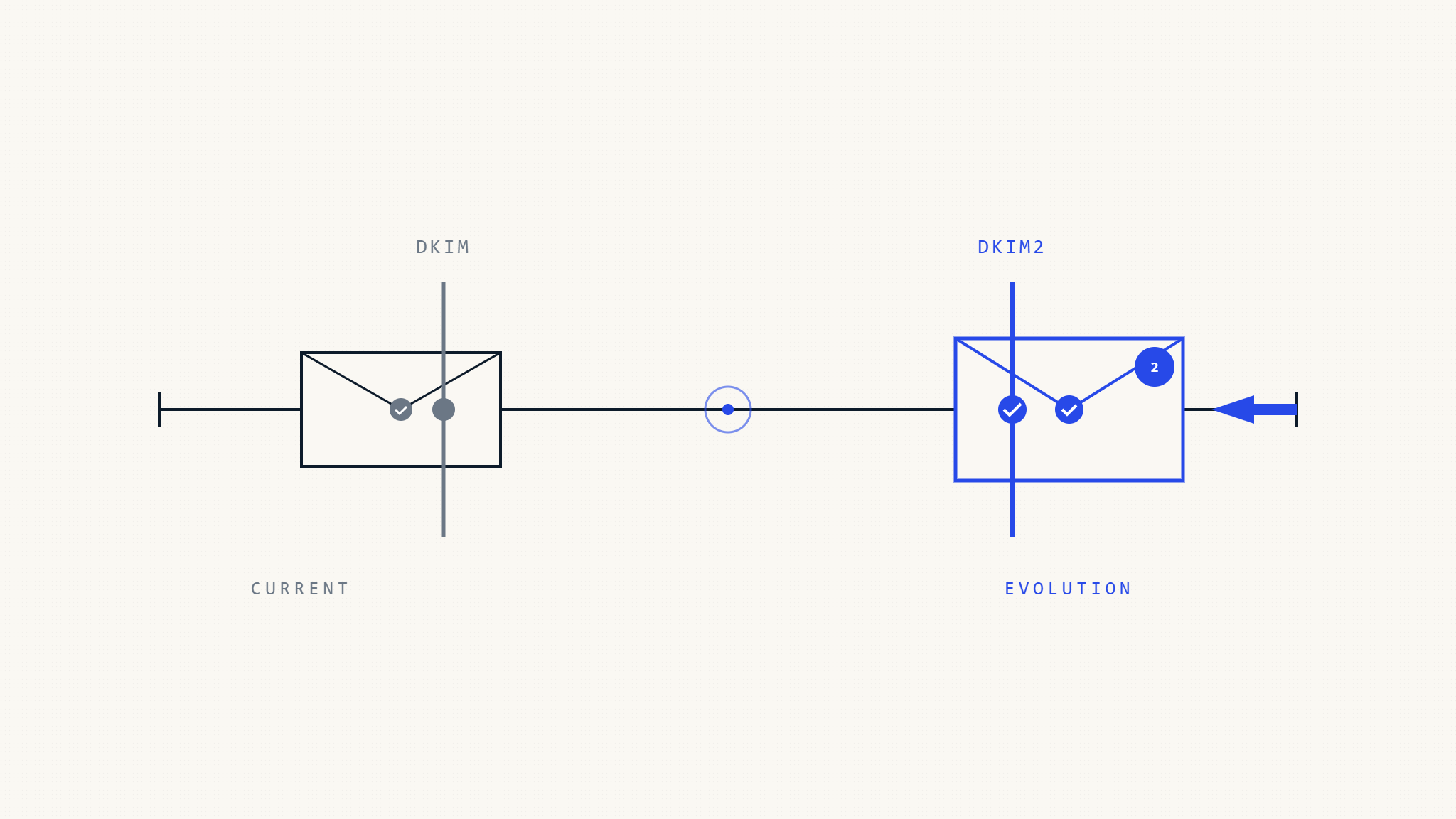
Email authentication continues to evolve as cybercriminals develop more sophisticated attacks. While DKIM (DomainKeys Identified Mail) has served as a cornerstone of email security for nearly two decades, organizations must optimize their current implementations while preparing for emerging authentication standards. Understanding DKIM best practices, common challenges, and integration with modern standards like ARC and BIMI is crucial for organizations planning their long-term email security strategy.
I. What Is DKIM and Why It Matters
DKIM provides cryptographic authentication by allowing email senders to digitally sign their messages. When an email is sent, DKIM creates a digital signature using a private key, which receiving servers can verify using a public key published in DNS records. This process confirms that the message originated from an authorized sender and hasn’t been tampered with during transmission.
