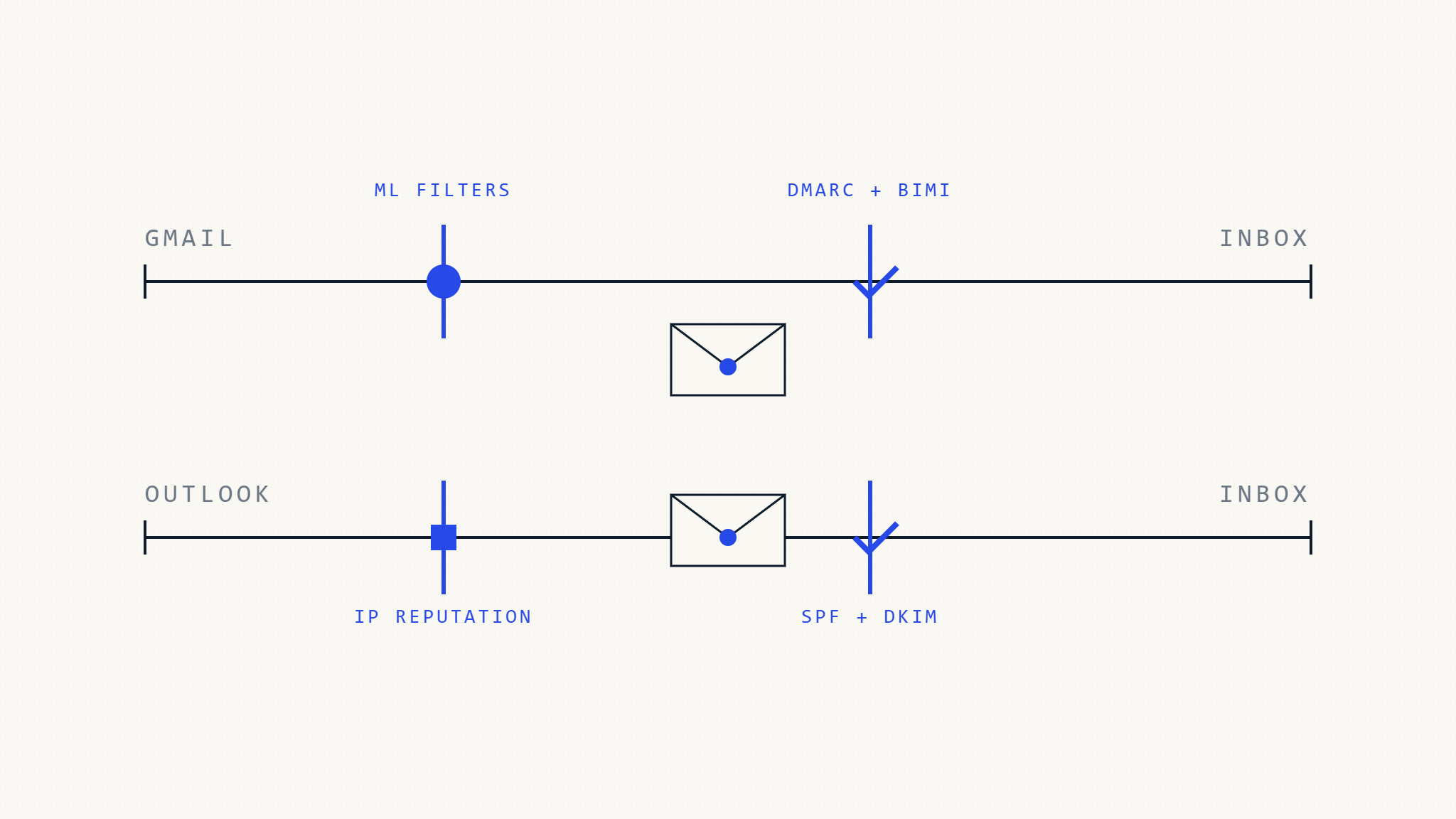
Gmail and Outlook use different filtering algorithms and authentication requirements. Learn platform-specific optimization strategies to maximize deliverability.
