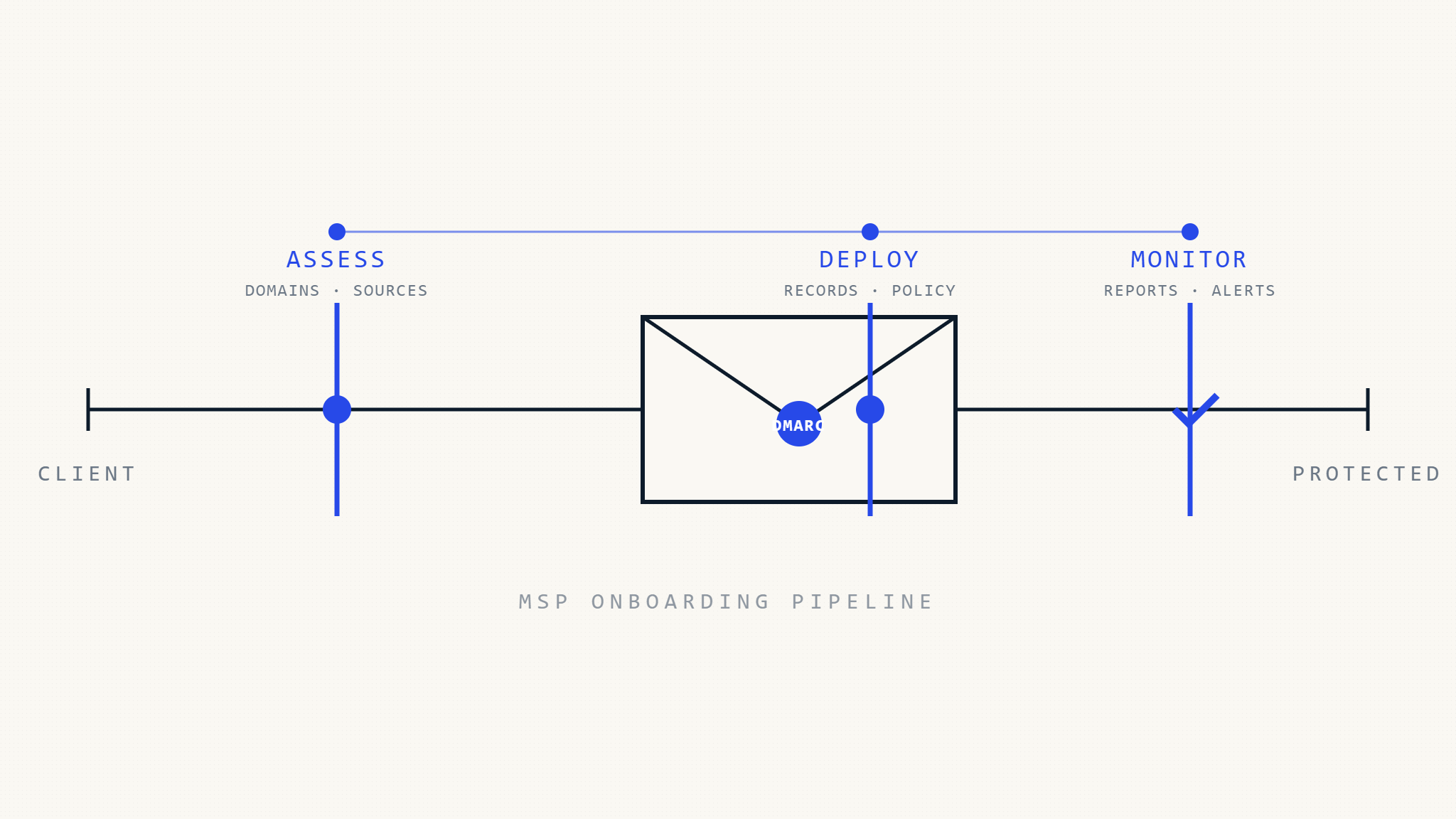
Onboarding new clients presents MSPs with a critical opportunity to establish strong email security foundations from day one. DMARC implementation during client onboarding ensures immediate protection against domain spoofing while positioning your MSP as a proactive security partner. This comprehensive checklist streamlines DMARC deployment across client portfolios, reducing implementation time while maintaining security standards.
