ISO 27001 certification requires organizations to implement comprehensive information security controls, and email systems represent a critical component of this framework. Email authentication controls and monitoring mechanisms play a vital role in demonstrating compliance with ISO 27001’s security management requirements, particularly in protecting against unauthorized access and ensuring information integrity.
This technical reference provides security professionals with actionable guidance on implementing email controls that support ISO 27001 certification objectives, covering authentication protocols, monitoring frameworks, and evidence collection strategies.
I. Understanding ISO 27001 Email Security Requirements
ISO 27001 does not prescribe specific email authentication technologies like DMARC, SPF, or DKIM. Instead, the standard establishes risk-based security objectives that organizations must address through appropriate controls. Email authentication and monitoring controls support several key ISO 27001 control objectives:
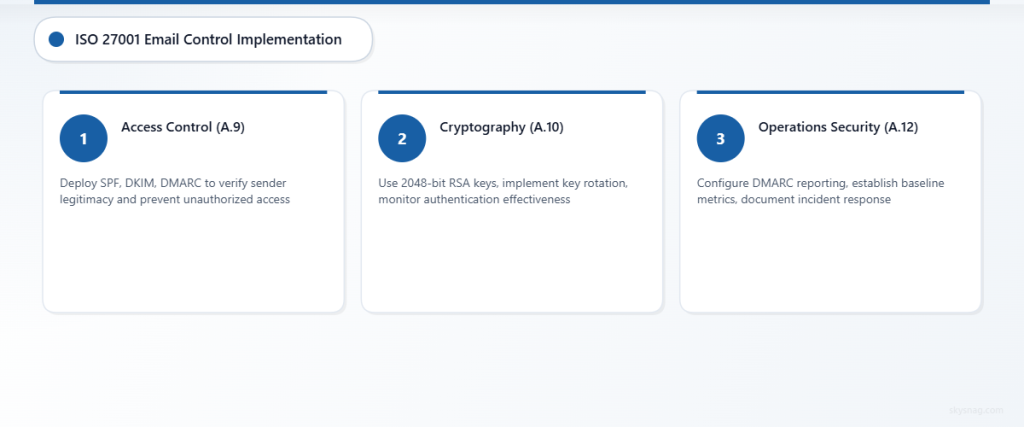
Access Control (A.9)
Organizations must implement controls to limit access to information and information processing facilities. Email authentication protocols help verify sender legitimacy and prevent unauthorized access to email communications.
Control Implementation Approach:
- Deploy SPF records to authorize sending IP addresses
- Configure DKIM signing for message integrity verification
- Implement DMARC policies to define authentication failure handling
- Monitor authentication results for access control effectiveness
Cryptography (A.10)
The standard requires proper use of cryptography to protect information confidentiality, authenticity, and integrity. Email authentication leverages cryptographic mechanisms to achieve these objectives.
Technical Implementation:
- DKIM uses RSA or ECDSA cryptographic signatures for message authentication
- Configure minimum key lengths (2048-bit RSA recommended)
- Implement key rotation schedules for DKIM signing keys
- Monitor cryptographic control effectiveness through authentication reporting
Operations Security (A.12)
ISO 27001 emphasizes correct and secure operation of information processing facilities. Email security monitoring falls under operational security controls.
Monitoring Framework:
- Implement DMARC reporting for authentication visibility
- Configure SPF and DKIM failure alerting
- Establish baseline metrics for email authentication success rates
- Document incident response procedures for authentication failures
II. Email Authentication Protocol Implementation

SPF (Sender Policy Framework) Configuration
SPF records define authorized sending sources for your domain, supporting ISO 27001 access control objectives.
Basic SPF Syntax:
v=spf1 include:_spf.skysnag.com ip4:203.0.113.1 -allImplementation Requirements:
- Document all legitimate sending sources
- Use restrictive policies (-all mechanism)
- Implement monitoring for SPF authentication failures
- Maintain change control procedures for SPF record updates
ISO 27001 Alignment:
SPF implementation supports A.9.1.1 (Access control policy) by defining authorized email senders and A.12.4.1 (Event logging) through authentication result logging.
DKIM (DomainKeys Identified Mail) Deployment
DKIM provides cryptographic authentication for email messages, supporting information integrity objectives.
