Security
SPF, DKIM, DMARC, BIMI, MTA-STS, and TLS-RPT — standards, guidance, and enforcement strategy for the enterprise inbox.
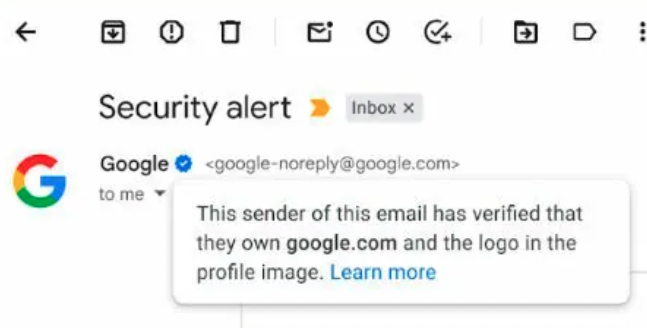
Path to Google’s Blue Verification Checkmark through Email Authentication
In response to the need for email authentication to protect companies from spoofing and solve deliverability issues, Google has taken a significant step forward by introducing verified blue checkmarks for senders in Gmail. With the new update, users will see...
Read the article
SMTP TLS REPORTING
The SMTP TLS reporting is a tool to identify probable misconfigurations. SMTP is a communication channel for sending electronic mail....

5 Steps to Detecting Phishing at a Glance
We all know that phishing is not a new concept. It is a common phenomenon that has plagued internet users for many...
19 DMARC myths debunked by the experts
Many people don’t instantly understand what DMARC accomplishes or how it protects against fraud, impersonation, and domain spoofing. There are...
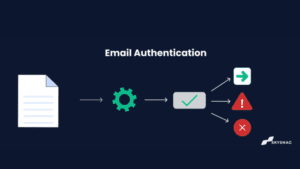
Intro to Email Authentication: 2024
What is email authentication? Email authentication is the process of verifying that an email comes from the sender that it...
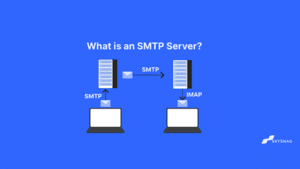
What Is an SMTP Server, and How Does It Work?
Although emailing is a popular means of communication for both organizations and individuals, have you ever paused to consider what...

What is BIMI?
The one tactic that increases your visibility in front of subscribers and increases the likelihood that your message will be...
What is Business Email Compromise(BEC)?
It is no surprise that the FBI has labeled Business Email Compromise (BEC) a “$26 billion fraud,” with an average...
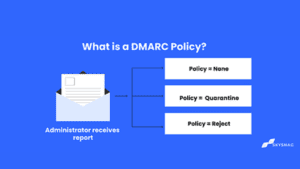
What is a DMARC Policy?
DMARC POLICY? A DMARC policy is an email authentication policy that allows domain owners to specify how their emails should...

What is email spam and how to prevent it
A Guide to recognizing and preventing Spam Emails For internet users, spam is not a new word. Spam emails are...

Ten DMARC myths ready to be debunked
The internet is a great resource for finding information on a variety of topics; however, it is important to be...
Check your domain's DMARC compliance.
Five protocols. Sixty seconds. No account. A full authentication-posture report on your domain, delivered before your coffee cools.


