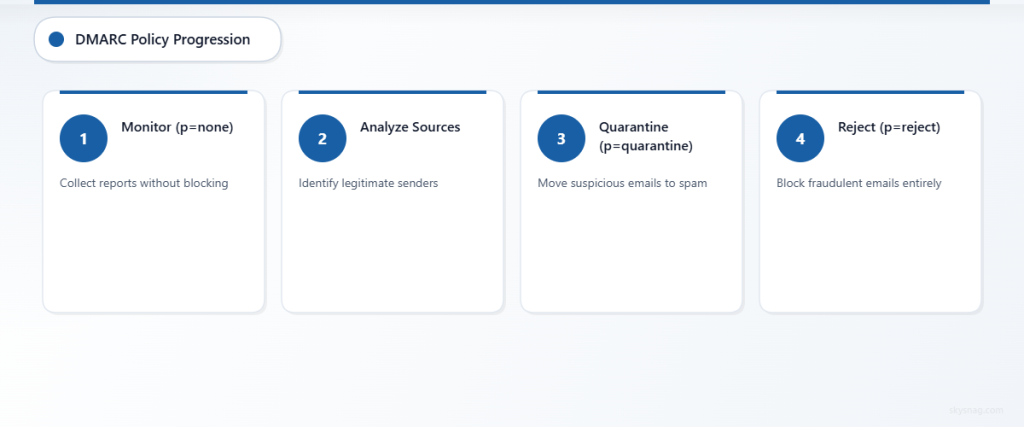
DMARC Policy Enforcement
- [ ] Start with DMARC policy “p=none” for initial monitoring
- [ ] Analyze DMARC reports to identify legitimate and fraudulent email sources
- [ ] Progress to “p=quarantine” after validating legitimate email flows
- [ ] Implement “p=reject” policy for maximum protection when ready
- [ ] Configure aggregate and forensic reporting for ongoing monitoring
DMARC implementation often stalls at the monitoring phase. Organizations collect reports but never analyze them systematically. Without this analysis, you can’t safely move to enforcement policies that actually block fraudulent emails.
Access Control and Monitoring
Administrative Controls
- [ ] Implement multi-factor authentication for all email system administrators
- [ ] Document role-based access controls for email system management
- [ ] Establish approval workflows for email system configuration changes
- [ ] Create audit logs for all administrative access and modifications
- [ ] Implement regular access reviews and deprovisioning procedures
Security Monitoring
- [ ] Deploy email security monitoring tools for threat detection
- [ ] Configure alerting for suspicious email patterns and authentication failures
- [ ] Implement automated responses to detected email security incidents
- [ ] Establish security information and event management (SIEM) integration
- [ ] Create dashboards for email security metrics and compliance reporting
Documentation and Policies
Policy Development
- [ ] Create or update email security policies aligned with SOC 2 requirements
- [ ] Document acceptable use policies for email systems and data handling
- [ ] Establish incident response procedures specific to email security events
- [ ] Create vendor management procedures for email service providers
- [ ] Develop data retention and deletion policies for email communications
Evidence Collection
- [ ] Implement automated collection of email security control evidence
- [ ] Create regular reporting on email authentication effectiveness
- [ ] Document security control testing procedures and results
- [ ] Maintain inventory of email security tools and configurations
- [ ] Establish control effectiveness measurement and reporting
Auditors want to see evidence that controls actually work, not just that they exist. Many organizations can demonstrate they have DMARC policies but struggle to show those policies effectively block fraudulent emails or that they monitor authentication failures consistently.
IV. Automate: Streamlining Email Security Management
Continuous Monitoring Implementation
Email security requires automated monitoring and response capabilities. Manual processes don’t scale, and auditors expect continuous monitoring rather than periodic checks.
Implement systems that track email authentication performance, detect policy violations, and generate compliance evidence automatically. Configure alerting for authentication failures, new unauthorized senders, and policy violations.
Skysnag Comply provides automated DMARC monitoring and reporting capabilities that support SOC 2 compliance evidence requirements. The platform tracks email authentication metrics, identifies policy violations, and generates detailed reports suitable for auditor review.
This proactive approach demonstrates the continuous monitoring capabilities that auditors expect in mature SOC 2 programs.
Compliance Evidence Automation
Establish automated collection and organization of email security compliance evidence. This includes authentication reports, policy compliance metrics, incident response documentation, and control effectiveness measurements.
Implement regular automated testing of email authentication controls to demonstrate ongoing effectiveness. Document these tests and results as evidence of continuous security control monitoring.
Create automated dashboards that provide real-time visibility into email security posture and SOC 2 compliance metrics. These dashboards support both operational security management and auditor evidence requests.
V. Key Takeaways
SOC 2 email security controls require implementation across authentication, access control, monitoring, and documentation. Success depends on systematic assessment, structured implementation, and continuous automation of security controls.
Email authentication through SPF, DKIM, and DMARC provides foundational protection that supports SOC 2 Security criterion objectives. However, implementation quality matters more than simply having these protocols in place. Controls must actually prevent domain spoofing and protect data transmission integrity.
Automated monitoring and evidence collection streamline SOC 2 compliance while improving actual security posture. Organizations that implement email security controls systematically position themselves for successful SOC 2 audits while reducing real-world security risks.
Regular review and updating of email security controls ensures ongoing effectiveness and compliance alignment. This systematic approach supports SOC 2 certification and broader organizational security objectives.
Ready to strengthen your SOC 2 email security posture? Skysnag Comply provides email authentication monitoring and compliance reporting to support your SOC 2 certification efforts.








