The German Federal Office for Information Security (BSI) sets rigorous standards for cybersecurity in Germany, particularly for critical infrastructure and government entities. Organizations subject to BSI oversight must carefully evaluate their DMARC implementation to ensure alignment with German cybersecurity requirements and broader European regulatory frameworks.
This comprehensive guide outlines the essential criteria for selecting BSI-compliant DMARC solutions and provides practical implementation guidance for German organizations navigating complex regulatory requirements.
I. Understanding BSI DMARC Compliance Requirements
BSI Framework Overview
The BSI (Bundesamt für Sicherheit in der Informationstechnik) establishes cybersecurity standards that emphasize risk management, technical safeguards, and operational security controls. While BSI standards don’t explicitly mandate specific email authentication protocols, they strongly emphasize protecting against unauthorized access and maintaining communication integrity.
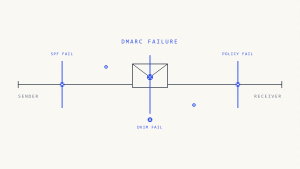
DMARC implementation supports BSI objectives by:
- Preventing email-based social engineering attacks
- Maintaining organizational communication integrity
- Providing audit trails for security incidents
- Supporting incident response and forensic analysis
Regulatory Context
Organizations implementing DMARC under BSI guidance must also consider:
NIS2 Directive Alignment: The Network and Information Security Directive emphasizes cybersecurity risk management, which email authentication directly supports.
GDPR Considerations: Data protection requirements affect how DMARC reports are collected, processed, and stored, particularly when handling personal identifiable information.
Sector-Specific Requirements: Critical infrastructure operators may face additional email security obligations under German cybersecurity law.
II. Essential DMARC Software Requirements for BSI Compliance
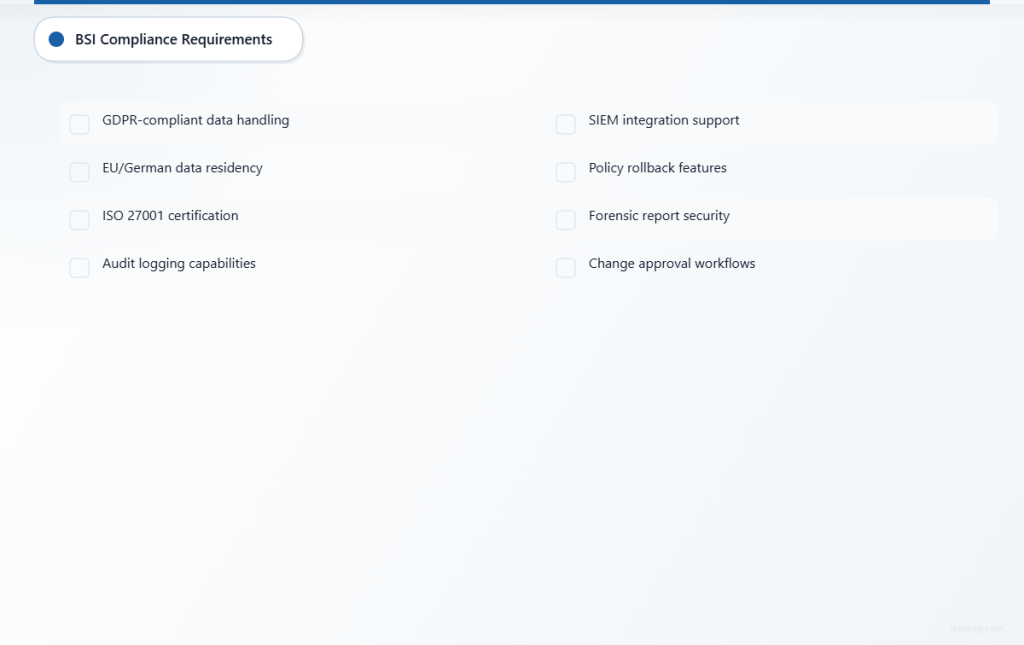
Core Technical Capabilities
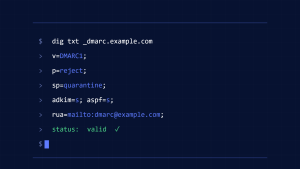
1. Policy Management and Enforcement
Granular Policy Controls
- Support for incremental policy deployment (none → quarantine → reject)
- Subdomain-specific policy configuration
- Percentage-based rollout capabilities
- Emergency policy modification procedures
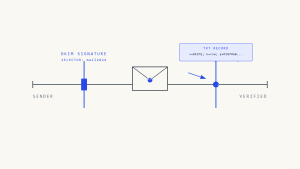
Alignment Requirements
- SPF alignment configuration (relaxed and strict modes)
- DKIM alignment settings with domain validation
- Multi-domain policy management for complex organizational structures
2. Comprehensive Reporting and Analytics
Aggregate Report Processing
- Automated collection from all major email providers
- Real-time parsing and analysis capabilities
- Historical trend analysis with configurable time periods
- Source authentication validation
Forensic Report Handling
- Secure collection and storage of failure samples
- Automated redaction of sensitive information
- Incident correlation with other security tools
- Chain-of-custody documentation for potential investigations