Filed 21 Apr 2026 · 6 min read
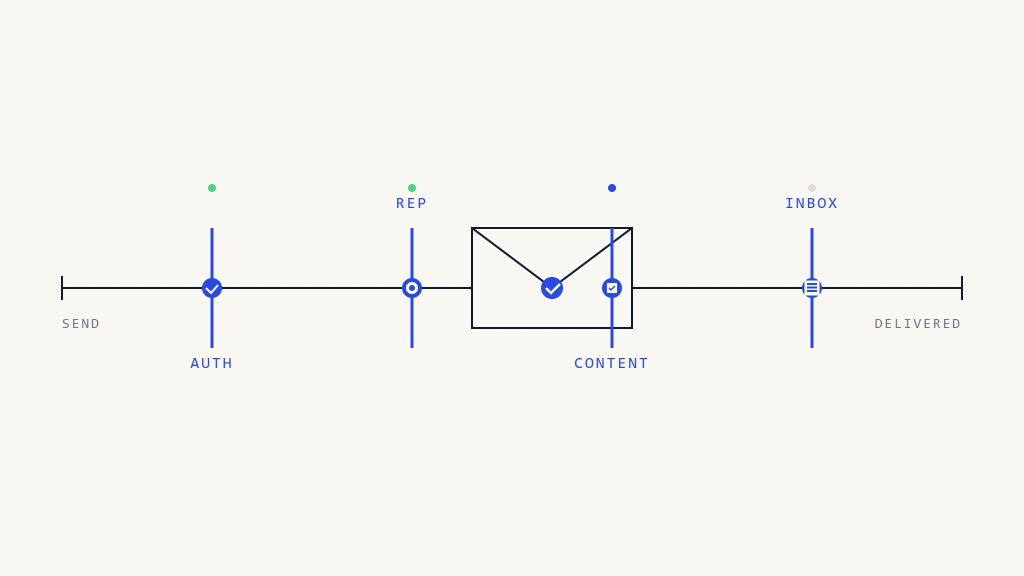
Read the analysisThe standards that prove who you are — and the practices that keep you in the inbox.
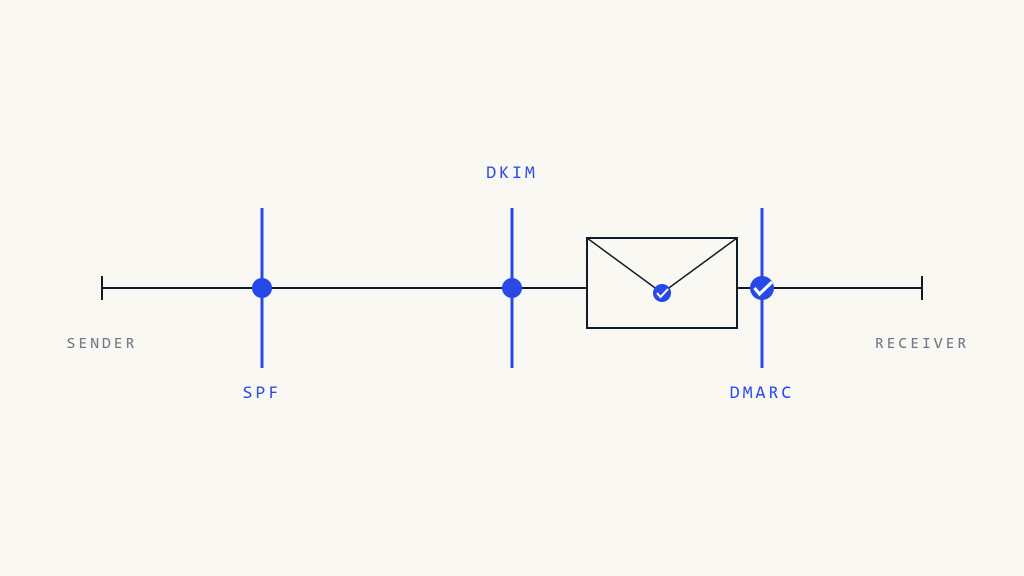
Learn DMARC fundamentals: how email authentication works, implementation steps, and protection against spoofing in 2026. Complete guide for security teams.
