How MTA-STS Prevents Email Downgrade Attacks: Technical Defense Mechanisms
Email downgrade attacks represent one of the most sophisticated threats to modern email infrastructure, exploiting the opportunistic nature of SMTP to force communications into vulnerable, unencrypted channels. MTA-STS (Mail Transfer Agent Strict Transport Security) serves as a critical defense mechanism against these attacks, providing mandatory encryption policies that prevent malicious actors from intercepting and manipulating email traffic.
Understanding Email Downgrade Attack Vectors
The SMTP Opportunistic Encryption Vulnerability
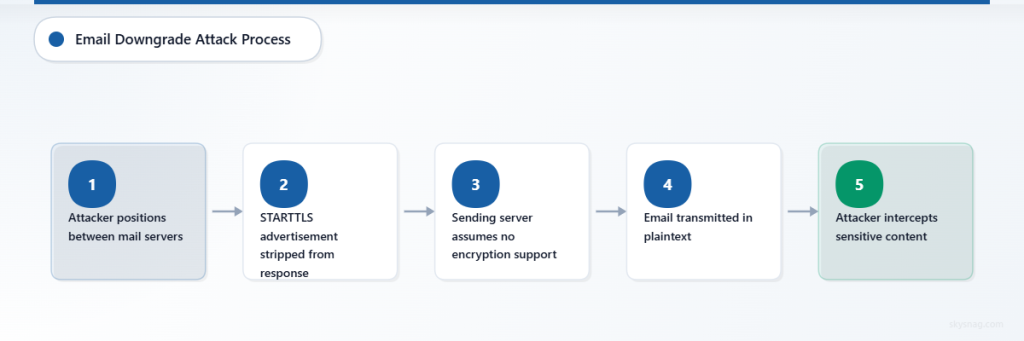
SMTP’s inherent design allows for opportunistic encryption through STARTTLS, where sending mail servers attempt to establish encrypted connections but fall back to plaintext transmission if encryption fails. This flexibility creates an attack surface that threat actors exploit through several sophisticated methods:
Active Man-in-the-Middle Manipulation: Attackers position themselves between communicating mail servers and actively strip STARTTLS advertisements from SMTP responses. When the sending server receives a response without STARTTLS capability, it assumes the receiving server doesn’t support encryption and transmits emails in plaintext.
DNS Poisoning for Mail Routing: Malicious actors compromise DNS responses for MX record lookups, redirecting email traffic to attacker-controlled servers that don’t advertise encryption capabilities. The legitimate sending server, following standard SMTP behavior, delivers emails without encryption to the malicious endpoint.
BGP Hijacking for Mail Interception: Advanced attackers leverage Border Gateway Protocol vulnerabilities to reroute email traffic through their infrastructure, where they can manipulate SMTP negotiations and force plaintext transmission while maintaining the appearance of successful delivery.
Real-World Attack Scenarios
Nation-state actors have demonstrated particular sophistication in deploying these techniques. In documented cases, attackers have established infrastructure that mirrors legitimate mail servers but systematically strips encryption capabilities. Corporate communications, government correspondence, and financial transactions become vulnerable to interception and content analysis.
The attack timeline typically follows this pattern: reconnaissance identifies high-value email communications, network positioning establishes the man-in-the-middle capability, active downgrade forces plaintext transmission, and data exfiltration occurs without detection by either sender or recipient.
MTA-STS Technical Architecture and Implementation
Policy Framework and Enforcement Mechanisms
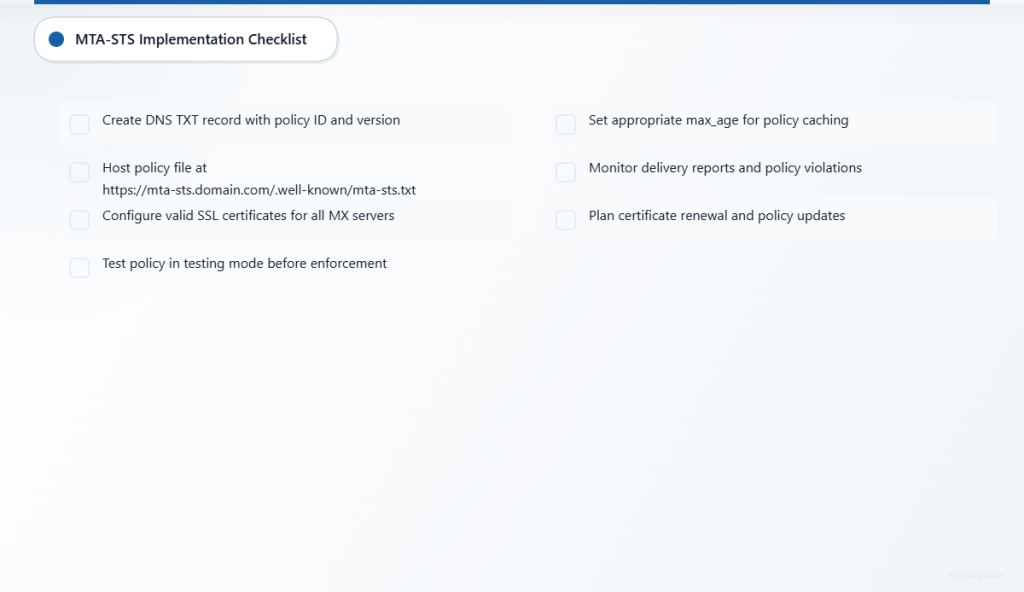
MTA-STS operates through a dual-component system that establishes and enforces strict encryption policies. The DNS TXT record serves as the discovery mechanism, advertising policy availability and version information. This record follows the format v=STSv1; id=policy_identifier; and enables sending servers to locate the full policy specification.
