MTA-STS vs DANE: Complete Email Security Comparison for Modern Organizations
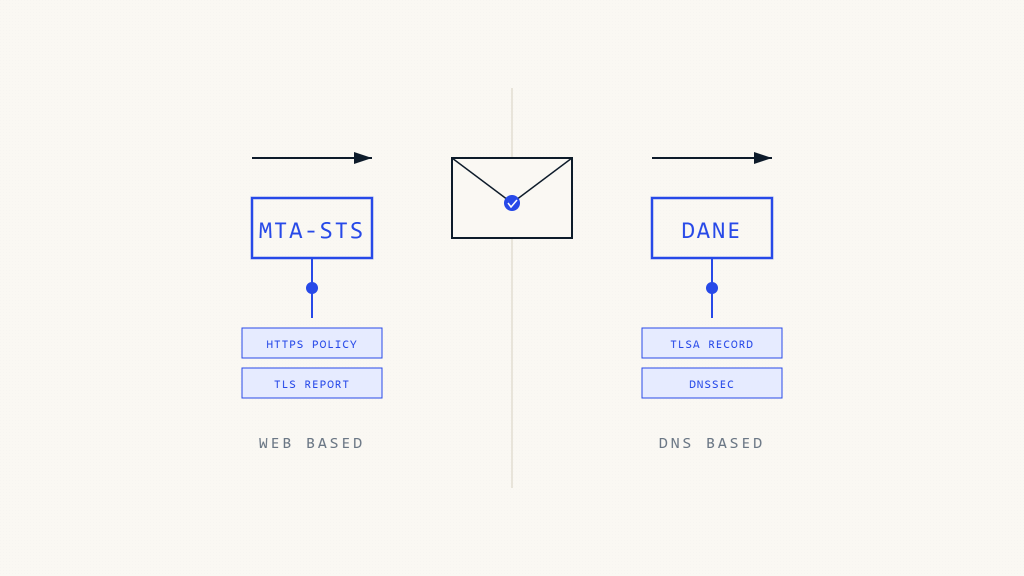
Email transport security remains a critical battleground in cybersecurity, with organizations facing increasingly sophisticated attacks targeting SMTP communications. Two prominent standards have emerged to secure email in transit: MTA-STS (Mail Transfer Agent Strict Transport Security) and DANE (DNS-based Authentication of Named Entities). Understanding the differences between these protocols is essential for implementing effective email security strategies.
Both MTA-STS and DANE address fundamental vulnerabilities in email transmission, but they take distinctly different approaches to solving transport layer security challenges. This comprehensive comparison examines their technical implementations, security benefits, and practical deployment considerations to help organizations choose the most appropriate solution for their email infrastructure.
Understanding MTA-STS: HTTPS-Based Email Security
MTA-STS leverages familiar web security principles to protect email communications. Introduced as RFC 8461, this standard uses HTTPS to publish security policies that dictate how email should be transmitted to a domain.
How MTA-STS Works
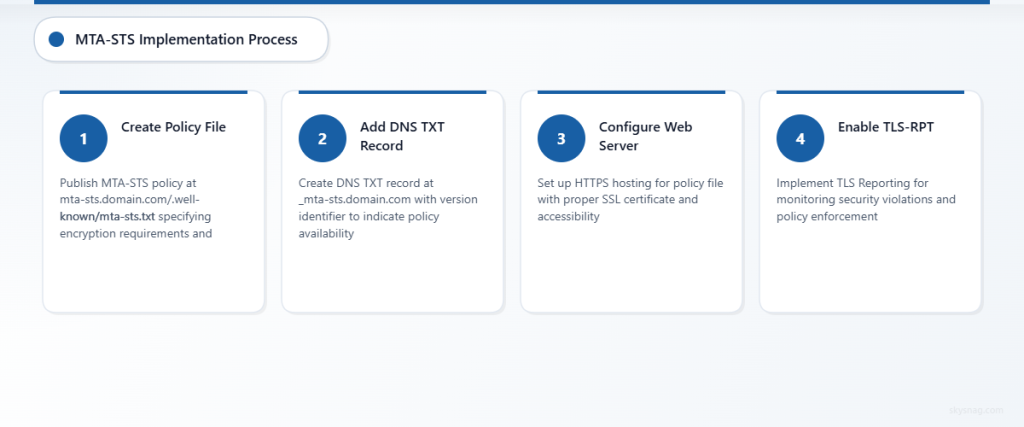
The MTA-STS implementation process involves several key components:
Policy Publication: Organizations publish MTA-STS policies via HTTPS at a well-known URL (mta-sts.domain.com/.well-known/mta-sts.txt). This policy file specifies which mail servers are authorized to receive email and mandates encryption requirements.