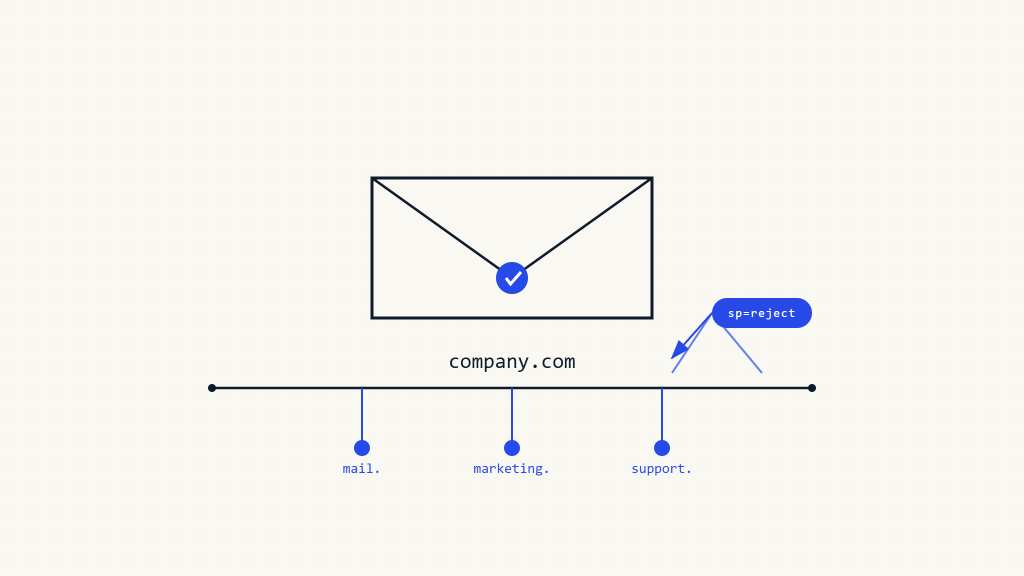
Master DMARC subdomain policies and sp tag configuration for comprehensive email security beyond root domains. Expert implementation guide.
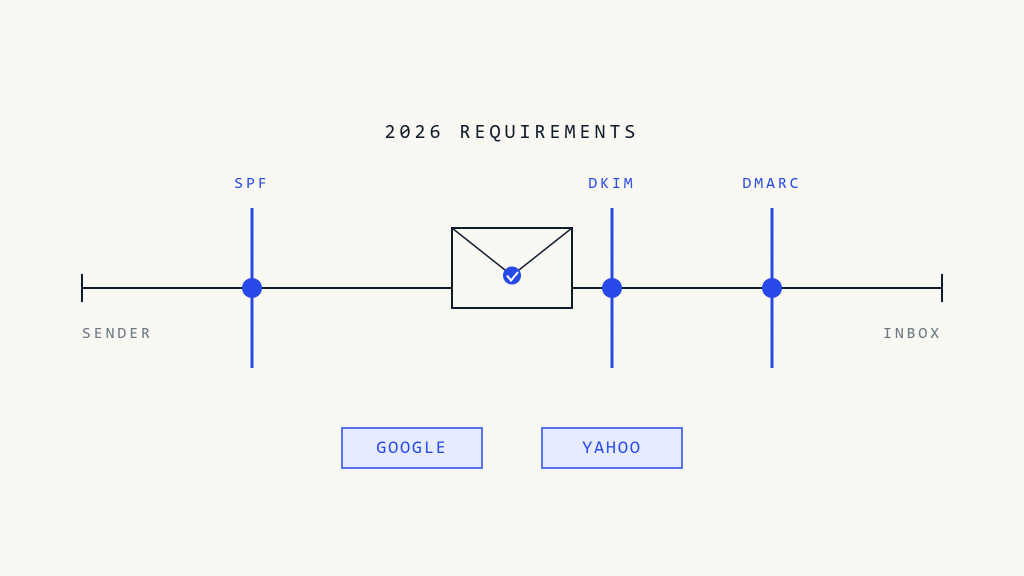
Master Google and Yahoo's latest email authentication requirements for 2026. Complete guide to SPF, DKIM, and DMARC compliance for bulk…
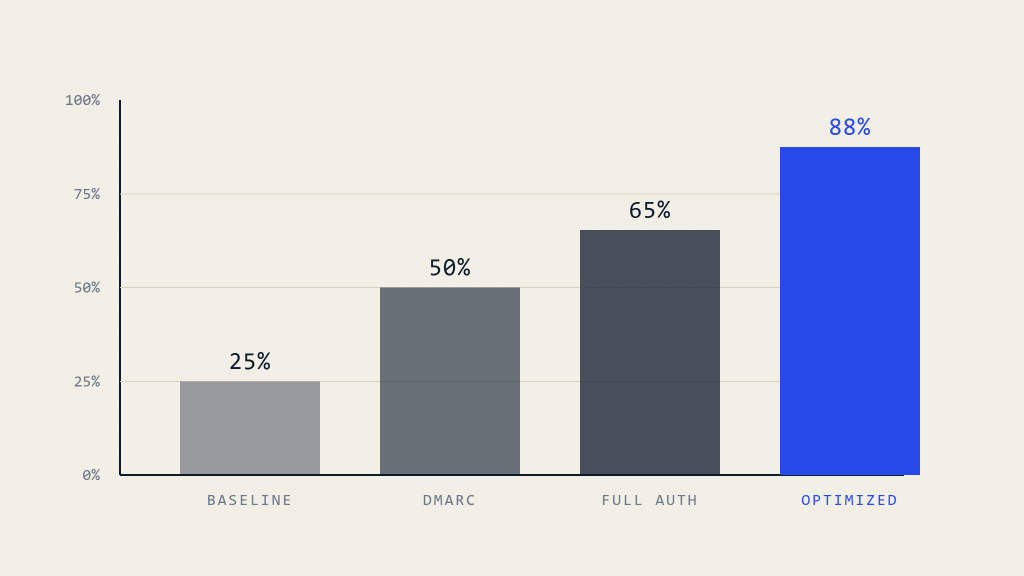
Maximize email inbox delivery with data-driven DMARC strategies. Complete guide to improving inbox placement rates and email deliverability optimization.