DKIM Record Structure:
selector._domainkey.example.com. IN TXT "v=DKIM1; k=rsa; p=MIGfMA0GCSqGSIb3DQEBAQUAA..."Configuration Parameters:
- Key Length: Minimum 2048-bit RSA keys
- Selector Rotation: Implement quarterly key rotation
- Signing Scope: Sign critical headers (From, Subject, Date, Message-ID)
- Hash Algorithm: Use SHA-256 for signature generation
Control Evidence:
Document DKIM implementation in security procedures, maintain key management records, and collect authentication success metrics for compliance evidence.
DMARC (Domain-based Message Authentication) Policy
DMARC builds on SPF and DKIM to provide comprehensive email authentication policy enforcement.
Policy Progression Strategy:
v=DMARC1; p=none; rua=mailto:[email protected]
v=DMARC1; p=quarantine; pct=25; rua=mailto:[email protected]
v=DMARC1; p=reject; rua=mailto:[email protected]Implementation Phases:
- Monitor (p=none): Collect authentication data without enforcement
- Quarantine (p=quarantine): Partial enforcement with gradual percentage increase
- Reject (p=reject): Full policy enforcement for maximum protection
III. Monitoring and Reporting Framework
DMARC Aggregate Reports Analysis
DMARC aggregate reports provide comprehensive visibility into email authentication performance, supporting ISO 27001 monitoring requirements.
Report Analysis Components:
- Authentication success/failure rates
- Source IP reputation assessment
- Policy enforcement effectiveness
- Threat intelligence correlation
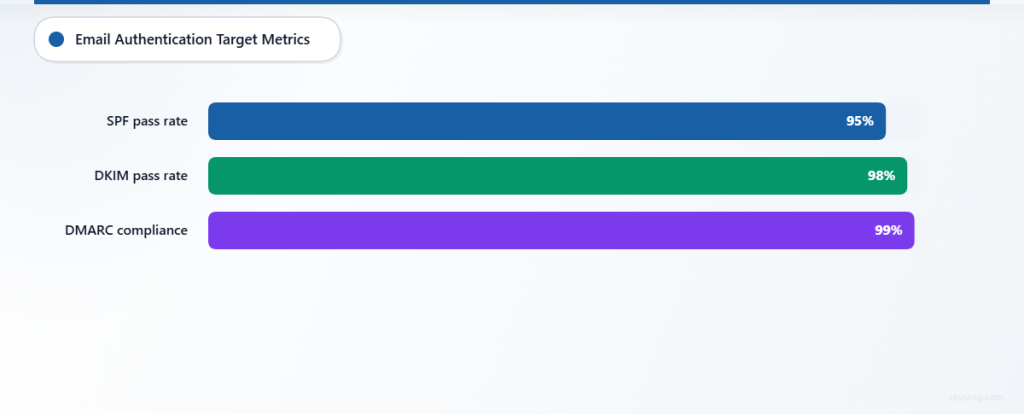
Key Performance Indicators:
- SPF authentication pass rate (target: >95%)
- DKIM authentication pass rate (target: >98%)
- DMARC policy compliance rate (target: >99%)
- Unauthorized sending source detection
Forensic Report Processing
DMARC forensic reports provide detailed information about authentication failures, supporting incident detection and response capabilities.
Forensic Data Elements:
- Original message headers and content
- Authentication failure reasons
- Source network information
- Recipient handling decisions
Integration Requirements:
- Forward forensic reports to SIEM systems
- Correlate with threat intelligence feeds
- Trigger automated incident response workflows
- Generate compliance audit trails
IV. Risk Assessment and Management
Email Threat Landscape Assessment
Organizations must conduct regular risk assessments to identify email-related threats and determine appropriate control measures.
Common Email Attack Vectors:
- Domain spoofing and impersonation attacks
- Business email compromise (BEC) schemes
- Malware distribution through email attachments
- Data exfiltration via unauthorized email channels
Risk Evaluation Criteria:
- Likelihood of successful attack execution
- Potential business impact and financial loss
- Regulatory compliance implications
- Reputation damage consequences
Control Effectiveness Measurement
ISO 27001 requires organizations to measure and evaluate the effectiveness of implemented security controls.
