DMARC p=none serves as the essential first step in email authentication deployment, providing visibility into your email ecosystem without impacting legitimate mail delivery. This monitor-only policy allows organizations to understand their email authentication landscape before implementing enforcement policies that could potentially block legitimate messages.
Understanding when to use p=none and how to transition safely to enforcement policies is crucial for maintaining email deliverability while building robust anti-phishing defenses. Many organizations rush to enforcement without adequate monitoring, creating delivery issues that could have been avoided with proper p=none implementation.
I. Understanding DMARC p=none Policy

DMARC p=none instructs receiving mail servers to take no action against messages that fail DMARC authentication checks. Instead of quarantining or rejecting failed messages, the policy generates aggregate and forensic reports that provide detailed insights into email authentication patterns.
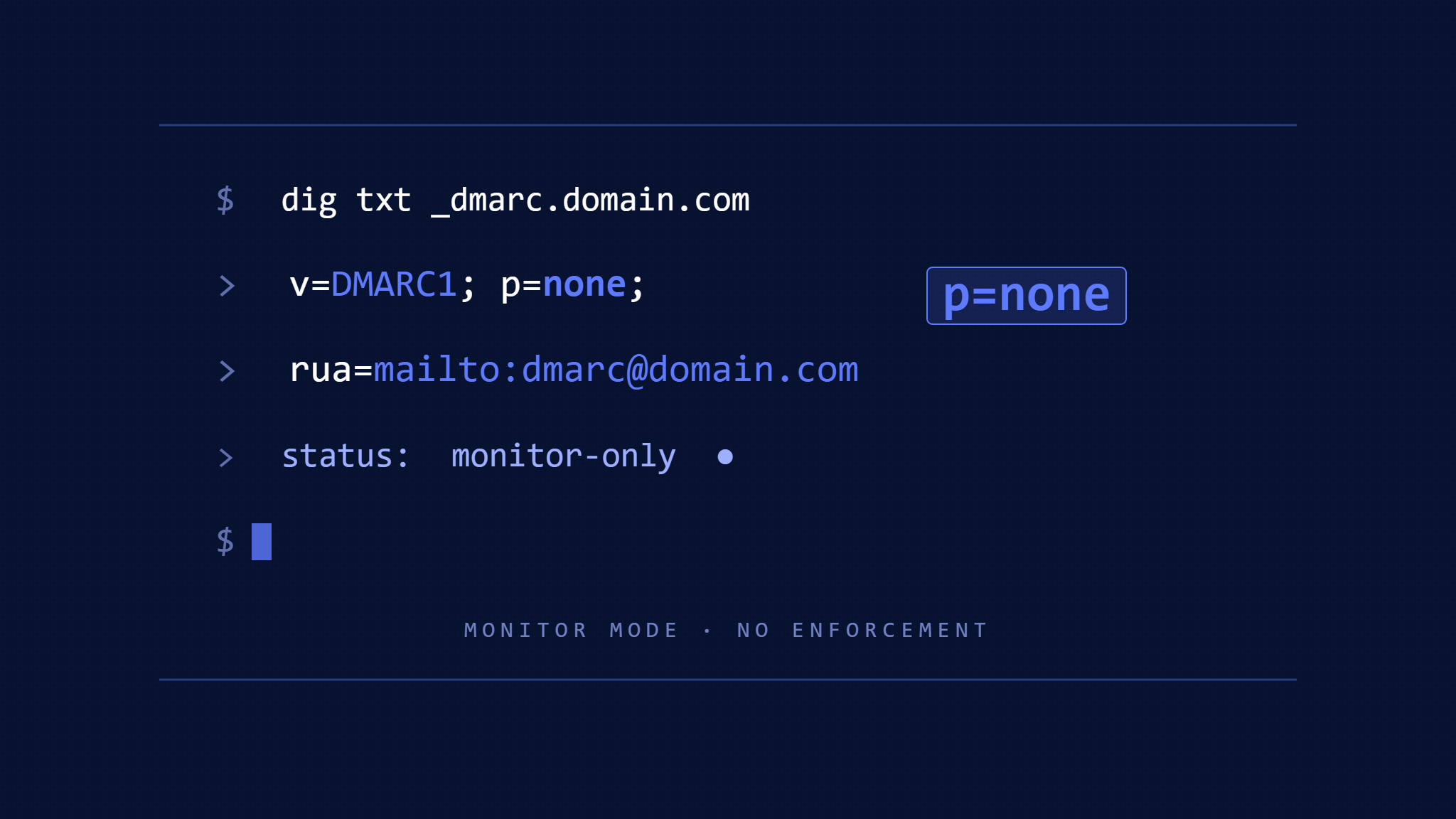
The p=none policy record typically looks like this:
v=DMARC1; p=none; rua=mailto:[email protected]; ruf=mailto:[email protected];This configuration enables comprehensive monitoring while maintaining normal mail flow. Organizations receive detailed reports about all email claiming to originate from their domain, including both legitimate sources and potential threats.
