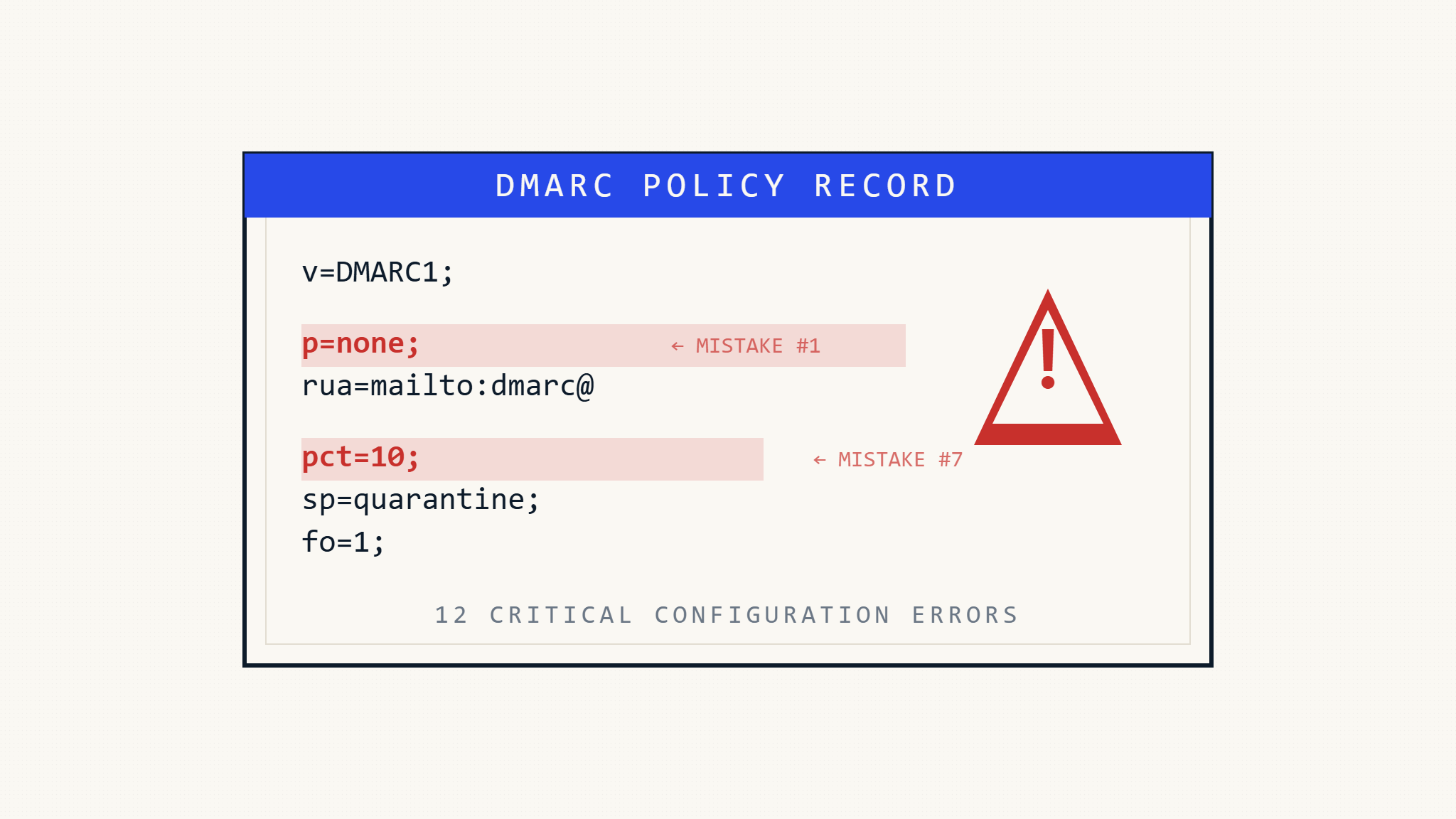
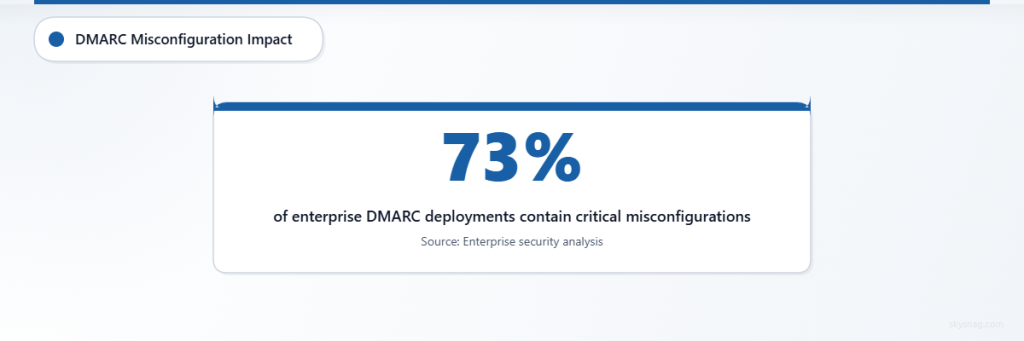
DMARC implementation errors can transform your strongest email security defense into a false sense of protection, leaving your organization vulnerable to sophisticated phishing attacks and brand impersonation. Even minor configuration mistakes can render your entire email authentication strategy ineffective.
Recent analysis of DMARC deployments across enterprise organizations reveals that 73% contain at least one critical misconfiguration that compromises security effectiveness. These implementation errors not only fail to protect against email fraud but can also disrupt legitimate email delivery, creating operational challenges that force organizations to weaken their security posture.
I. Assessment: Common DMARC Implementation Failures
Understanding where DMARC implementations typically fail helps organizations avoid costly security gaps and delivery issues.
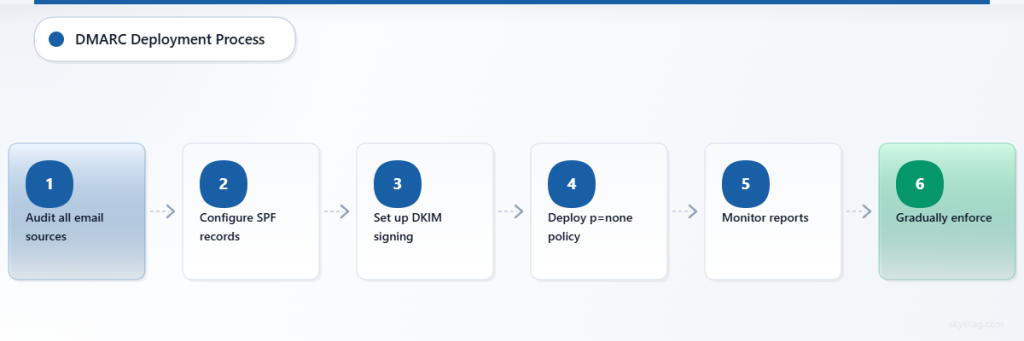
1. Starting with p=reject Without Gradual Deployment
The Mistake: Immediately setting your DMARC policy to p=reject without proper preparation and monitoring.
Why It Breaks Security: Legitimate emails get blocked before you understand your email ecosystem, forcing emergency policy rollbacks that leave you unprotected.
Impact Assessment:
- Measure current authentication pass rates across all email sources
- Document all legitimate sending sources (marketing platforms, third-party services, internal applications)
- Calculate potential business disruption from blocked emails
2. Insufficient SPF Record Coverage
The Mistake: Incomplete SPF records that don’t account for all legitimate sending sources.
Why It Breaks Security: DMARC relies on SPF alignment; missing sources cause authentication failures and policy violations.
Critical Check:
- Audit all email-sending systems, including forgotten legacy applications
- Include cloud services, CRM platforms, and automated notification systems
- Account for IP address changes in dynamic hosting environments
3. DKIM Signature Inconsistencies
The Mistake: Misaligned DKIM domains or missing signatures from key sending sources.
