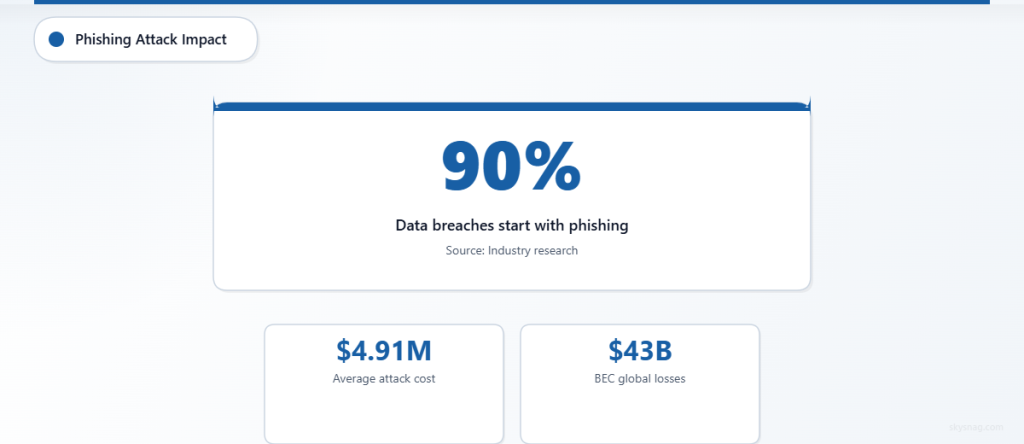
Phishing attacks remain the most common cybersecurity threat facing organizations, with over 90% of successful data breaches starting with a phishing email. Despite increased awareness, these attacks continue to evolve, becoming more sophisticated and harder to detect. The financial impact is staggering, with the average cost of a phishing attack reaching $4.91 million per incident according to IBM’s latest security report.
The challenge isn’t just the frequency of these attacks, but their increasing sophistication. Modern phishing campaigns use advanced social engineering techniques, spoofed domains that closely mimic legitimate brands, and AI-generated content that passes casual inspection. This reality demands a comprehensive approach to phishing attack prevention that goes beyond basic user training.
I. Understanding the Modern Phishing Landscape
Before diving into prevention strategies, it’s crucial to understand what you’re defending against. Today’s phishing attacks fall into several categories, each requiring different defensive measures.
Spear Phishing targets specific individuals within organizations, often using publicly available information to create highly personalized messages. These attacks typically research their targets through social media and company websites, crafting messages that appear to come from trusted colleagues or business partners.
Business Email Compromise (BEC) attacks focus on financial fraud, often targeting finance teams and executives. These sophisticated schemes can result in wire transfer fraud, with the FBI reporting over $43 billion in global losses from BEC attacks over the past decade.
Brand Impersonation attacks use familiar company logos and formatting to trick recipients into believing emails come from trusted sources. Microsoft, Amazon, and banking institutions remain the most commonly impersonated brands in these campaigns.
The evolution of these threats means traditional email filtering alone is insufficient. Modern phishing attack prevention requires layered security controls that address both technical vulnerabilities and human factors.
II. Step 1: Implement DMARC Email Authentication
Domain-based Message Authentication, Reporting, and Conformance (DMARC) serves as your first line of defense against email spoofing and phishing attacks. This email authentication protocol works alongside SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail) to verify sender legitimacy.
DMARC prevents attackers from using your domain to send fraudulent emails, protecting both your organization and your customers from brand impersonation attacks. When properly configured, DMARC can block up to 99% of email spoofing attempts targeting your domain.
Implementation Steps:
- Publish SPF records for all domains and subdomains
- Configure DKIM signing for outbound email
- Start with DMARC policy set to “none” for monitoring
- Gradually move to “quarantine” then “reject” policies
- Monitor DMARC reports to identify legitimate sending sources
Skysnag Protect automates this entire process, providing real-time monitoring and simplified DMARC implementation that doesn’t require deep technical expertise. The platform handles the complexity of gradual policy enforcement while ensuring legitimate email delivery remains unaffected.
III. Step 2: Deploy Advanced Email Security Filtering
While DMARC handles domain spoofing, comprehensive email security requires additional filtering layers to catch sophisticated phishing attempts that may come from legitimate but compromised domains.