The policy file, hosted at https://mta-sts.domain.com/.well-known/mta-sts.txt, contains comprehensive security requirements:
version: STSv1
mode: enforce
mx: mail.example.com
mx: backup-mail.example.com
max_age: 604800The mode parameter defines enforcement behavior with three distinct options. Testing mode enables policy monitoring without blocking email delivery, allowing administrators to identify potential compatibility issues. Enforce mode strictly requires encrypted connections and rejects emails that cannot establish secure transport. None mode effectively disables MTA-STS protection while maintaining policy infrastructure.
Certificate Validation and Trust Establishment
MTA-STS extends beyond basic encryption requirements by mandating proper certificate validation. The protocol requires that receiving mail servers present valid SSL/TLS certificates that match their hostname and chain to trusted certificate authorities. This prevents attackers from using self-signed or fraudulent certificates to establish seemingly encrypted but actually compromised connections.
The certificate validation process includes multiple verification steps: hostname matching against the MX record, certificate chain validation to trusted root authorities, certificate expiration verification, and revocation status checking through CRL or OCSP mechanisms.
Attack Prevention Through Policy Enforcement
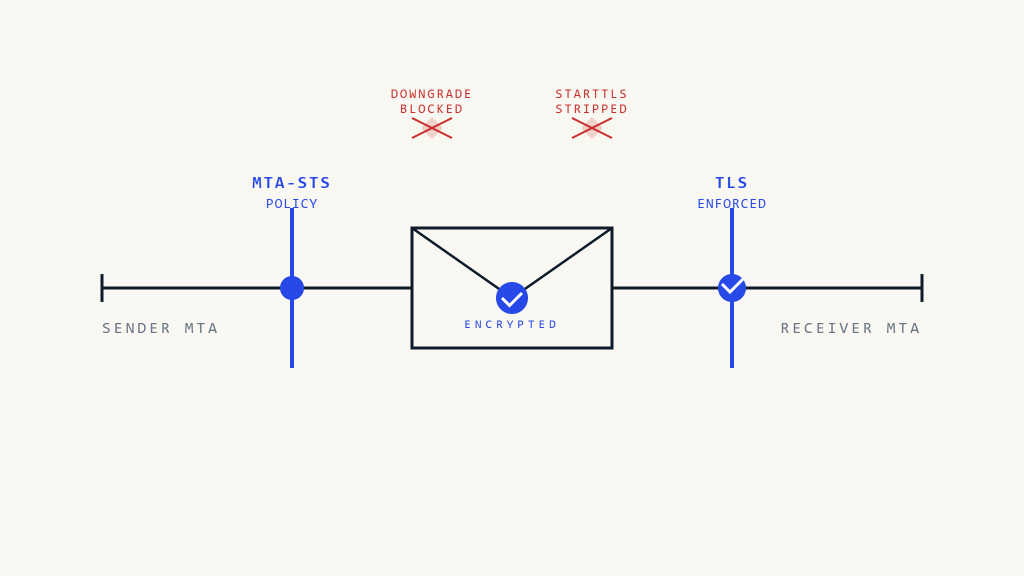
STARTTLS Stripping Protection
When MTA-STS policies are active, sending mail servers can no longer fall back to plaintext transmission even if STARTTLS negotiation fails. The policy explicitly requires encryption, forcing the sending server to either establish a secure connection or defer delivery. This eliminates the primary attack vector for downgrade attacks.
Consider this technical scenario: an attacker intercepts SMTP traffic and removes STARTTLS advertisements from server responses. Without MTA-STS, the sending server would proceed with plaintext transmission. With MTA-STS enforcement, the sending server recognizes the policy requirement for encryption and either retries the connection or queues the message for later delivery, preventing the downgrade attack.
DNS Manipulation Resistance
MTA-STS policies include specific MX server declarations that limit which mail servers can receive email for a domain. Even if attackers successfully manipulate DNS MX records to redirect traffic, the MTA-STS policy restricts acceptance to explicitly authorized servers. This creates a secondary validation layer that prevents successful DNS-based redirection attacks.
The policy validation process requires that receiving servers not only support encryption but also appear in the authorized MX list within the MTA-STS policy. Attackers cannot simply establish encrypted endpoints; they must compromise the policy infrastructure itself, significantly increasing attack complexity.
