Security
SPF, DKIM, DMARC, BIMI, MTA-STS, and TLS-RPT — standards, guidance, and enforcement strategy for the enterprise inbox.
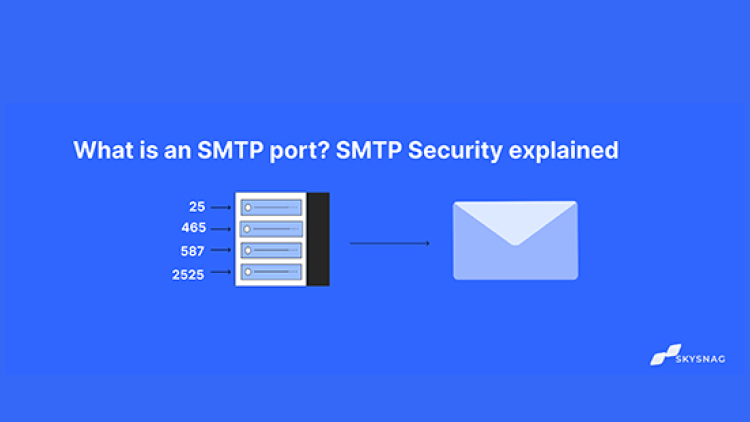
What is an SMTP port? SMTP Security explained
Are you currently configuring an SMTP service and have just come across a port field that you are unsure of how to fill out? We're here to help. In this article, we'll take a deep dive into SMTP port and Why...
Read the article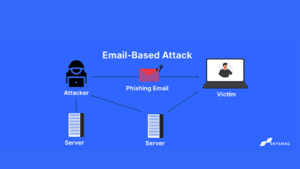
Example of Email-Based Attacks
Over a billion individuals use email on a daily basis across the world. Email has grown to be a significant...

History of Email
There are many fascinating tales and innovative technologies throughout the history of email. In the timeline below, we’ve highlighted 24...

Multiple SPF records on a domain?
Can more than one SPF record be present on the same domain? The answer is no; if a domain contains...
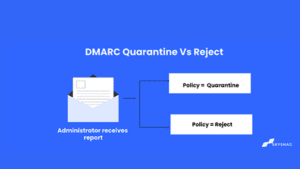
DMARC Quarantine Vs Reject: What’s the difference?
What is the difference between the DMARC policies quarantine and reject, and what will happen when I publish these policies?...

What is Phishing?
Phishing is when cybercriminals send malicious emails to scam internet users. It is a form of social engineering in which scammers use human psychology...
How to Reach a DMARC Reject Policy
In this article, we provide you with a step-by-step guide on how to enforce the DMARC policy and discuss whether...
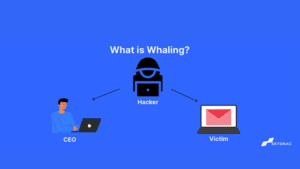
What is Whaling? and how to prevent it?
As cyberattacks develop, more sophisticated methods of data breach are affecting a lot more businesses. Due to the COVID-19 pandemic...

How to prevent Email Spoofing.
Spoofing emails is one of the most frequent sorts of hacker behavior that includes email exchanges. Everything you need to...
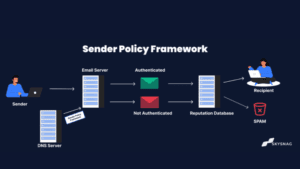
What is Sender Policy Framework (SPF)
What is SPF SPF(Sender Policy Framework) is an email authentication protocol that domain admins deploy to prevent spammers from spoofing their domain....
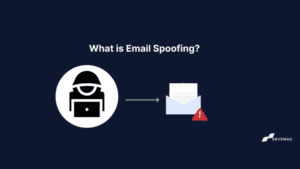
What is Email Spoofing?
Email spoofing is the creation of email messages with a forged sender address. This indicates that the message looks to...

Emails from MailChimp still continue to land in SPAM?
There have been complaints about issues while utilizing MailChimp and SPF. Because MailChimp employs a shared IP address for all...
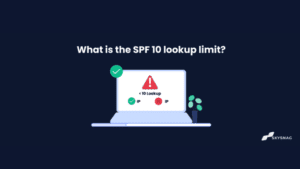
What is the SPF 10 lookup limit?
What is an SPF lookup? An SPF lookup is when the receiving mail server checks to see if the IP...
Check your domain's DMARC compliance.
Five protocols. Sixty seconds. No account. A full authentication-posture report on your domain, delivered before your coffee cools.