How Monitor-Only Policy Functions
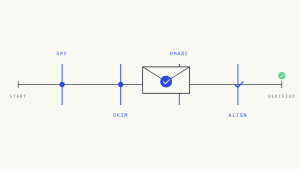
When a receiving server encounters a message from a domain with p=none policy, it performs standard DMARC alignment checks against SPF and DKIM records. Failed authentication triggers report generation but no delivery impact. The message continues through normal processing, reaching the intended recipient regardless of authentication status.
This approach provides complete visibility into email patterns without the risk of blocking legitimate communications. Organizations can identify all authorized sending sources, spot authentication gaps, and detect fraudulent activity without operational disruption.
II. When DMARC p=none Is Appropriate

Initial DMARC Implementation
Every organization should begin DMARC deployment with p=none policy. This monitoring phase reveals the complete email ecosystem, including forgotten third-party services, legacy systems, and partner integrations that may not be properly authenticated.
Organizations commonly discover 20-30% more legitimate sending sources during the monitoring phase than initially documented. These sources might include marketing platforms, customer service systems, automated notifications, and business partner communications that weren’t included in the original inventory.
Complex Email Environments
Organizations with distributed email infrastructure benefit from extended p=none monitoring. Companies using multiple marketing platforms, regional offices with local email systems, or extensive third-party integrations need comprehensive visibility before enforcement.
Manufacturing companies often maintain separate systems for customer communications, supplier notifications, and regulatory reporting. Each system may have different authentication configurations, making thorough monitoring essential before policy enforcement.
Merger and Acquisition Scenarios
During organizational changes, p=none policies provide crucial visibility into inherited email systems. Acquired companies may operate undocumented email services or maintain legacy authentication configurations that could be disrupted by immediate enforcement policies.
The monitoring approach allows IT teams to identify and properly configure all inherited email sources before implementing stricter policies. This prevents service disruptions during critical transition periods.
III. Benefits of Monitor-Only Implementation
Complete Email Visibility
DMARC reports generated during p=none deployment provide comprehensive email source identification. Organizations receive detailed information about every IP address, sending service, and authentication status for messages claiming their domain.
This visibility extends beyond internal systems to include spoofing attempts and fraudulent messages. Security teams can analyze attack patterns, identify targeted campaigns, and understand the threat landscape specific to their domain.
Skysnag Protect transforms complex DMARC aggregate reports into actionable insights, helping organizations quickly identify legitimate sources and potential threats during the monitoring phase.
Risk-Free Authentication Testing
The p=none policy enables comprehensive testing of SPF and DKIM configurations without delivery impact. Organizations can modify authentication records, test new sending services, and validate configuration changes while maintaining normal email operations.
This testing capability proves especially valuable when implementing new email marketing platforms or updating DNS configurations. Teams can verify proper authentication before committing to enforcement policies.
Stakeholder Confidence Building
Extended monitoring periods demonstrate due diligence to business stakeholders concerned about email delivery impacts. Comprehensive reports showing stable authentication patterns and identified improvements build confidence in eventual policy enforcement.
Executive teams appreciate data-driven approaches to security implementations. Detailed monitoring results provide clear justification for moving to enforcement policies while demonstrating thorough risk assessment.
IV. Transitioning from p=none to Enforcement
Monitoring Duration Guidelines
Most organizations should maintain p=none policies for 2-4 weeks minimum to capture typical email patterns. Complex environments may require 6-8 weeks of monitoring to identify quarterly reports, seasonal campaigns, or intermittent business processes.
Organizations with global operations should monitor through complete business cycles to ensure regional systems and time zone variations are properly documented. Holiday seasons and fiscal period closes often reveal additional email sources.
Authentication Source Validation
Before transitioning to enforcement, validate that all legitimate sources achieve proper SPF and DKIM alignment. This requires configuring authentication records for every identified sending service and verifying consistent DMARC pass rates.