Security and Data Protection Features
3. Privacy-Compliant Data Handling
GDPR Alignment
- Data minimization in report collection
- Automated personal data detection and handling
- Configurable data retention periods
- Subject access request capabilities
- Right to erasure implementation
Secure Data Processing
- End-to-end encryption for report transmission
- Secure storage with access controls
- Audit logging for all data access
- Geographic data residency options (German/EU hosting)
4. Integration and Automation Capabilities
SIEM Integration
- Real-time alert generation for policy violations
- Standardized log formats (CEF, LEEF, JSON)
- API connectivity for security orchestration
- Correlation with other email security events
Change Management
- Automated backup of configuration changes
- Approval workflows for policy modifications
- Rollback capabilities for failed deployments
- Integration with ITIL-compliant change processes
III. Implementation Architecture Requirements
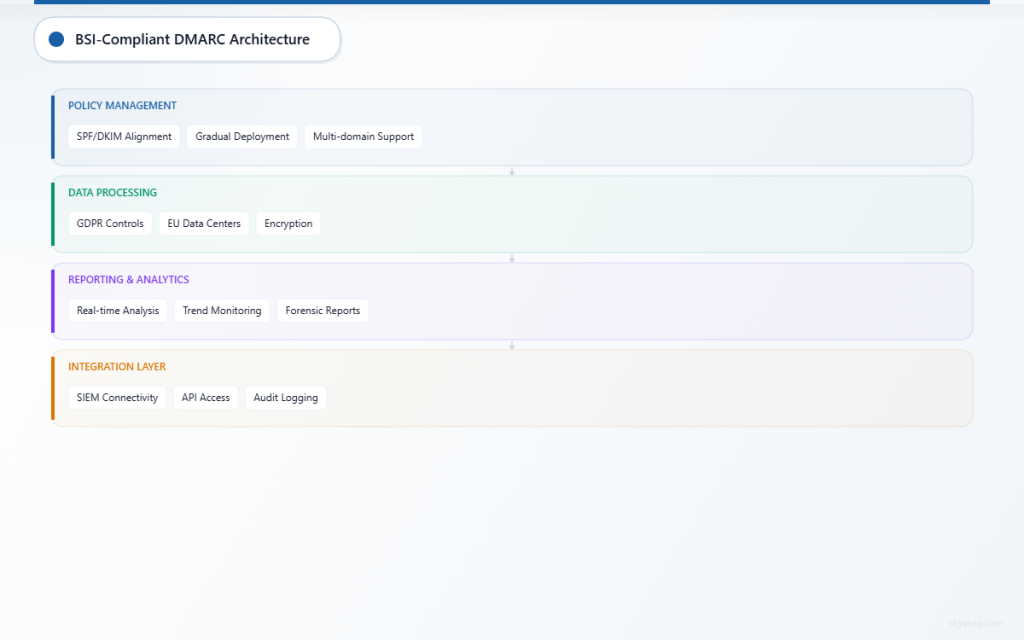
Infrastructure Considerations
1. Deployment Models
On-Premises Requirements
- Dedicated hardware specifications for report processing
- Network segmentation and firewall configuration
- Database sizing for long-term report storage
- Backup and disaster recovery procedures
Cloud-Based Considerations
- German or EU data center locations
- Compliance certifications (ISO 27001, SOC 2)
- Data processing agreements (DPA) under GDPR
- Service level agreements with security provisions
2. Scalability and Performance
Volume Handling
- Processing capacity for enterprise-scale email volumes
- Burst processing capabilities during report collection windows
- Database optimization for large datasets
- Automated scaling for growing organizations
Vendor Evaluation Criteria
3. Compliance Documentation
Certification Requirements
- ISO 27001 information security management
- SOC 2 Type II controls validation
- BSI-recognized security frameworks
- Third-party security assessments
Documentation Standards
- Detailed security architecture documentation
- Data processing and retention policies
- Incident response procedures
- Business continuity plans
IV. Step-by-Step Implementation Guide
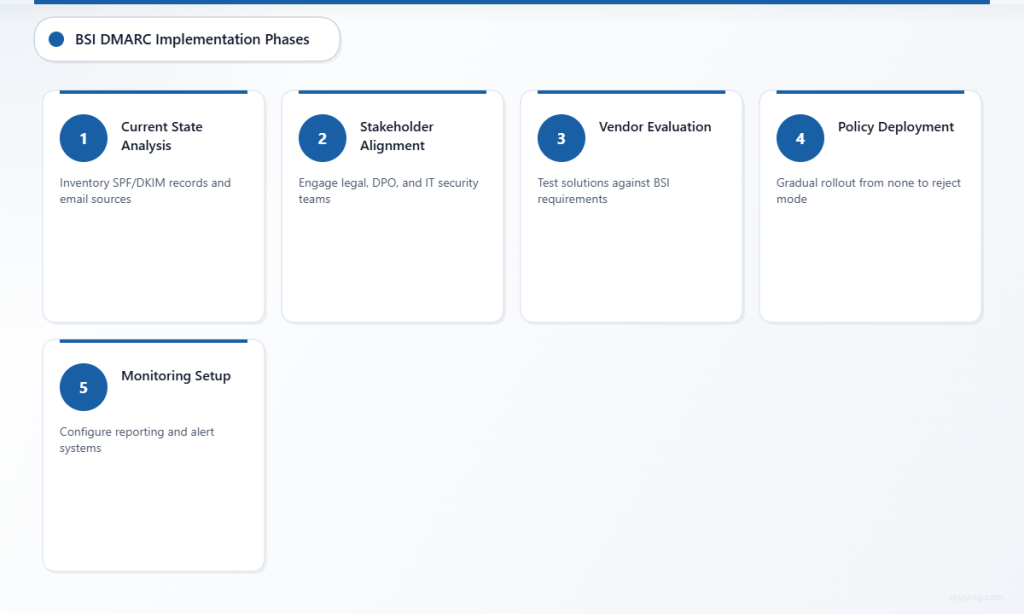
Phase 1: Pre-Implementation Assessment
1. Current State Analysis
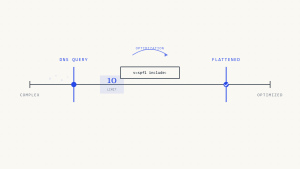
- Inventory existing email authentication records
- Document current SPF and DKIM implementations
- Identify all legitimate email sources
- Assess organizational change management processes
2. Stakeholder Alignment
- Engage legal team for compliance review
- Coordinate with data protection officer
- Align with IT security policies
- Establish cross-functional project team
Phase 2: Solution Selection and Configuration
3. Vendor Evaluation Process
- Request detailed compliance documentation
- Conduct proof-of-concept testing
- Validate technical requirements
- Review contractual terms for BSI alignment
4. Initial Configuration
- Configure aggregate report collection