Current DKIM implementations face several challenges that modern optimization strategies aim to address:
- Key management complexity requiring manual rotation and coordination
- Limited cryptographic agility with slower adoption of modern algorithms
- Scalability concerns for high-volume email operations
- Integration gaps with newer authentication frameworks
II. Modern DKIM Optimization Strategies
Rather than waiting for future standards, organizations can significantly improve their email security by optimizing current DKIM implementations and integrating with emerging authentication technologies.
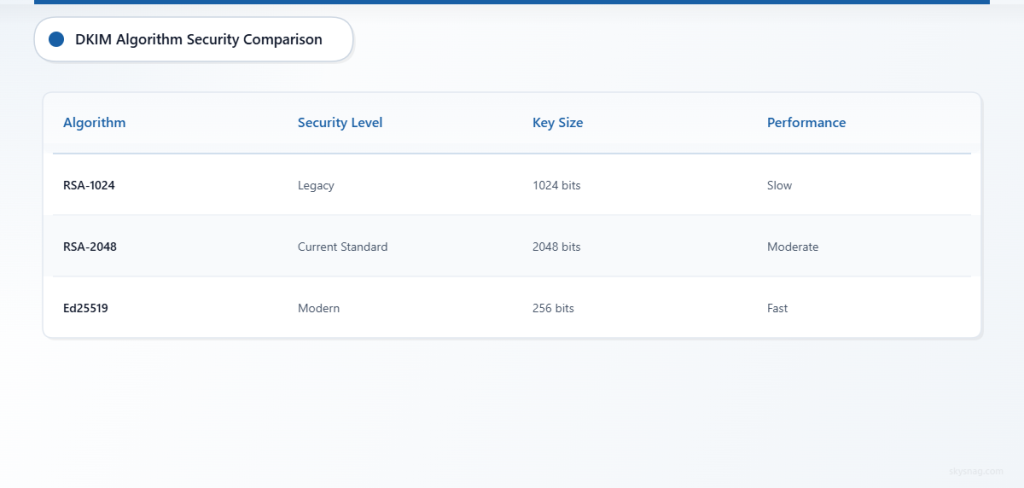
Enhanced Cryptographic Security
Modern DKIM implementations should prioritize stronger cryptographic algorithms. While RSA-1024 was once standard, organizations should migrate to RSA-2048 or Ed25519 for improved security. Ed25519 offers equivalent security to RSA-2048 with smaller key sizes and faster signature generation.
Algorithm Comparison:
- RSA-1024: Legacy, should be deprecated
- RSA-2048: Current standard, widely supported
- Ed25519: Modern elliptic curve, optimal performance
Simplified Key Management Best Practices
Effective key management reduces operational burden while improving security through regular rotation:
Automated Key Rotation
Implement quarterly or bi-annual key rotation schedules using automated tools. This reduces the risk of key compromise and ensures consistent security posture.
Hierarchical Key Structures
Use consistent selector naming conventions that indicate key generation dates or purposes (e.g., selector-202401, marketing-key, transactional-key).
Better Scalability Techniques
High-volume email senders can optimize DKIM performance through several strategies:
Selective Header Signing
Sign only essential headers to reduce signature size and processing overhead while maintaining security effectiveness.
Parallel Processing
Implement multi-threaded signature generation for bulk email operations to improve throughput.
Caching Strategies
Cache DNS lookups for public key retrieval to reduce latency during signature verification.
III. Integration with Modern Authentication Standards
Authenticated Received Chain (ARC)
ARC preserves email authentication results when messages pass through intermediaries like mailing lists or forwarding services. ARC works alongside DKIM to maintain authentication integrity throughout the email delivery chain.
ARC Implementation Benefits:
- Preserves DKIM authentication through email forwarding
- Reduces false positives in DMARC policies
- Improves deliverability for legitimate forwarded messages
ARC Headers Structure:
ARC-Authentication-Results: i=1; domain.com; dkim=pass
ARC-Message-Signature: i=1; a=rsa-sha256; d=intermediary.com
ARC-Seal: i=1; a=rsa-sha256; d=intermediary.comBrand Indicators for Message Identification (BIMI)
BIMI allows organizations to display their logos in email clients when they have strong authentication policies. BIMI requires DMARC enforcement policies and works best with properly configured DKIM.