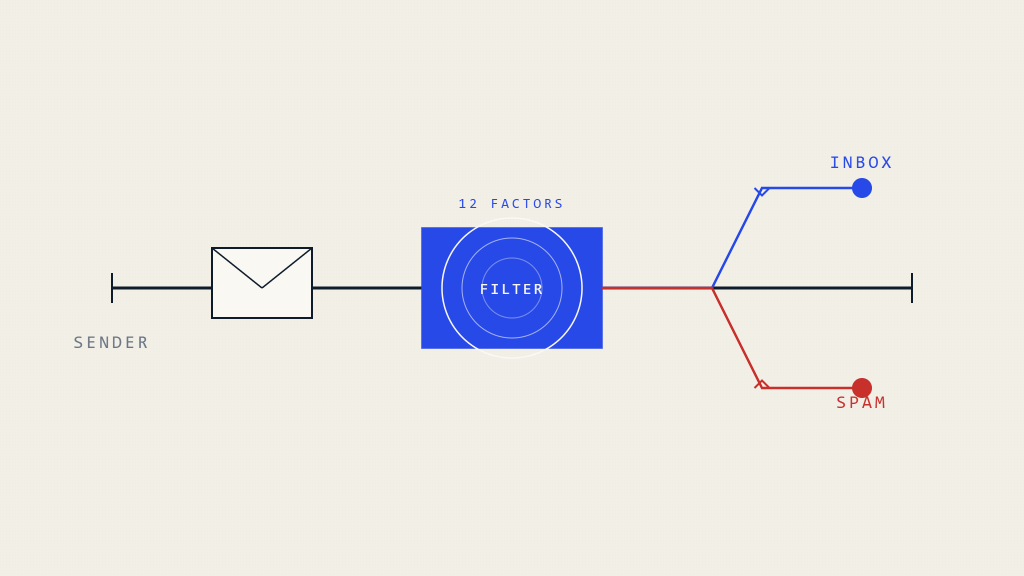
Understanding why emails go to spam is crucial for effective digital communication. Modern filtering systems analyze hundreds of factors beyond…
Complete troubleshooting guide for diagnosing and resolving email deliverability problems, inbox placement issues, and authentication failures in 2026.

Learn 7 essential steps to protect your organization from phishing attacks with comprehensive email security strategies and actionable prevention measures.
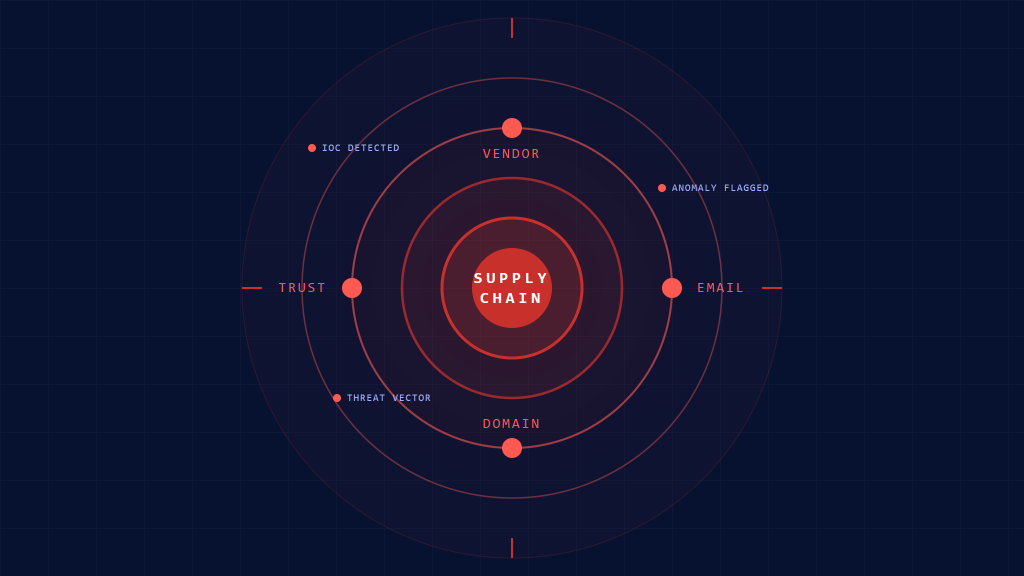
Essential indicators of compromise for detecting supply chain email threats. Complete checklist for identifying and responding to sophisticated vendor-based attacks.