Modern email security solutions use machine learning algorithms to analyze email content, sender behavior, and contextual factors. These systems can identify subtle indicators of phishing attempts, including unusual sending patterns, suspicious URLs, and social engineering language patterns.
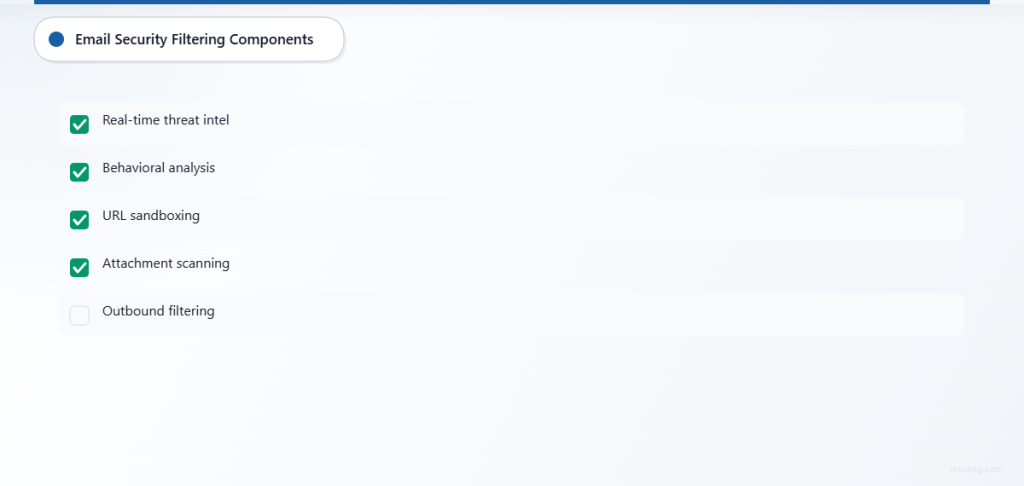
Key Filtering Components:
- Real-time threat intelligence feeds
- Behavioral analysis of sender patterns
- URL sandboxing and reputation checking
- Attachment analysis and safe document viewing
- Integration with threat intelligence platforms
Look for solutions that provide both inbound and outbound email filtering. Outbound filtering helps detect compromised accounts within your organization before they can be used to attack external targets or damage your sender reputation.
IV. Step 3: Establish Email Security Policies and Procedures
Technical controls are only effective when supported by clear policies and procedures. Your email security policy should define acceptable use, outline response procedures for suspected phishing attacks, and establish clear escalation paths for security incidents.
Essential Policy Elements:
- Guidelines for identifying suspicious emails
- Procedures for reporting potential phishing attempts
- Incident response workflows for confirmed attacks
- Regular review and update schedules
- Integration with broader cybersecurity policies
Train your IT team on proper incident response procedures, including email header analysis, threat hunting techniques, and coordination with security vendors. Establish clear communication channels between IT security teams and end users to encourage prompt reporting of suspicious emails.
Document your phishing response procedures and test them regularly through tabletop exercises. These simulations help identify gaps in your processes and ensure team members understand their roles during an actual incident.
V. Step 4: Conduct Comprehensive Security Awareness Training
Human factors remain the weakest link in email security, making comprehensive training programs essential for effective phishing attack prevention. However, traditional awareness training often falls short because it focuses on generic threats rather than the specific phishing techniques targeting your industry and organization.
Effective security awareness training goes beyond annual presentations to create ongoing education programs that adapt to emerging threats. The most successful programs use real-world examples and interactive scenarios that help employees develop intuitive threat recognition skills.
Training Program Components:
- Monthly phishing simulation campaigns
- Industry-specific threat awareness sessions
- Hands-on exercises with actual phishing examples
- Regular updates on emerging attack techniques
- Recognition programs for employees who report threats
Personalize training content based on job roles and departments. Finance teams need specific training on BEC attacks and wire transfer fraud, while HR departments should focus on social engineering attempts that exploit employee information.
Track training effectiveness through metrics beyond simple completion rates. Monitor click rates on simulated phishing emails, time to report suspicious messages, and improvements in threat recognition accuracy over time.