BIMI Requirements:
- DMARC policy set to quarantine or reject
- Strong DKIM implementation with consistent passing rates
- SVG logo file hosted on secure servers
- Verified Mark Certificate (VMC) for enhanced trust
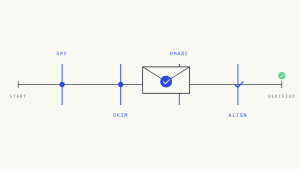
SPF and DKIM Alignment
Proper alignment between SPF, DKIM, and DMARC creates a robust authentication framework:
DKIM Alignment Best Practices:
- Ensure DKIM signing domain aligns with From header domain
- Use organizational domain alignment when managing multiple subdomains
- Monitor alignment rates to identify configuration issues
IV. Common DKIM Implementation Challenges
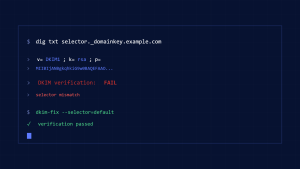
DNS Configuration Issues
Record Publication Problems:
- Incorrect TXT record formatting
- Missing or malformed public keys
- DNS propagation delays
Resolution Strategies:
- Use DNS validation tools to verify record syntax
- Implement monitoring for DNS record availability
- Plan for DNS propagation time during key updates
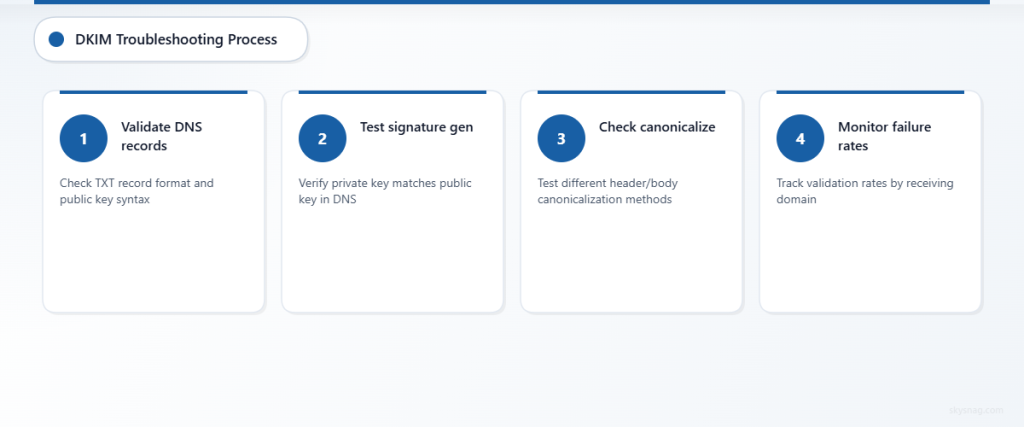
Signature Validation Failures
Common Failure Causes:
- Header modification during email transit
- Incorrect canonicalization settings
- Clock synchronization issues
Troubleshooting Approach:
- Monitor signature validation rates by receiving domain
- Analyze failure patterns to identify systematic issues
- Test signature generation with different canonicalization methods
Performance and Resource Usage
Organizations processing high email volumes must balance security with performance:
Optimization Techniques:
- Implement signature caching for repetitive content
- Use hardware security modules (HSMs) for key storage
- Monitor CPU and memory usage during peak periods
V. Implementation Roadmap for Modern Email Authentication
Phase 1: DKIM Foundation (Months 1-2)
Current Implementation Assessment:
- Audit existing DKIM configuration across all sending domains
- Evaluate key strength and rotation schedules
- Review signature validation rates and failure patterns
- Document current DNS record structure and management processes
Optimization Actions:
- [ ] Upgrade to RSA-2048 or Ed25519 keys
- [ ] Implement automated key rotation procedures
- [ ] Standardize selector naming conventions
- [ ] Optimize header selection for signatures
Phase 2: Advanced Integration (Months 3-4)
ARC Implementation:
- Deploy ARC signing on outbound mail servers
- Configure ARC validation for inbound processing
- Monitor ARC chain integrity and validation rates
DMARC Optimization:
- Analyze DKIM alignment rates
- Adjust policies based on authentication performance
- Implement gradual enforcement progression
Phase 3: Brand Protection (Months 5-6)
BIMI Deployment:
- Create compliant SVG logo assets
- Publish BIMI DNS records
- Consider Verified Mark Certificate acquisition
- Monitor logo display rates across email clients
Comprehensive Monitoring:
- Deploy unified authentication monitoring tools
- Establish alerting for authentication failures
- Create regular reporting processes
VI. Technical Requirements and Infrastructure
Mail Transfer Agent Updates
Modern email infrastructure requires MTAs that support current authentication standards:
Required Capabilities:
- Multi-algorithm DKIM signing (RSA-2048, Ed25519)
- ARC signing and validation
- Comprehensive logging and monitoring
- API integration for automated management
DNS Infrastructure Considerations
Robust DNS infrastructure supports reliable authentication:
Best Practices:
- Use multiple authoritative DNS servers
- Implement DNS monitoring and alerting
- Plan for emergency key rollover procedures
- Maintain backup DNS records
Monitoring and Analytics Tools
Comprehensive monitoring enables proactive authentication management:
Key Metrics to Track:
- DKIM signature validation rates by domain
- ARC chain integrity statistics
- DMARC alignment percentages
- Authentication failure patterns
VII. Cost-Benefit Analysis
Investment Requirements
Initial Implementation Costs:
- Software licensing for advanced MTA features
- DNS infrastructure upgrades
- Monitoring and management tools
- Staff training and certification
Ongoing Operational Costs:
- Automated key management services
- Enhanced monitoring tool subscriptions
- Additional DNS hosting for multiple records
- Regular security audits and updates
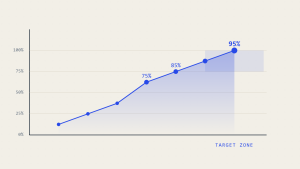