DNS TXT Record: A simple DNS TXT record at _mta-sts.domain.com indicates policy availability and includes a version identifier for policy updates.
Policy Enforcement: Sending mail servers retrieve and cache the MTA-STS policy, then enforce the specified security requirements when delivering email to the domain.
Key MTA-STS Features
- Encryption Enforcement: Requires TLS encryption for all email communications
- Certificate Validation: Mandates proper SSL/TLS certificate verification
- Authorized MX Records: Specifies which mail servers can legitimately receive email
- Policy Flexibility: Supports testing and enforcement modes for gradual deployment
- Failure Reporting: Includes TLS-RPT integration for monitoring security violations
Exploring DANE: DNS-Powered Certificate Authentication
DANE takes a fundamentally different approach by leveraging DNS Security Extensions (DNSSEC) to publish certificate information directly in DNS records. Standardized in RFC 6698, DANE creates a direct trust relationship between domain names and their associated certificates.
DANE Implementation Architecture
TLSA Records: DANE uses TLSA (Transport Layer Security Authentication) records in DNS to specify which certificates or certificate authorities are authorized for a service.
DNSSEC Dependency: DANE requires a fully functional DNSSEC implementation to ensure the authenticity and integrity of certificate information published in DNS.
Certificate Matching: DANE supports multiple certificate matching methods, including exact certificate matches, public key matches, and certificate authority validation.
DANE Security Mechanisms
- Certificate Pinning: Binds specific certificates to domain names through DNS
- CA Independence: Reduces reliance on traditional certificate authority infrastructure
- Cryptographic Validation: Uses DNSSEC signatures to verify certificate authenticity
- Multiple Validation Options: Supports various certificate validation methods
- Protocol Integration: Works with multiple protocols beyond SMTP, including HTTPS and other TLS-enabled services
Technical Implementation Comparison
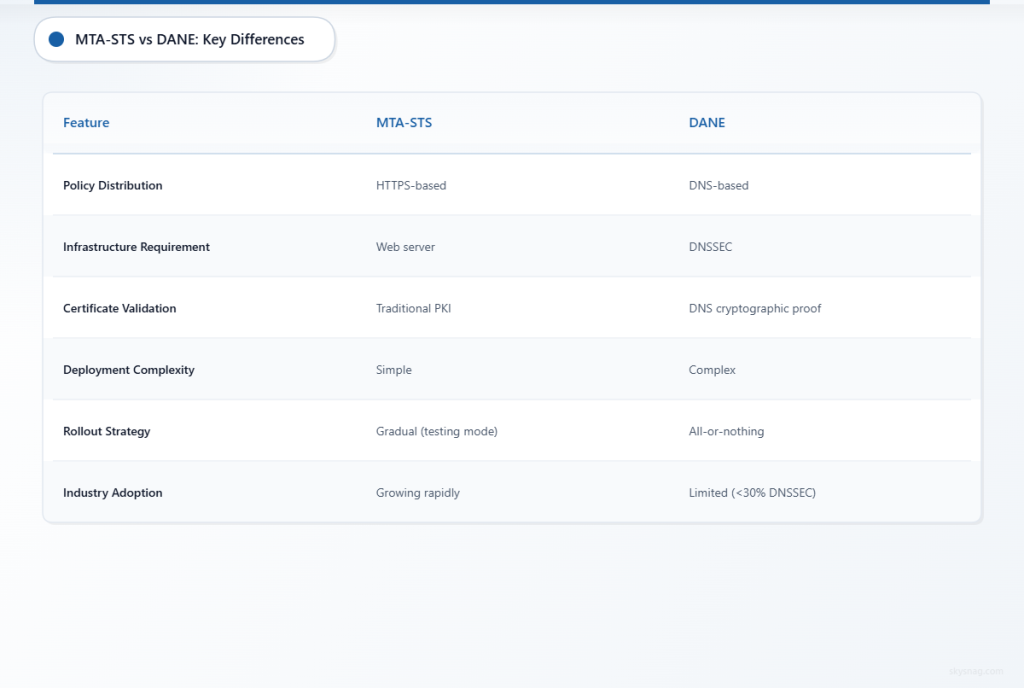
Deployment Complexity
MTA-STS Implementation:
- Requires web server configuration for policy hosting
- Simple DNS TXT record creation
- Straightforward policy file management
- Compatible with existing PKI infrastructure
- Gradual rollout through testing mode
DANE Implementation:
- Demands full DNSSEC deployment
- Complex TLSA record configuration
- Requires certificate lifecycle management in DNS
- May need specialized DNS hosting
- All-or-nothing deployment approach
Infrastructure Requirements
Organizations considering MTA-STS vs DANE face different infrastructure demands. MTA-STS requires minimal additional infrastructure beyond a web server capable of serving policy files over HTTPS. Most organizations already possess this capability through their existing web presence.
