DMARC forensic reports and aggregate reports serve distinct purposes in email security monitoring, yet many organizations struggle to understand when and how to use each type effectively. While aggregate reports provide high-level authentication statistics, forensic reports deliver granular details about individual message failures that can be crucial for threat detection and compliance.
The choice between implementing RUA (Report URI for Aggregate) or RUF (Report URI for Forensic) tags in your DMARC policy significantly impacts your security visibility and privacy posture. Understanding these differences is essential for building an effective email authentication strategy.
I. What Are DMARC Aggregate Reports?
DMARC aggregate reports (RUA) provide statistical summaries of email authentication results over a 24-hour period. These reports contain aggregated data about messages that claim to be from your domain, including authentication pass/fail rates and source information.
Key Components of Aggregate Reports
- Authentication results: SPF, DKIM, and DMARC alignment status
- Message volume statistics: Total emails processed and their disposition
- Source identification: IP addresses and sending infrastructure details
- Policy evaluation: How your DMARC policy was applied to message flows
Aggregate reports typically arrive daily from receiving mail servers and contain data formatted in XML. They help organizations understand their email ecosystem’s overall health without revealing sensitive message content.
Privacy and Security Benefits
Aggregate reports maintain sender privacy by providing statistical data rather than actual message content. This approach allows organizations to monitor authentication performance while minimizing exposure of confidential information to third-party recipients.
II. Understanding DMARC Forensic Reports
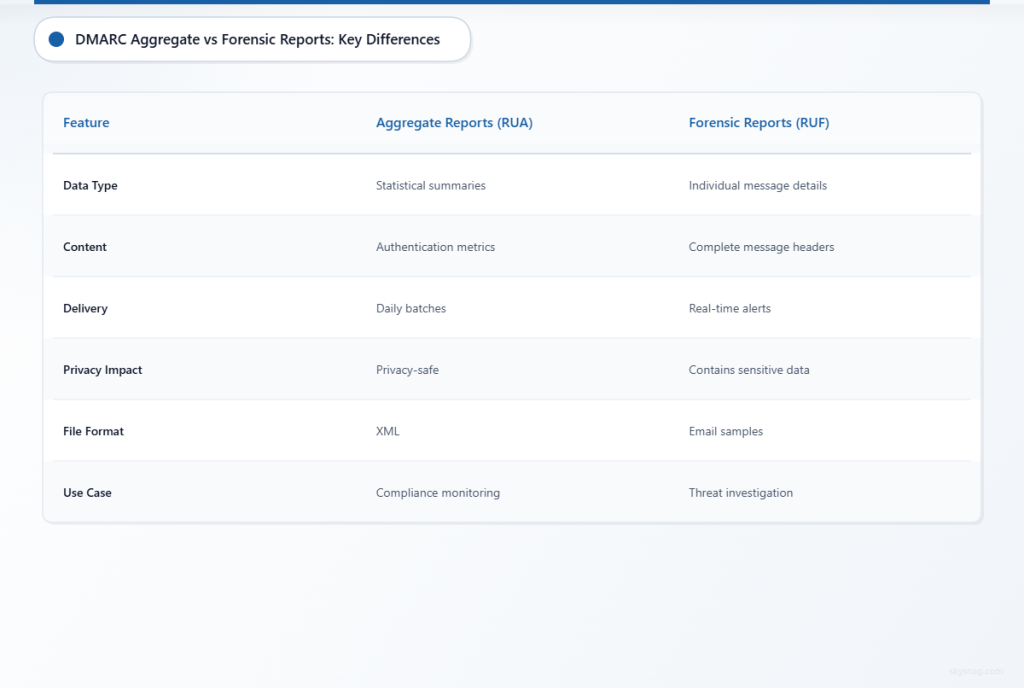
DMARC forensic reports (RUF) deliver detailed information about individual messages that fail DMARC authentication. Unlike aggregate reports, forensic reports contain copies or samples of actual failed messages, providing deep visibility into authentication failures.