Return on Investment
Security Benefits:
- Reduced email fraud and phishing attempts
- Improved brand protection and reputation
- Enhanced deliverability rates
- Regulatory compliance support
Operational Efficiency:
- Automated authentication management
- Reduced manual troubleshooting time
- Improved incident response capabilities
- Better visibility into email security posture
VIII. Industry Adoption and Best Practices
Current Market Trends
Major email service providers increasingly require strong authentication:
Gmail and Yahoo Requirements:
- DKIM signing for bulk senders
- SPF record publication
- DMARC policy implementation
- Low spam complaint rates
Microsoft 365 Enhancements:
- ARC support for improved forwarding
- Enhanced DKIM validation
- BIMI logo display capabilities
Vendor Ecosystem Support
Email Infrastructure Providers:
Most major email platforms now support modern authentication standards with varying levels of automation and management capabilities.
Security Service Providers:
Specialized email security vendors offer comprehensive authentication management, monitoring, and optimization services.
IX. Future-Proofing Email Authentication
Emerging Standards and Technologies
Post-Quantum Cryptography:
Prepare for eventual migration to quantum-resistant algorithms by implementing crypto-agile infrastructure that can adapt to new standards.
Machine Learning Integration:
Advanced email security platforms increasingly use ML to optimize authentication policies and detect sophisticated threats.
API-Driven Management:
Modern email infrastructure supports programmatic configuration and monitoring, enabling more dynamic and responsive security policies.
Strategic Planning Recommendations
Technology Investment:
- Prioritize platforms with comprehensive authentication support
- Plan for regular infrastructure updates and migrations
- Invest in staff training on emerging standards
Policy Development:
- Create flexible authentication policies that can evolve with new standards
- Establish clear procedures for rapid response to security threats
- Document decision-making processes for future reference
X. Integration with Comprehensive Email Security
Modern email authentication works best as part of a complete security strategy. Skysnag Protect helps organizations implement and monitor DKIM alongside SPF, DMARC, ARC, and BIMI, providing unified visibility into email authentication performance.
The platform’s automated monitoring capabilities enable organizations to:
- Track authentication success rates across all standards
- Receive real-time alerts for policy violations
- Generate comprehensive compliance reports
- Optimize configurations based on performance data
Compliance Considerations
Organizations subject to regulatory requirements should consider how modern email authentication supports their compliance objectives:
Regulatory Benefits:
- Demonstrates security due diligence
- Provides audit trails for email communications
- Supports data protection and privacy requirements
- Enables rapid incident response and forensic analysis
XI. Key Takeaways
Modern email authentication requires a comprehensive approach that optimizes current DKIM implementations while integrating emerging standards like ARC and BIMI. Organizations should focus on:
Immediate Priorities:
- Upgrade cryptographic algorithms to current standards
- Implement automated key management procedures
- Deploy comprehensive authentication monitoring
- Plan for integration with modern standards
Strategic Objectives:
- Build crypto-agile infrastructure for future standards
- Establish strong vendor relationships for ongoing support
- Invest in team capabilities for emerging technologies
- Create flexible policies that adapt to changing threat landscape
Success in email authentication requires treating it as an evolving capability rather than a static implementation. Organizations that invest in modern, well-integrated authentication strategies will be better positioned to protect their brands and maintain email deliverability as standards continue to evolve.
Ready to optimize your email authentication strategy with modern standards and best practices? Skysnag Protect provides the comprehensive monitoring and management tools you need for current and emerging email security requirements.