Email Control Metrics:
- Authentication protocol deployment coverage
- Policy enforcement success rates
- Incident detection and response times
- User security awareness training effectiveness
Measurement Methodology:
- Define baseline security metrics
- Implement continuous monitoring systems
- Collect and analyze performance data
- Report findings to senior management
- Implement corrective actions for gaps
V. Implementation Best Practices
Technical Configuration Standards
DNS Management:
- Implement DNS Security Extensions (DNSSEC) for record integrity
- Use short TTL values during initial deployment phases
- Maintain separate DNS zones for email authentication records
- Document all DNS changes through change control processes
Email Server Configuration:
- Configure mail servers to perform authentication checks
- Implement proper message handling for authentication failures
- Enable detailed logging for audit trail requirements
- Establish secure communication channels for authentication reporting
Organizational Controls
Policy Development:
- Create comprehensive email security policies
- Define roles and responsibilities for email system management
- Establish incident response procedures for authentication failures
- Document training requirements for administrative personnel
Change Management:
- Implement formal change control for email authentication configurations
- Require security review for all email infrastructure changes
- Maintain configuration baseline documentation
- Establish rollback procedures for failed implementations
VI. Audit Preparation and Evidence Collection
Documentation Requirements
ISO 27001 auditors expect comprehensive documentation demonstrating control implementation and effectiveness.
Required Documentation:
- Email security policy and procedures
- Risk assessment reports including email threats
- Technical implementation specifications
- Monitoring and measurement reports
- Incident response records
- Training and awareness materials
Evidence Collection Strategy
Technical Evidence:
- Email authentication configuration files
- DNS record validation reports
- DMARC aggregate and forensic report summaries
- Security monitoring dashboard screenshots
- Vulnerability assessment results
Procedural Evidence:
- Change control approval records
- Incident response activity logs
- Management review meeting minutes
- Security awareness training completion records
- Supplier security assessment reports
VII. Integration with Skysnag Comply
Skysnag Comply streamlines ISO 27001 email control implementation through automated configuration management and compliance reporting capabilities. The platform provides:
Automated Control Implementation:
- Guided SPF, DKIM, and DMARC configuration
- Real-time DNS validation and monitoring
- Policy recommendation engine based on risk assessment
- Automated evidence collection for audit purposes
Compliance Reporting:
- ISO 27001-aligned control effectiveness reports
- Automated incident detection and alerting
- Risk dashboard with key performance indicators
- Audit-ready documentation generation
Continuous Monitoring:
- Real-time authentication performance monitoring
- Threat intelligence integration and alerting
- Policy compliance tracking and reporting
- Automated escalation for critical security events
VIII. Advanced Implementation Considerations
Multi-Domain Management
Organizations with complex domain portfolios require sophisticated authentication management strategies.
Configuration Challenges:
- Subdomain authentication policy inheritance
- Third-party service provider authorization
- Brand protection across multiple domains
- Consistent policy enforcement across organizational units
Solution Framework:
- Implement hierarchical authentication policies
- Use DMARC subdomain policy tags (sp=) for granular control
- Maintain centralized authentication monitoring
- Establish cross-domain threat intelligence sharing
Cloud Service Integration
Modern organizations leverage multiple cloud services for email processing, requiring careful authentication configuration.
Integration Requirements:
- Authorize cloud service provider IP addresses in SPF records
- Configure DKIM signing for cloud-based email services
- Implement DMARC policies that account for cloud service authentication
- Monitor authentication performance across all service providers
IX. Key Takeaways
Email authentication controls provide essential support for ISO 27001 certification by addressing access control, cryptography, and operations security requirements. While the standard does not mandate specific protocols, implementing SPF, DKIM, and DMARC creates a robust foundation for email security management.
Successful implementation requires comprehensive risk assessment, technical configuration management, continuous monitoring, and thorough documentation. Organizations should focus on gradual policy enforcement, comprehensive monitoring, and integration with broader security management systems.
Regular measurement and evaluation of email control effectiveness ensures ongoing compliance with ISO 27001 requirements and provides evidence of due diligence in protecting organizational information assets.
For organizations seeking streamlined ISO 27001 email control implementation, Skysnag Comply provides comprehensive automation and reporting capabilities that reduce implementation complexity while ensuring audit readiness.