I. Assessment Phase: Evaluating Client Email Infrastructure
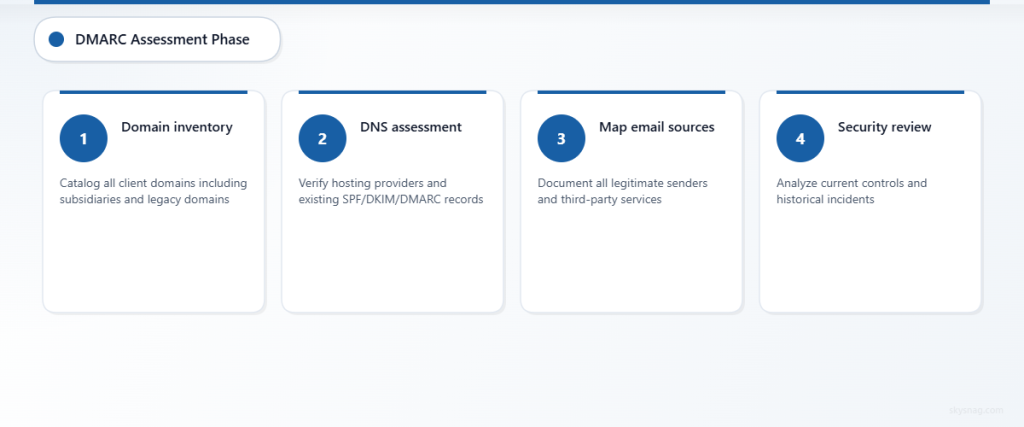
Domain Discovery and Inventory
- [ ] Catalog all client domains and subdomains
- Document primary business domains
- Identify subsidiary and departmental domains
- Map legacy domains still in use
- Note domains used for marketing campaigns
- [ ] Assess current DNS infrastructure
- Verify DNS hosting provider and access credentials
- Document TTL settings for existing records
- Check for any existing SPF, DKIM, or DMARC records
- Identify DNS management workflow and approval processes
- [ ] Evaluate email sending sources
- Map legitimate email services (Office 365, Google Workspace, on-premises Exchange)
- Document third-party services (marketing platforms, CRM systems, notification services)
- Identify shadow IT email services
- Assess mobile device management and BYOD policies
Security Posture Analysis
- [ ] Review existing email security controls
- Document current anti-phishing solutions
- Assess email gateway configurations
- Review user security awareness training programs
- Evaluate incident response procedures for email threats
- [ ] Analyze historical email security incidents
- Review any previous domain spoofing attempts
- Document user-reported phishing incidents
- Assess business impact of email-based attacks
- Identify patterns in attack vectors
II. Actions Phase: DMARC Deployment Strategy
Foundation Setup
- [ ] Configure SPF records for all domains
- Implement SPF records with appropriate mechanisms
- Ensure include statements cover all legitimate senders
- Set hard fail (-all) after validation testing
- Document SPF lookup chain to avoid 10-lookup limit
- [ ] Deploy DKIM authentication
- Generate DKIM keys for primary email services
- Configure DKIM signing in email platforms
- Publish DKIM public keys in DNS
- Verify DKIM signatures on test messages
- [ ] Implement initial DMARC policy
- Start with monitoring policy (p=none) for visibility
- Configure aggregate report collection
- Set forensic reporting for detailed analysis
- Establish report processing workflow
Multi-Client Management Strategy
- [ ] Standardize deployment procedures
- Create templated DNS record configurations
- Develop client communication templates
- Establish change management processes
- Document rollback procedures for issues
- [ ] Implement monitoring infrastructure
- Configure centralized DMARC report collection
- Set up automated report parsing and analysis
- Establish alerting for policy violations
- Create client reporting dashboards
Skysnag MSP/MSSP Comply provides multi-tenant management capabilities that streamline DMARC deployment across client portfolios. The platform automates report collection and analysis while providing white-label client reporting options.
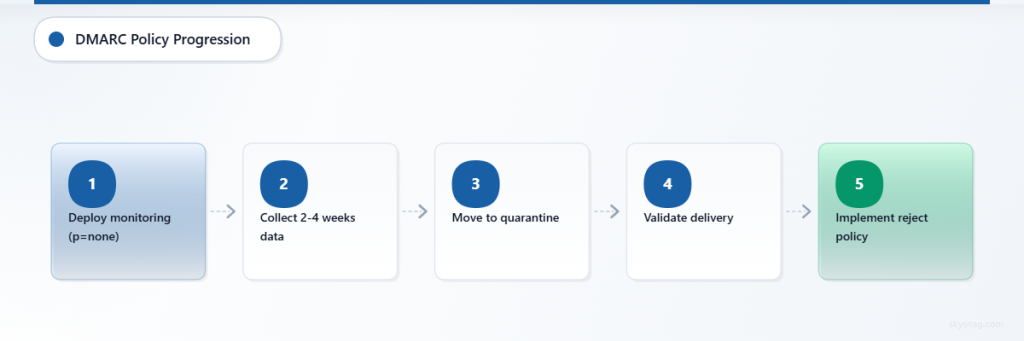
Policy Progression Framework
- [ ] Phase 1: Monitoring (p=none)
- Deploy monitoring policy across all domains
- Collect 2-4 weeks of aggregate data
- Identify all legitimate email sources
- Address any authentication failures
- [ ] Phase 2: Quarantine (p=quarantine)
- Transition to quarantine policy after validation
- Monitor for delivery issues or false positives
- Adjust SPF and DKIM configurations as needed
- Communicate policy changes to client stakeholders
- [ ] Phase 3: Reject (p=reject)
- Implement reject policy for maximum protection
- Establish ongoing monitoring procedures
- Create incident response workflows
- Document compliance evidence for audits
III. Automate Phase: Scaling DMARC Management
Automated Monitoring and Analysis
- [ ] Deploy automated report processing