Detailed Forensic Report Contents
- Complete message headers: Full header information for failed messages
- Authentication failure reasons: Specific SPF, DKIM, or alignment issues
- Message samples: Partial or complete copies of failed emails
- Real-time delivery: Reports sent immediately when failures occur
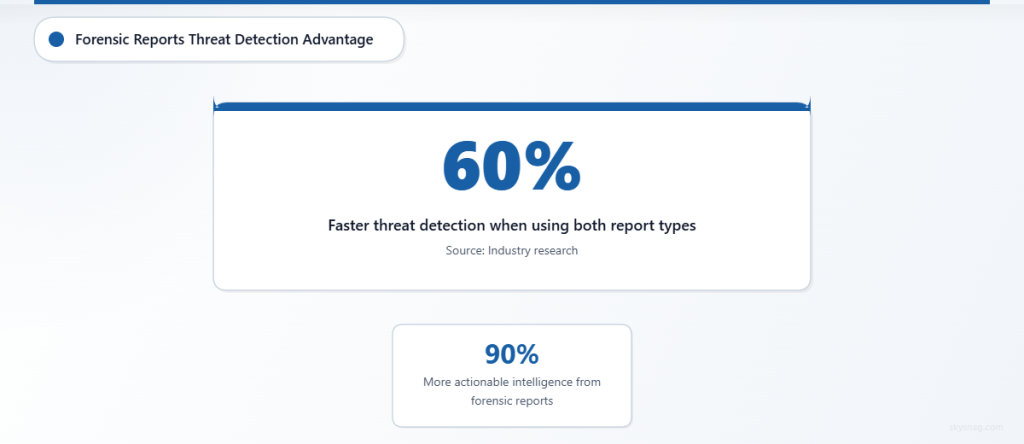
According to recent industry analysis, forensic reports can provide up to 90% more actionable intelligence for threat hunting compared to aggregate reports alone. However, this granular visibility comes with significant privacy considerations.
Privacy and Compliance Implications
Forensic reports pose substantial privacy risks because they contain actual message content, including potentially sensitive business communications. Many receiving mail servers have stopped generating forensic reports due to privacy regulations like GDPR and data protection concerns.
III. RUA vs RUF: Technical Implementation Differences
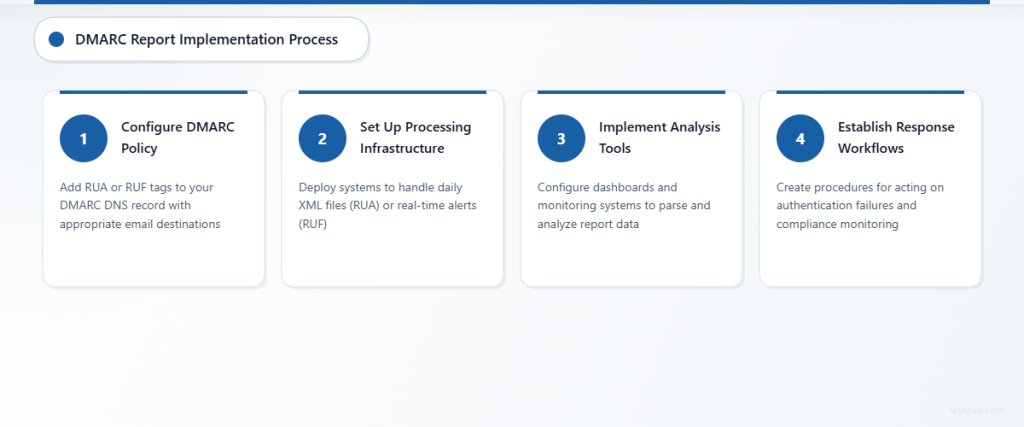
The implementation approach for aggregate versus forensic reporting differs significantly in both DMARC policy configuration and processing requirements.
Aggregate Report Configuration (RUA)
v=DMARC1; p=quarantine; rua=mailto:[email protected]; fo=1RUA implementation requires:
- Daily processing capability: Handle large XML files containing thousands of records
- Data aggregation tools: Parse and analyze statistical information
- Trend analysis systems: Monitor authentication performance over time
- Storage infrastructure: Maintain historical data for compliance requirements
Forensic Report Configuration (RUF)
v=DMARC1; p=quarantine; ruf=mailto:[email protected]; fo=1RUF implementation demands:
- Real-time processing: Handle immediate alert notifications
- Content security measures: Protect sensitive message data
- Incident response workflows: Act on individual authentication failures
- Privacy compliance controls: Ensure proper handling of message content
IV. Use Cases and Strategic Applications
Different organizational needs call for different DMARC reporting strategies, with some requiring both report types for comprehensive coverage.
