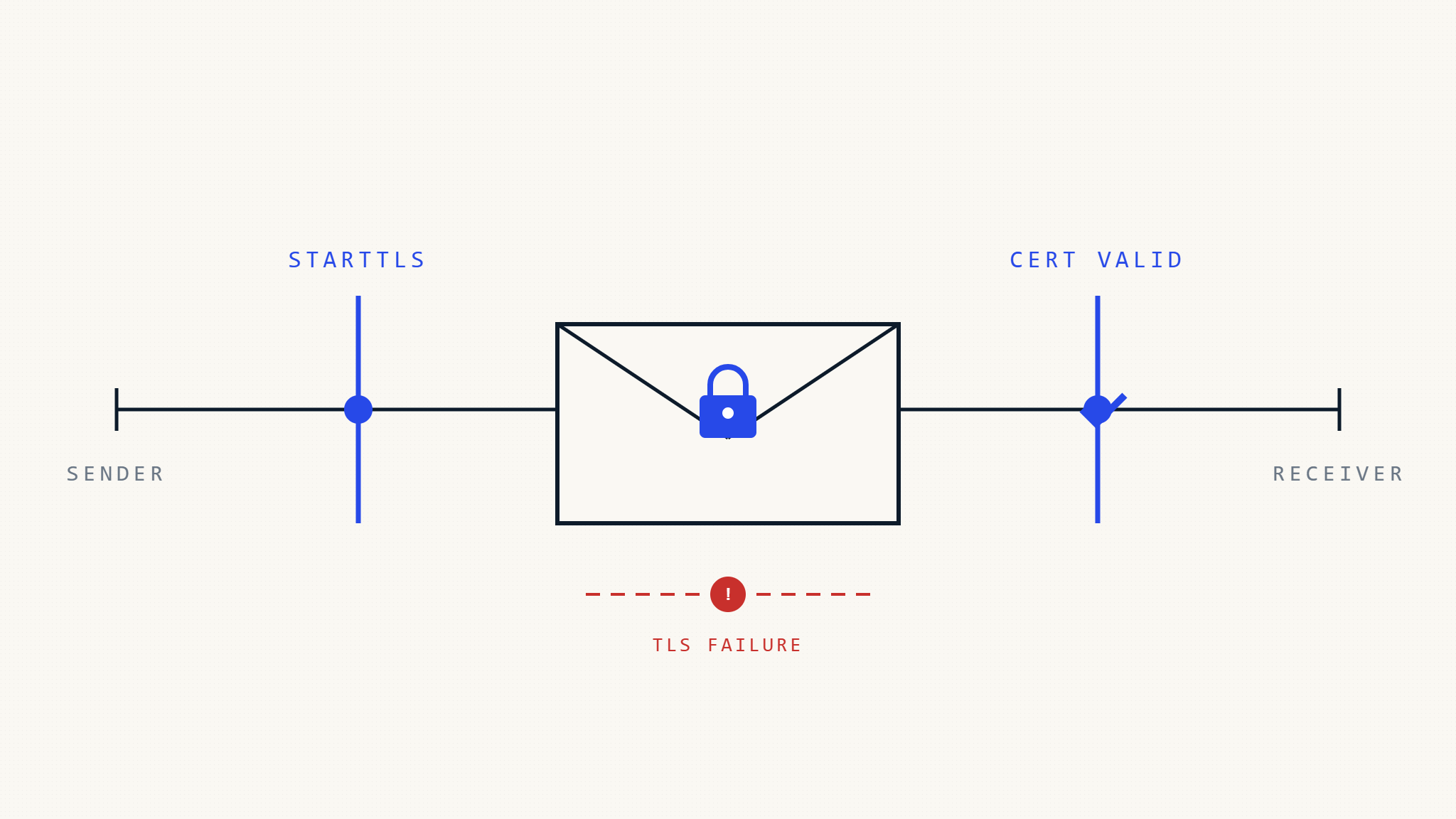
Email encryption failures represent a critical blind spot in organizational security, with TLS-RPT analysis revealing systematic breakdowns in SMTP TLS implementation that leave sensitive communications vulnerable to interception. Transport Layer Security Reporting (TLS-RPT) provides unprecedented visibility into email encryption failures, exposing patterns that help security teams understand why their encrypted email initiatives aren’t working as intended.