- Configure real-time DMARC report ingestion
- Set up automated source identification
- Implement threat intelligence correlation
- Establish automated alerting workflows
- [ ] Create standardized reporting
- Develop executive-level security dashboards
- Implement automated compliance reporting
- Configure client-specific report delivery
- Establish KPI tracking and trending
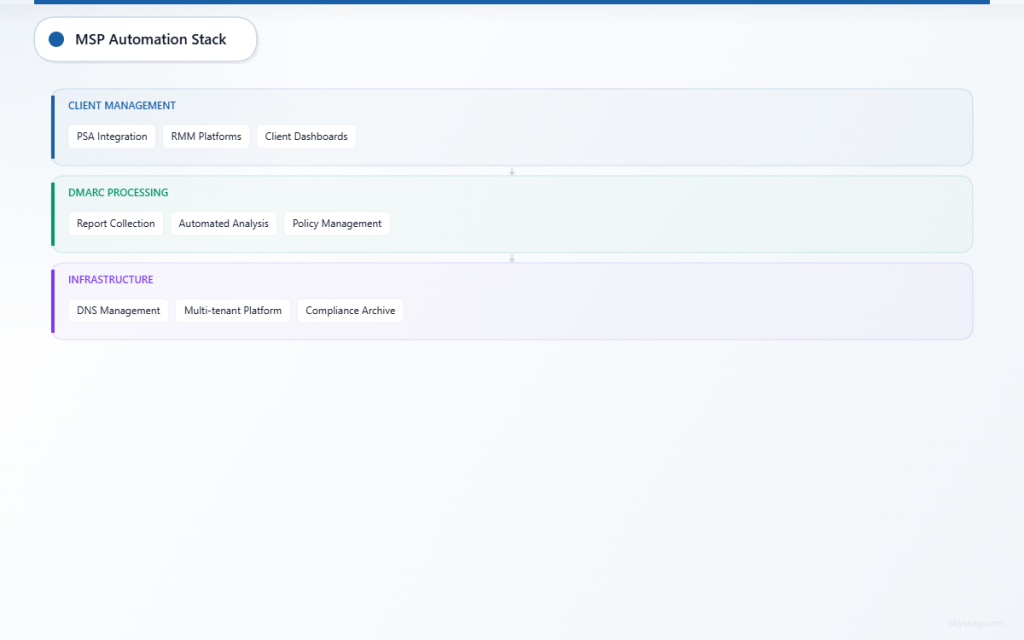
Integration with MSP Operations
- [ ] Connect to PSA and RMM platforms
- Integrate DMARC monitoring with existing tools
- Automate ticket creation for policy violations
- Configure client notification workflows
- Establish billing integration for security services
- [ ] Implement change management automation
- Automate DNS record deployment
- Configure policy progression workflows
- Implement backup and recovery procedures
- Establish audit trail documentation
Compliance and Documentation Automation
- [ ] Automate compliance evidence collection
- Configure automated report archiving
- Implement policy compliance tracking
- Generate audit-ready documentation
- Establish retention policy management
- [ ] Create client onboarding templates
- Develop standardized implementation timelines
- Create client education materials
- Establish success metrics and KPIs
- Document best practices and lessons learned
IV. Advanced Client Management Strategies
Service Tier Differentiation
Different client segments may require varying levels of DMARC protection and monitoring:
Basic Tier: Standard DMARC implementation with monthly reporting
Premium Tier: Advanced threat intelligence integration and real-time monitoring
Enterprise Tier: Custom policy management and dedicated security consultation
Regulatory Compliance Considerations
Many clients face specific compliance requirements that DMARC implementation supports:
- Financial services organizations benefit from enhanced anti-phishing controls
- Healthcare clients can demonstrate email security due diligence
- Government contractors may need to meet specific cybersecurity frameworks
Client Communication and Training
- [ ] Develop client education programs
- Create DMARC awareness training materials
- Establish regular security briefings
- Provide incident response training
- Document security best practices
- [ ] Implement feedback mechanisms
- Regular client satisfaction surveys
- Quarterly security posture reviews
- Continuous improvement processes
- Benchmarking against industry standards
Skysnag MSP/MSSP Comply enables MSPs to deliver consistent DMARC implementation across their client base while maintaining centralized visibility and control. The platform’s automated reporting and white-label capabilities support scalable service delivery models.
V. Key Takeaways
Successful DMARC implementation during MSP client onboarding requires systematic assessment, phased deployment, and automated management. By following this checklist, MSPs can establish strong email security foundations while positioning themselves as trusted security advisors.
The assessment phase ensures comprehensive understanding of client email infrastructure, while the actions phase provides structured deployment methodology. Automation enables scalable management across growing client portfolios while maintaining consistent security standards.
MSPs that implement standardized DMARC onboarding processes demonstrate proactive security leadership while creating opportunities for expanded security service offerings. This systematic approach to email authentication establishes the foundation for comprehensive cybersecurity partnerships.