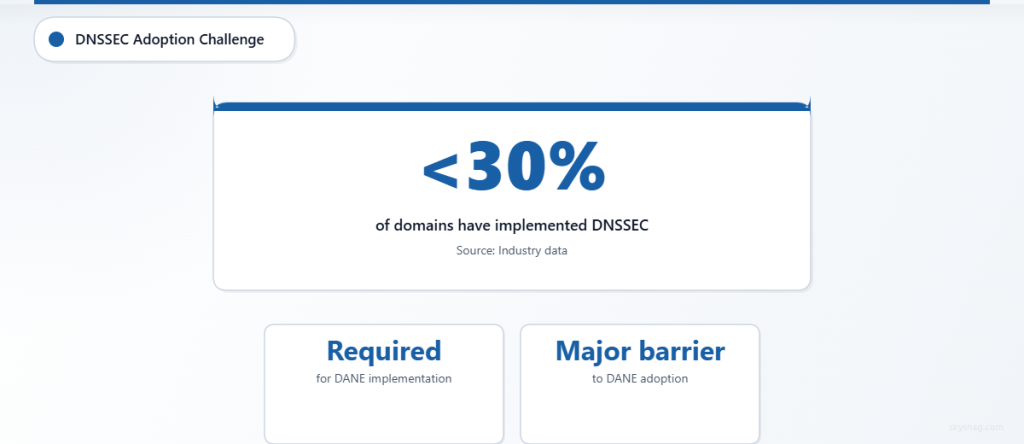
DANE implementation presents more significant infrastructure challenges. DNSSEC deployment requires specialized DNS hosting or significant internal DNS infrastructure upgrades. According to recent industry data, less than 30% of domains have implemented DNSSEC, creating a substantial barrier to DANE adoption.
Maintenance and Operations
MTA-STS Maintenance:
- Policy updates via simple file modifications
- Standard web server monitoring
- Certificate management through existing PKI processes
- Clear error reporting through TLS-RPT
DANE Maintenance:
- DNS record updates for certificate changes
- DNSSEC key management and rotation
- Complex troubleshooting for DNSSEC-related issues
- Limited visibility into validation failures
Security Analysis and Effectiveness
Attack Surface Mitigation
Both protocols address different attack vectors in email security. MTA-STS primarily protects against man-in-the-middle attacks during SMTP transmission by enforcing encryption and certificate validation. This approach effectively prevents attackers from intercepting or modifying email communications through connection downgrade attacks.
DANE provides more comprehensive certificate validation by establishing cryptographic proof of certificate authenticity through DNSSEC. This mechanism protects against rogue certificate attacks and reduces dependency on potentially compromised certificate authorities.
Trust Model Differences
The trust models underlying MTA-STS and DANE represent fundamentally different approaches to certificate validation:
MTA-STS Trust Model: Relies on traditional PKI infrastructure and certificate authorities, enhanced with policy-based enforcement. This approach maintains compatibility with existing certificate management practices while adding security layers.
DANE Trust Model: Creates a direct cryptographic trust relationship between domain owners and their certificates through DNSSEC. This model reduces reliance on certificate authorities but requires robust DNSSEC infrastructure.
Adoption Rates and Industry Support
Current Market Penetration
MTA-STS has achieved broader adoption across major email providers and enterprises due to its simpler implementation requirements. Major providers including Gmail, Yahoo, and Microsoft have implemented MTA-STS support, creating a network effect that encourages further adoption.
DANE adoption remains limited primarily due to DNSSEC implementation challenges. While technically superior in some aspects, the practical barriers to DANE deployment have restricted its widespread adoption.
Vendor Support
Email security vendors have generally provided stronger support for MTA-STS implementation due to customer demand and simpler integration requirements. Skysnag Protect includes comprehensive MTA-STS monitoring and policy management capabilities, helping organizations implement and maintain effective transport security policies.