I. What Is TLS-RPT Analysis and Why Does It Matter?

TLS-RPT analysis involves examining Transport Layer Security reports generated when email servers attempt to establish encrypted connections during message transmission. These reports capture detailed information about TLS handshake failures, certificate validation errors, and policy enforcement issues that prevent successful email encryption.
Unlike traditional email security monitoring that focuses on delivered messages, TLS-RPT analysis reveals the hidden failures occurring during the encryption negotiation process. When an email server cannot establish a secure TLS connection with the receiving server, the message may downgrade to unencrypted transmission or fail entirely, creating security gaps that organizations rarely detect through conventional monitoring.
The significance extends beyond individual message failures. TLS-RPT data reveals systematic issues in email infrastructure configuration, certificate management practices, and encryption policy enforcement that compound over time. Organizations implementing SMTP TLS often discover through TLS-RPT analysis that their encryption coverage is far lower than expected, with failure rates sometimes exceeding 15% of outbound messages according to email infrastructure studies.
II. Common Email Encryption Failure Patterns in TLS-RPT Data
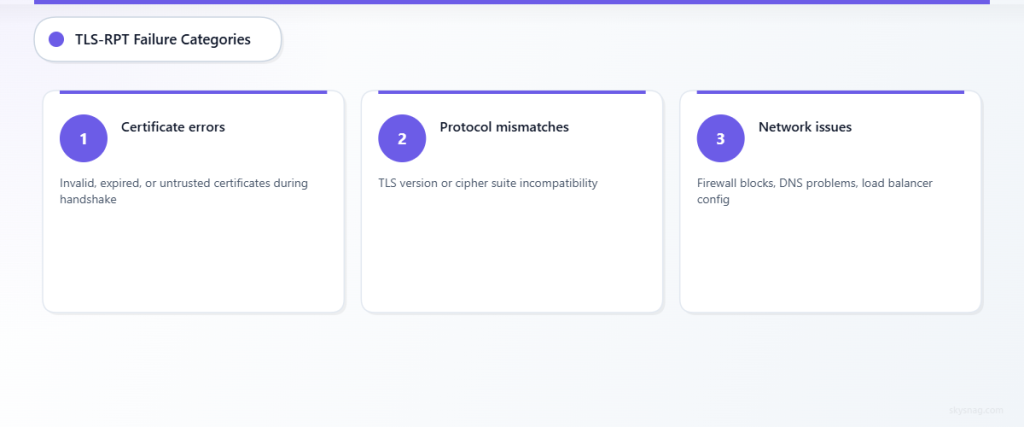
Certificate Validation Failures
Certificate-related errors represent the most frequent cause of email encryption failures in TLS-RPT analysis. These failures occur when receiving mail servers present invalid, expired, or untrusted certificates during the TLS handshake process.
Self-signed certificates cause immediate validation failures, particularly problematic for organizations operating internal mail servers or using cloud providers with non-standard certificate configurations. Certificate chain validation errors emerge when intermediate certificates are missing or incorrectly configured, preventing the receiving server from establishing trust with the certificate authority.
Certificate hostname mismatches create another common failure pattern, occurring when the certificate’s subject alternative name (SAN) doesn’t match the mail server’s actual hostname. This frequently happens during server migrations or when organizations use generic cloud hosting without proper certificate customization.
Protocol Version and Cipher Suite Mismatches
TLS-RPT analysis frequently reveals protocol negotiation failures between mail servers supporting different TLS versions or cipher suites. Legacy mail servers may only support older TLS versions (1.0 or 1.1) while modern security policies require TLS 1.2 or higher, creating incompatibility that forces message downgrade or delivery failure.
Cipher suite mismatches occur when sending and receiving servers cannot agree on acceptable encryption algorithms. Organizations implementing strict security policies may disable weak cipher suites, but this can prevent communication with external partners still using legacy configurations.
Forward secrecy requirements add another layer of complexity, with some organizations requiring perfect forward secrecy (PFS) cipher suites that older mail servers cannot support. The result is a communication breakdown that TLS-RPT analysis makes visible but traditional monitoring misses.
Network Infrastructure and Connectivity Issues
Network-level problems create encryption failures that appear in TLS-RPT data as connection timeouts, refused connections, or incomplete handshakes. Firewall configurations blocking specific TLS ports or implementing deep packet inspection can interfere with encryption negotiation.
Load balancers and proxy configurations introduce additional failure points, particularly when SSL/TLS termination occurs at the wrong network layer or when session persistence isn’t properly configured for mail servers. These infrastructure issues create intermittent failures that are difficult to diagnose without comprehensive TLS-RPT analysis.