Common validation steps include:
- Confirming SPF records include all legitimate IP addresses
- Verifying DKIM signing for all authorized services
- Testing authentication alignment for third-party platforms
- Validating backup and disaster recovery email systems
Gradual Enforcement Implementation
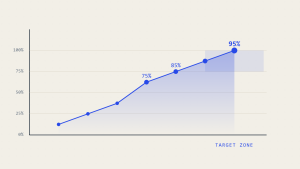
The safest transition approach implements enforcement gradually using percentage-based policies. Starting with p=quarantine at 5% allows organizations to test enforcement impact on a small subset of messages while maintaining most normal delivery.
Progressive implementation might follow this timeline:
- Week 1-2: p=quarantine; pct=5
- Week 3-4: p=quarantine; pct=25
- Week 5-6: p=quarantine; pct=50
- Week 7-8: p=quarantine; pct=100
- Week 9-10: p=reject; pct=25
- Week 11+: p=reject; pct=100
This approach provides multiple checkpoints to identify and resolve authentication issues before full enforcement.
V. Common p=none Implementation Challenges
Report Volume Management
Organizations with high email volumes may receive thousands of DMARC aggregate reports daily. Managing and analyzing this data manually becomes impractical, requiring automated processing and analysis tools.
Without proper tooling, teams often struggle to extract actionable insights from report data. The volume can overwhelm manual analysis, leading to incomplete source identification or delayed enforcement transitions.
False Positive Identification
Distinguishing between legitimate authentication failures and actual threats requires careful analysis. Legitimate services may show intermittent authentication failures due to configuration issues or service provider changes.
Organizations must investigate each unique source to determine whether authentication failures represent configuration problems or security threats. This analysis process requires both technical expertise and business context understanding.
Stakeholder Communication
Different business units may control various email sending services, requiring coordination across multiple teams. Marketing departments, customer service groups, and IT operations may each manage separate systems requiring authentication configuration.
Effective p=none implementation requires clear communication about the monitoring process, timeline expectations, and eventual enforcement implications. Regular stakeholder updates help maintain support throughout the transition process.
VI. Best Practices for Monitor-Only Deployment
Comprehensive Reporting Configuration
Configure both aggregate (RUA) and forensic (RUF) reporting addresses to capture complete authentication data. Aggregate reports provide statistical summaries while forensic reports deliver detailed message samples for investigation.
Use dedicated email addresses for DMARC reporting to avoid mixing authentication data with operational communications. Consider implementing automated processing for high-volume environments to ensure timely analysis.
Regular Report Analysis
Establish weekly report review processes to identify new sources and track authentication trends. Consistent analysis helps detect configuration changes, new threats, or service modifications that might impact enforcement readiness.
Document all identified sources with business justification and technical contact information. This documentation supports later enforcement decisions and helps maintain authentication configurations over time.
Cross-Team Collaboration
Involve security, IT operations, marketing, and business stakeholders in the monitoring process. Different teams may recognize legitimate sources or provide context for authentication patterns that aren’t immediately obvious.
Regular cross-functional meetings during the monitoring phase help ensure comprehensive source identification and build consensus for eventual enforcement implementation.
VII. Tools and Technologies for p=none Management
Modern DMARC analysis platforms transform raw report data into actionable intelligence. These tools aggregate data from multiple sources, identify trends, and provide clear visualizations of authentication status across the email ecosystem.
Skysnag Protect offers comprehensive DMARC monitoring capabilities that simplify p=none deployment and analysis. The platform provides automated report processing, threat identification, and clear transition guidance for moving to enforcement policies.
Advanced platforms also provide integration capabilities with existing security tools, enabling automated threat detection and response workflows based on DMARC intelligence.
VIII. Key Takeaways
DMARC p=none policies serve as essential monitoring tools that provide comprehensive email ecosystem visibility without delivery impact. Organizations should implement p=none as the first step in any DMARC deployment, maintaining monitoring for sufficient duration to identify all legitimate sending sources.
Successful transitions to enforcement require careful analysis of monitoring data, validation of authentication configurations, and gradual implementation of percentage-based policies. The monitoring phase builds stakeholder confidence while ensuring comprehensive source identification.
Effective p=none deployment requires appropriate tooling for report analysis, cross-team collaboration for source identification, and systematic processes for transitioning to enforcement. Organizations that invest in proper monitoring phases achieve more successful DMARC implementations with fewer delivery disruptions.
Ready to implement comprehensive DMARC monitoring? Skysnag Protect provides the visibility and analysis tools needed for successful p=none deployment and safe transition to enforcement policies.