DANE support varies significantly among vendors, with many focusing on niche use cases or specialized security requirements rather than broad enterprise deployment.
Implementation Decision Framework
When to Choose MTA-STS
Organizations should prioritize MTA-STS implementation when:
- Seeking rapid transport security deployment
- Working within existing PKI infrastructure constraints
- Requiring broad compatibility with email partners
- Needing clear policy reporting and monitoring
- Operating without comprehensive DNSSEC infrastructure
When to Consider DANE
DANE implementation makes sense for organizations that:
- Have robust DNSSEC infrastructure already deployed
- Require maximum certificate validation security
- Need to reduce certificate authority dependencies
- Operate in high-security environments
- Can manage complex DNS-based certificate lifecycle processes
Hybrid Approach Considerations
Some organizations implement both MTA-STS and DANE to maximize security coverage. This approach provides redundant protection mechanisms but requires careful coordination to prevent policy conflicts and operational complexity.
Practical Deployment Strategies
Phased Implementation Approach
Phase 1: Assessment
- Evaluate current email infrastructure and security requirements
- Assess DNSSEC readiness for DANE consideration
- Identify key email partners and their security capabilities
Phase 2: Testing
- Deploy MTA-STS in testing mode for gradual validation
- Monitor TLS-RPT reports for implementation issues
- Validate certificate management processes
Phase 3: Enforcement
- Enable enforcement mode after successful testing period
- Monitor ongoing compliance and security metrics
- Expand implementation across all mail-enabled domains
Common Implementation Pitfalls
Organizations frequently encounter challenges during transport security deployment:
Certificate Management Issues: Failure to coordinate transport security policies with certificate renewal processes can create delivery failures.
Policy Synchronization: Misaligned policies between different security mechanisms can cause confusion and operational issues.
Monitoring Gaps: Inadequate monitoring of transport security effectiveness limits the ability to detect and respond to security issues.
Performance and Operational Impact
Latency Considerations
MTA-STS introduces minimal latency overhead through HTTPS policy retrieval and caching. The impact on email delivery performance is negligible for most organizations, as policies are cached for extended periods.
DANE can introduce additional DNS lookup latency, particularly in environments with complex DNSSEC validation chains. However, proper DNS caching and optimization can minimize performance impact.
Monitoring and Troubleshooting
Effective monitoring capabilities differ significantly between the two approaches:
MTA-STS Monitoring: TLS-RPT provides detailed reporting on transport security violations, certificate validation failures, and policy enforcement issues. This standardized reporting enables proactive security monitoring and rapid issue resolution.
DANE Monitoring: DANE troubleshooting relies heavily on DNS analysis tools and DNSSEC validation monitoring. The complexity of DNSSEC debugging can make issue resolution more challenging for many IT teams.
Future Considerations and Evolution
Protocol Development Trends
Both MTA-STS and DANE continue evolving to address emerging security challenges and improve deployment simplicity. Recent developments include enhanced policy flexibility for MTA-STS and simplified DANE deployment tools.
The email security landscape increasingly favors solutions that balance security effectiveness with practical deployment requirements, suggesting continued strong growth for MTA-STS adoption.
Integration with Broader Security Frameworks
Transport security protocols are increasingly integrated with comprehensive email security platforms that provide unified policy management and monitoring across multiple security standards including DMARC, SPF, and DKIM.
Key Takeaways
MTA-STS emerges as the clear winner for most organizations seeking to implement email transport security. Its simpler deployment requirements, broad vendor support, and effective security protections make it the practical choice for enterprise email security strategies. The protocol’s integration with existing PKI infrastructure and comprehensive reporting capabilities through TLS-RPT provide operational advantages that facilitate long-term maintenance and security monitoring.
DANE offers superior theoretical security through its cryptographic certificate validation approach, but implementation complexity and DNSSEC dependencies limit its practical applicability for most organizations. DANE remains valuable for high-security environments with existing DNSSEC infrastructure and specialized security requirements.
Organizations should prioritize MTA-STS implementation as their primary email transport security strategy while considering DANE for specific use cases that justify its additional complexity. The combination of MTA-STS with comprehensive email authentication protocols provides robust protection against modern email-based threats while maintaining operational simplicity and broad compatibility.
For organizations ready to implement effective email transport security, Skysnag Protect offers comprehensive MTA-STS policy management and monitoring capabilities that simplify deployment and ensure ongoing security effectiveness across your entire email infrastructure.
Ready to secure your sending identity and protect your domain reputation? Sign up today.
Get started