The Louvre’s jewel heist exposed more than a security breach - it revealed a digital failure. Outdated systems, weak passwords,…
DMARC providers using non-EU processors create privacy compliance risks for European organizations. Learn how to prevent data exposure and maintain regulatory compliance.
Complete guide to PCI DSS 4.0 email security requirements. Learn implementation steps, compliance validation, and best practices for payment card security.
Complete checklist for implementing SOC 2 Type II email security controls. Essential authentication, encryption, and monitoring requirements for compliance certification.
Learn how DMARC email authentication supports GDPR compliance goals, protects personal data, and strengthens your email marketing security framework.
Hands-on technical guides and notes on industry solutions from the team.
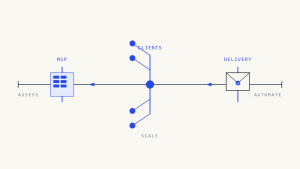
Comprehensive checklist for MSPs managing email authentication across multiple clients. Covers assessment, implementation, and automation strategies for scalable deliverability.

Transform chaotic email security management into streamlined, centralized DMARC control that scales with your MSP business across multiple client domains.
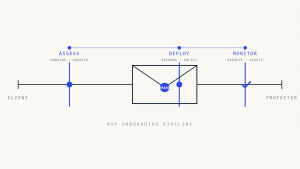
Complete checklist for MSPs deploying DMARC across new client portfolios. Streamline implementation with assessment, deployment, and automation strategies.

Systematic troubleshooting workflow for MSPs managing DMARC deployments across multiple client domains with infrastructure-wide visibility and rapid issue resolution.
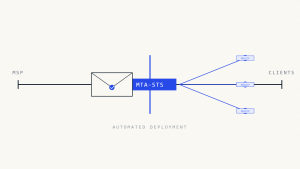
Learn scalable MTA-STS deployment strategies for MSPs managing multiple client environments. Complete implementation guide with automation and monitoring.
In enterprise environments, maintaining control of email security depends less on individual protocols and more on clear ownership and consistent management of authentication controls.
The newsroom feed — Skysnag platform releases and what's moving in email security, filed as it happens.
Discover how confidence-scored SPF enforcement with guided operator control centers revolutionizes DNS security management and email protection.
Skysnag releases its Look-Alike Domain Checker, empowering businesses to detect impersonation threats, prevent phishing, and protect their brand identity.
The Skysnag Integrations Center makes it easy for marketers to protect and improve email deliverability. With autonomous integrations to thousands of sending services, you can resolve issues faster and ensure…
Skysnag has launched a new blog dedicated to email authentication, security, and compliance. Discover expert insights, industry updates, and best practices on DMARC, SPF, and DKIM to help organizations strengthen…
Discover what MSSPs need from a DMARC solution in 2026, including email authentication standards, provider requirements, multi-tenant management, and high-margin revenue opportunities.
Cybercrime in 2026 is evolving into a patient, human-driven threat. From AI-generated phishing to identity leaks, attackers are using precision and psychology to exploit trust. Discover how businesses can strengthen…
As organizations expand, their digital footprint grows, so do their risks. Mismanaged domains and subdomains can become hidden entry points for phishing and impersonation attacks. Learn how consistent email authentication,…
BEC attacks exploit trust to bypass traditional defenses. Learn how to secure your domain with proactive email authentication that stops impersonation at the source.
A weekly dispatch for security leaders, MSPs, and deliverability engineers. Threat advisories, standards movement, and one piece of long-form analysis — edited by the Skysnag research group.
No marketing sequences. Unsubscribe in one click. Skysnag's privacy posture is SOC 2 Type II & GDPR-aligned.