Connection Security Validation
MTA-STS enforcement includes comprehensive connection security validation that extends beyond basic encryption. The protocol verifies cipher suite strength, protocol version requirements, and certificate chain integrity. This multi-layered validation prevents attacks that attempt to establish encrypted but cryptographically weak connections.
Modern implementations reject connections using deprecated cipher suites, weak key exchanges, or outdated TLS versions. This ensures that even if attackers establish encrypted connections, the cryptographic strength meets current security standards and resists known attack methods.
Integration with Email Security Infrastructure
Skysnag Protect Implementation
Skysnag Protect provides comprehensive MTA-STS implementation that simplifies policy deployment and management across complex email infrastructures. The platform automates policy generation, handles certificate validation requirements, and provides detailed monitoring of encryption enforcement across all email communications.
The service includes advanced threat detection capabilities that identify attempted downgrade attacks and provide detailed forensic information about attack patterns. This enables security teams to understand threat actor methodologies and implement additional defensive measures where necessary.
TLSRPT Integration for Attack Visibility
MTA-STS operates in conjunction with TLSRPT (TLS Reporting) to provide comprehensive visibility into encryption enforcement and attack attempts. TLSRPT generates detailed reports about connection failures, policy violations, and encryption negotiation patterns that enable security teams to identify systematic attack campaigns.
The reporting framework captures attempted downgrade attacks, certificate validation failures, and connection pattern anomalies. This data provides crucial intelligence about threat actor capabilities and helps organizations adjust security policies based on observed attack methods.
Deployment Considerations and Edge Cases
MTA-STS implementation requires careful consideration of legitimate email infrastructure patterns. Organizations with complex mail routing, third-party email services, and backup mail servers must ensure that policies accommodate all legitimate communication paths while maintaining security enforcement.
Gradual Deployment Strategy: Organizations should implement MTA-STS using testing mode initially to identify potential compatibility issues with legitimate mail servers. The testing period allows for policy refinement and ensures that security enforcement doesn’t inadvertently block legitimate communications.
Third-Party Service Integration: Modern email infrastructures often include cloud-based security services, spam filtering systems, and backup mail providers. MTA-STS policies must explicitly include these services in authorized MX lists while ensuring they meet encryption and certificate requirements.
Emergency Communication Procedures: Critical communications systems require backup procedures for scenarios where MTA-STS enforcement prevents email delivery due to infrastructure issues. Organizations should establish alternative communication channels and policy override procedures for emergency situations.
Monitoring and Threat Intelligence
Attack Pattern Recognition
Effective MTA-STS deployment includes comprehensive monitoring systems that identify attack patterns and provide actionable threat intelligence. Modern attacks often involve systematic probing of multiple domains to identify vulnerabilities and policy gaps.
Monitoring systems should track connection failure patterns, certificate validation anomalies, and geographic distributions of connection attempts. These patterns help identify coordinated attack campaigns and enable proactive defense adjustments.
Performance Impact Assessment
MTA-STS enforcement includes additional validation steps that can impact email delivery performance. Organizations must balance security requirements with operational efficiency, particularly for high-volume email systems.
Connection caching, policy validation optimization, and certificate chain caching can significantly reduce performance impacts while maintaining security effectiveness. Regular performance monitoring ensures that security enforcement doesn’t create unacceptable delivery delays.
Future Attack Evolution and Defense Adaptation
Emerging Threat Vectors
As MTA-STS adoption increases, threat actors are developing more sophisticated attack methods that attempt to circumvent policy enforcement. These include policy infrastructure attacks, certificate authority compromise attempts, and advanced persistent threat campaigns that target policy management systems.
Organizations must maintain updated threat intelligence and adapt MTA-STS implementations to address emerging attack methods. This includes regular policy reviews, certificate authority monitoring, and infrastructure security assessments.
Standards Evolution and Compatibility
Email security standards continue evolving to address new threat vectors and improve interoperability. MTA-STS implementations must remain compatible with emerging standards while maintaining backward compatibility with existing infrastructure.
The ongoing development of email security protocols includes enhanced certificate validation methods, improved policy distribution mechanisms, and integration with emerging authentication standards. Organizations should plan for standards evolution in their long-term security strategies.
Key Takeaways
MTA-STS provides robust protection against email downgrade attacks through mandatory encryption policies and comprehensive certificate validation. The protocol prevents STARTTLS stripping attacks, resists DNS manipulation, and ensures cryptographically strong connections for all email communications.
Successful implementation requires careful planning, gradual deployment, and comprehensive monitoring systems. Organizations must balance security enforcement with operational requirements while maintaining compatibility with legitimate email infrastructure.
The integration of MTA-STS with broader email security frameworks creates layered defense systems that significantly increase the cost and complexity of successful attacks. Regular monitoring, policy maintenance, and threat intelligence integration ensure continued effectiveness against evolving attack methods.
Ready to implement comprehensive email security protection? Skysnag Protect provides enterprise-grade MTA-STS deployment and management with advanced threat detection capabilities.
Ready to secure your sending identity and protect your domain reputation? Sign up today.
Get started


