Skysnag automatically applies default authentication to your marketing emails in order to improve deliverability. In order to safeguard email senders and recipients against spam, and phishing, Skysnag has automated DomainKeys Identified Mail (DKIM) authentication for you.
You’ll discover the advantages of email authentication and how it works to fight BEC. We’ll start with the basics but feel free to jump ahead with the links below.
I. Table of Contents
- What is BEC?
- Impact of BEC on organizations
- How does email authentication work to fight BEC?
- Email authentication relies on basic standards
- Configure DMARC for your domain
- Conclusion
II. What is BEC?
BEC, or business email compromise, is a cyberattack that targets organizations of all sizes. These attacks are carried out by impersonating persons in positions of authority, such as the CEO or CFO, to defraud the organization.
III. Impact of BEC on organizations
The severity of these risks is highlighted in a public service announcement published by the FBI. Losses due to BEC amounted to 55.5 billion dollars from 2013 until 2023.
The impact of BEC on organizations can be both direct and indirect. The direct impact is typically financial, as organizations may lose money as a result of BEC scams. The indirect impact can be more far-reaching, as BEC can damage an organization’s reputation and relationships with customers, suppliers, and other partners. In some cases, BEC can also lead to regulatory problems or legal action.
IV. How does email authentication work to fight BEC?
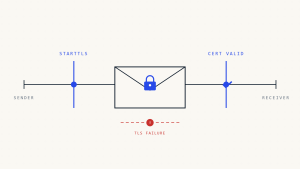
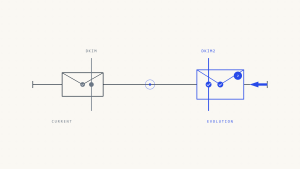
Email authentication works by verifying that an email message has not been tampered with and that it really comes from the sender that it claims to come from. When an email is sent, the sending email server attaches a digital signature to the message. This signature contains information that can be used to verify the authenticity of the message. When the receiving email server receives the message, it uses the information in the signature to verify that the message is from the sender that it claims to be from and that the message has not been tampered with.
V. Email authentication relies on basic standards
The most commonly used email authentication standards are SPF, DKIM, and DMARC. These standards were designed to supplement SMTP, the basic protocol used to send email, because SMTP does not itself include any authentication mechanisms.
- Skysnag automates SPF allowing senders to define which IP addresses are allowed to send mail for a particular domain.
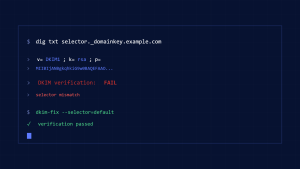
- Skysnag’s automated DKIM provides an encryption key and digital signature that verifies that an email message was not faked or altered.
- DMARC unifies the SPF and DKIM authentication mechanisms into a common framework and allows domain owners to declare how they would like an email from that domain to be handled if it fails an authorization test.
VI. Configure DMARC for your domain
In a time where BEC losses are at an all-time high, domain owners are left responsible for email authentication, there is not a one-size-fits-all answer to this question, as the configuration of DMARC will vary depending on the specific domain and mail server environment.
Create a Skysnag account to generate your DMARC record.
VII. Conclusion
Skysnag offers a complete, end-to-end solution to stop business email compromise (BEC). We examine numerous email fraud attack strategies, including email spoofing, spamming, and phishing. Skysnag automates DMARC authentication to defend your company’s reputation from BEC fraud.
With the help of our automated software, you gain automatic threat detection and response as well as visibility across a number of threat channels, including your supply chain. Sign up for a free trial today.