DNS resolution problems affecting mail server discovery can prevent TLS connections from establishing, particularly when MX records point to servers with connectivity issues or when DNS over HTTPS (DoH) implementations conflict with mail server resolution.
III. Systematic Approaches to Email Encryption Troubleshooting
Implementing Comprehensive TLS-RPT Collection
Effective SMTP TLS troubleshooting begins with systematic TLS-RPT report collection across all organizational domains and subdomains. Organizations should configure TLS-RPT policies that request daily reports from all external mail servers, providing complete visibility into encryption failures.
Report aggregation becomes critical when managing multiple domains or complex mail routing configurations. Centralized collection systems should normalize TLS-RPT data from different sources, enabling pattern recognition across the entire email infrastructure.
Automated parsing and categorization of TLS-RPT failures enables faster identification of systemic issues versus one-off problems. Organizations implementing comprehensive analysis often discover that apparent random failures actually follow predictable patterns tied to specific mail providers, geographic regions, or time periods.
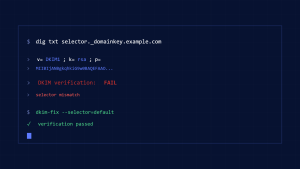
Certificate Management and Validation Strategies
Proactive certificate management addresses the most common source of email encryption failures identified in TLS-RPT analysis. Organizations should implement automated certificate monitoring that tracks expiration dates across all mail servers and validates certificate chains before deployment.
Certificate transparency logs provide additional validation layers, enabling organizations to detect unauthorized certificates issued for their mail domains. Integration with TLS-RPT analysis helps correlate certificate-related failures with actual mail delivery problems.
Backup certificate strategies become essential for maintaining email encryption during certificate transitions. Organizations should maintain valid backup certificates and implement automated failover procedures that minimize encryption disruption during certificate updates.
Infrastructure Configuration Optimization
Mail server configuration optimization based on TLS-RPT analysis involves adjusting TLS policies to balance security requirements with communication reliability. Organizations should maintain compatibility matrices showing supported TLS versions and cipher suites across their major communication partners.
Gradual policy enforcement helps organizations implement stronger encryption requirements without causing widespread delivery failures. TLS-RPT analysis enables monitoring of failure rates during policy transitions, allowing for adjustments before full enforcement.
Network infrastructure tuning includes optimizing firewall rules, load balancer configurations, and DNS resolution for reliable TLS connections. Organizations should test encryption connectivity from multiple network paths to identify potential infrastructure bottlenecks.
IV. Strategic Implementation of TLS-RPT Analysis with Skysnag Comply
Skysnag Comply integrates TLS-RPT analysis into comprehensive email security monitoring, providing automated collection, parsing, and analysis of encryption failure data across organizational domains. The platform’s centralized dashboard enables security teams to identify encryption failure patterns and track remediation progress over time.
The solution’s automated alerting capabilities notify administrators when encryption failure rates exceed acceptable thresholds or when new failure patterns emerge. This proactive approach prevents small encryption issues from developing into systematic delivery problems.
Skysnag Comply’s reporting features support compliance documentation requirements, particularly for organizations subject to data protection regulations that mandate encryption for sensitive communications. The platform generates compliance-ready reports showing encryption coverage percentages and remediation activities.
Integration with existing security information and event management (SIEM) systems enables correlation of email encryption failures with broader security events, providing context for incident response activities and helping security teams prioritize remediation efforts.
V. Key Takeaways
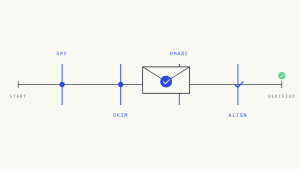
TLS-RPT analysis reveals critical email encryption failures that traditional monitoring approaches miss, providing visibility into certificate validation errors, protocol mismatches, and infrastructure problems that compromise message security. Systematic collection and analysis of TLS-RPT data enables organizations to identify failure patterns and implement targeted remediation strategies.
Certificate management emerges as the most critical factor in maintaining reliable email encryption, requiring proactive monitoring, automated validation, and strategic backup planning. Infrastructure optimization based on TLS-RPT insights helps organizations balance security requirements with communication reliability.
Organizations implementing comprehensive TLS-RPT analysis through solutions like Skysnag Comply gain the visibility and automation necessary to maintain effective email encryption programs while supporting compliance requirements and operational reliability.