- Establish baseline monitoring
- Implement initial policy at “none” enforcement
- Set up alerting and notification systems
Phase 3: Gradual Policy Enforcement
5. Monitoring and Analysis
- Review aggregate reports for authentication failures
- Identify and authorize legitimate email sources
- Document policy violation patterns
- Establish baseline metrics for ongoing monitoring
6. Progressive Enforcement
- Implement quarantine policy for small percentage of traffic
- Monitor impact on legitimate email delivery
- Gradually increase enforcement percentage
- Document policy changes for audit purposes
Phase 4: Full Enforcement and Optimization
7. Complete Policy Enforcement
- Deploy reject policy after thorough validation
- Monitor for any legitimate email blocking
- Implement exception handling procedures
- Establish ongoing monitoring protocols
V. Skysnag Protect: BSI-Compliant DMARC Implementation
Skysnag Protect provides comprehensive DMARC management capabilities designed to support BSI compliance requirements. The platform offers:
Privacy-First Architecture: European data hosting with GDPR-compliant data processing and automated personal information handling.
Advanced Policy Management: Granular controls for progressive policy deployment with detailed audit trails and change management workflows.
Comprehensive Reporting: Real-time analytics with customizable dashboards, automated alerting, and integration capabilities for German organizations.
Regulatory Alignment: Built-in features supporting BSI objectives, NIS2 requirements, and sector-specific compliance needs.
VI. Best Practices for Ongoing Compliance
Continuous Monitoring
Performance Metrics
- Authentication success rates across all email channels
- Policy violation trends and patterns
- Source authentication compliance rates
- Delivery impact assessment
Compliance Validation
- Regular review of BSI guidance updates
- Periodic assessment of technical controls
- Documentation of compliance evidence
- Third-party validation where required
Incident Response Integration
Alert Configuration
- Real-time notifications for policy violations
- Escalation procedures for security incidents
- Integration with existing security operations
- Forensic evidence collection procedures
VII. Key Takeaways
BSI DMARC compliance requires careful attention to both technical implementation and regulatory alignment. Organizations must select solutions that provide comprehensive policy management, privacy-compliant data handling, and robust integration capabilities.
Success depends on following a structured implementation approach, maintaining detailed documentation, and ensuring ongoing monitoring aligned with BSI cybersecurity objectives. The investment in proper DMARC implementation supports broader organizational security goals while meeting German regulatory requirements.
Ready to implement BSI-compliant DMARC? Explore Skysnag Protect to see how our platform supports German organizations with comprehensive email authentication management designed for regulatory compliance.