When to Prioritize Aggregate Reports
Organizations should focus on aggregate reporting for:
- Compliance monitoring: Meeting regulatory requirements with privacy-safe data
- Infrastructure optimization: Understanding legitimate email flow patterns
- Gradual policy enforcement: Moving from p=none to p=quarantine safely
- Vendor management: Monitoring third-party sender performance
Skysnag Comply provides automated aggregate report processing that transforms complex XML data into actionable compliance dashboards, helping organizations maintain continuous DMARC monitoring without manual intervention.
When Forensic Reports Add Value
Forensic reporting becomes critical for:
- Active threat hunting: Investigating sophisticated phishing campaigns
- Incident response: Understanding specific attack vectors and techniques
- Authentication troubleshooting: Diagnosing complex SPF or DKIM configuration issues
- Advanced threat detection: Identifying patterns in authentication bypass attempts
Research indicates that organizations using both report types detect email-based threats 60% faster than those relying solely on aggregate data.
V. Privacy Considerations and Best Practices
The privacy implications of DMARC reporting vary dramatically between aggregate and forensic approaches, requiring careful consideration of regulatory requirements and organizational policies.
Aggregate Report Privacy Protection
Aggregate reports inherently protect privacy by:
- Data anonymization: Statistical summaries without message content
- Source aggregation: IP addresses grouped rather than individually tracked
- Time-based batching: Data collected over 24-hour periods rather than real-time
- Standards compliance: Built-in privacy protections in DMARC specification
Forensic Report Privacy Risks
Organizations implementing forensic reporting must address:
- Message content exposure: Full or partial email content shared with external parties
- Regulatory compliance: GDPR, CCPA, and industry-specific privacy requirements
- Data retention policies: Secure storage and deletion of sensitive forensic data
- Third-party sharing: Controlling how forensic data is processed by report recipients
Implementation Recommendations
Based on current privacy landscape and threat environment, organizations should:
- Start with aggregate reporting: Establish baseline monitoring with privacy-safe data
- Implement selective forensic reporting: Use RUF only for critical domains or specific threat scenarios
- Review receiving server capabilities: Verify that target servers actually generate forensic reports
- Establish data handling procedures: Create policies for processing and storing forensic information
VI. Performance and Operational Impact
The operational requirements for processing aggregate versus forensic reports differ significantly in terms of volume, timing, and resource requirements.
Aggregate Report Processing
Aggregate reports typically generate:
- Predictable volume: Daily reports with consistent timing
- Batch processing opportunities: Efficient handling of large datasets
- Historical trending capability: Long-term analysis and pattern recognition
- Automated processing potential: Machine-readable XML format enables automation
Forensic Report Challenges
Forensic reporting creates operational challenges including:
- Unpredictable volume: Real-time generation based on failure rates
- Immediate response requirements: Time-sensitive threat intelligence
- Manual analysis needs: Complex message content requiring human interpretation
- Storage and retention complexity: Sensitive data management requirements
Organizations should consider that forensic reports may generate 10-50x more individual messages than aggregate reports, depending on authentication failure rates and email volume.
VII. Making the Right Choice for Your Organization
The decision between aggregate and forensic reporting should align with organizational security maturity, privacy requirements, and operational capabilities.
Assessment Framework
Evaluate your reporting needs based on:
Security Requirements
- Current threat landscape exposure
- Incident response maturity level
- Compliance and regulatory obligations
- Integration with existing security tools
Operational Capacity
- Available security analyst resources
- Automated processing capabilities
- Data storage and retention infrastructure
- Privacy and legal compliance frameworks
Risk Tolerance
- Acceptable levels of email-based threats
- Privacy exposure comfort levels
- Regulatory penalty considerations
- Business continuity requirements
Most organizations benefit from starting with comprehensive aggregate reporting through solutions like Skysnag Comply, which provides automated DMARC monitoring with built-in privacy protection and compliance reporting capabilities.
VIII. Key Takeaways
DMARC aggregate and forensic reports serve complementary but distinct purposes in email security monitoring. Aggregate reports provide privacy-safe statistical insights essential for compliance and infrastructure optimization, while forensic reports deliver granular threat intelligence at the cost of privacy exposure and operational complexity.
Organizations should prioritize aggregate reporting for foundational DMARC monitoring, implementing forensic reporting only when specific threat hunting or troubleshooting requirements justify the additional privacy and operational overhead. The choice between RUA and RUF configurations should align with organizational security maturity, privacy requirements, and available operational resources.
Modern DMARC compliance platforms like Skysnag Comply can automate much of the aggregate report processing complexity while maintaining the privacy and security benefits that make aggregate reporting the preferred choice for most organizations.