VI. Step 5: Implement Multi-Factor Authentication (MFA)
Multi-factor authentication serves as a critical safety net when phishing attacks successfully harvest user credentials. Even if an employee falls victim to a credential harvesting attack, MFA can prevent unauthorized access to your systems and data.
Modern phishing attacks specifically target MFA bypass techniques, including SIM swapping, social engineering against help desk staff, and MFA fatigue attacks. Your MFA implementation must account for these evolving threats.
MFA Best Practices:
- Use authenticator apps instead of SMS when possible
- Implement risk-based authentication for unusual access patterns
- Require MFA for all administrative and privileged accounts
- Provide clear user guidance on MFA best practices
- Monitor for MFA bypass attempts and unusual authentication patterns
Consider implementing hardware security keys for high-privilege accounts and employees who are frequent targets of phishing attacks. While more expensive than software-based solutions, hardware keys provide stronger protection against advanced phishing techniques.
VII. Step 6: Deploy Email Banner and Warning Systems
Email banner systems provide real-time visual cues that help employees identify potentially suspicious messages before they take action. These warnings are particularly effective for external emails and messages that fail various authentication checks.
Effective email banners strike a balance between security awareness and user experience. Overly aggressive warning systems can lead to banner blindness, where users ignore all warnings, while insufficient warnings may not adequately alert users to genuine threats.
Banner System Features:
- Clear visual indicators for external emails
- Specific warnings for emails failing authentication
- Contextual alerts based on message content analysis
- Customizable warning levels based on risk assessment
- Integration with threat intelligence feeds
Configure banner systems to escalate warnings based on risk levels. Low-risk external emails might receive subtle banners, while messages with multiple suspicious indicators should display prominent warnings that require user acknowledgment.
VIII. Step 7: Establish Continuous Monitoring and Response Capabilities
Effective phishing attack prevention requires continuous monitoring of your email environment and rapid response to emerging threats. This includes monitoring DMARC reports, analyzing email security logs, and tracking threat indicators across your email infrastructure.
Establish baseline metrics for normal email patterns within your organization, including sending volumes, authentication success rates, and user behavior patterns. Deviations from these baselines can indicate ongoing attacks or compromised accounts.
Monitoring Components:
- Real-time DMARC report analysis
- Email security log correlation and analysis
- User behavior analytics for suspicious patterns
- Threat intelligence integration and alerting
- Automated incident response workflows
Implement automated response capabilities where possible, including automatic quarantine of suspicious emails, blocking of known malicious domains, and escalation procedures for high-risk incidents. However, maintain human oversight for complex incidents that require contextual analysis.
Consider integrating email security monitoring with your broader Security Information and Event Management (SIEM) system to correlate email threats with other security indicators across your infrastructure.
IX. Building Long-Term Phishing Resilience
Successful phishing attack prevention requires ongoing commitment and continuous improvement. Threat actors constantly evolve their techniques, and your defensive measures must adapt accordingly.
Regularly review and update your email security policies based on emerging threats and lessons learned from security incidents. Conduct annual assessments of your email security posture, including penetration testing focused on social engineering and email-based attacks.
Establish partnerships with threat intelligence providers and industry organizations to stay informed about emerging phishing techniques and campaigns targeting your industry. This intelligence helps you proactively adjust your defensive measures before new threats impact your organization.
X. Key Takeaways
Effective phishing attack prevention requires a multi-layered approach that combines technical controls, policy frameworks, and human factors. DMARC email authentication provides foundational protection against domain spoofing, while advanced email filtering catches sophisticated attacks that bypass basic authentication checks.
Comprehensive security awareness training remains critical, but it must be supported by technical controls that reduce the likelihood of successful attacks. Multi-factor authentication, email banner systems, and continuous monitoring provide additional layers of protection that help prevent successful breaches even when individual security controls are bypassed.
Success in phishing prevention comes from treating it as an ongoing process rather than a one-time implementation. Regular assessment, continuous improvement, and adaptation to emerging threats ensure your organization maintains effective protection against this persistent and evolving threat.
Ready to strengthen your organization’s email security posture? Skysnag Protect provides comprehensive DMARC implementation and monitoring capabilities that form the foundation of effective phishing attack prevention. Start building your multi-layered defense strategy today.