Why It Breaks Security: DKIM failures prevent proper email authentication, making DMARC enforcement ineffective.
Validation Points:
- Verify DKIM signatures align with your organizational domain
- Ensure all email sources generate valid DKIM signatures
- Test signature validity across different email clients and servers
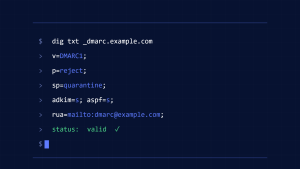
4. Ignoring Subdomain Policy Configuration
The Mistake: Not explicitly setting subdomain policies with sp= tags.
Why It Breaks Security: Subdomains inherit parent domain policies, potentially blocking legitimate subdomain emails or leaving security gaps.
Configuration Review:
- Map all active subdomains used for email sending
- Set appropriate
sp=policies for subdomain protection - Test subdomain email authentication separately from primary domain
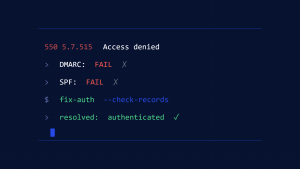
II. Actions: Fixing Critical DMARC Mistakes
5. Inadequate DMARC Reporting Analysis
The Mistake: Deploying DMARC without actively monitoring and analyzing aggregate and forensic reports.
Why It Breaks Security: You remain blind to authentication failures, spoofing attempts, and configuration issues.
Action Steps:
- Implement automated DMARC report processing and analysis
- Set up alert systems for unusual authentication failure patterns
- Create regular review processes for DMARC data trends
6. Missing Alignment Configuration
The Mistake: Not specifying alignment modes with aspf= and adkim= tags when strict alignment is needed.
Why It Breaks Security: Relaxed alignment (default) may allow lookalike domains to pass authentication checks.
Immediate Fixes:
- Evaluate whether strict alignment (
aspf=soradkim=s) suits your email architecture - Test alignment changes in monitoring mode before enforcement
- Document alignment decisions for future reference
7. Incorrect RUA and RUF Recipients
The Mistake: Setting up DMARC reporting addresses that aren’t monitored or don’t exist.
Why It Breaks Security: You lose visibility into DMARC performance and potential security threats.
Setup Requirements:
- Verify reporting email addresses can receive high-volume automated reports
- Configure proper email filtering to prevent report loss
- Ensure reporting addresses are monitored by security teams
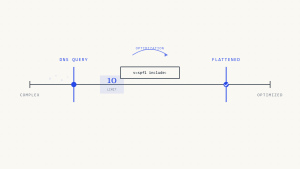
8. Policy Percentage Mismanagement
The Mistake: Using the pct= tag incorrectly or leaving it at partial enforcement indefinitely.
Why It Breaks Security: Partial enforcement creates inconsistent protection, allowing some fraudulent emails through.
Correction Process:
- Start with low percentages during testing phases
- Gradually increase percentages based on authentication success rates
- Remove
pct=tag completely when ready for full enforcement
9. Failure to Coordinate with Third-Party Senders
The Mistake: Not properly configuring authentication for external email service providers.
Why It Breaks Security: Legitimate third-party emails fail DMARC checks, forcing policy relaxation.
Coordination Steps:
- Provide third-party senders with proper DKIM keys and SPF inclusion requirements
- Test third-party authentication before DMARC enforcement
- Maintain updated lists of authorized external senders
III. Automate: DMARC Management and Monitoring
10. No Automated Policy Progression
The Mistake: Manual DMARC policy management without systematic progression planning.
Why It Breaks Security: Human delays and errors prevent timely policy strengthening and threat response.
Automation Framework:
- Schedule automatic policy progression based on authentication success metrics
- Implement automated rollback triggers for authentication failure spikes
- Create systematic testing protocols for policy changes
11. Inadequate Threat Detection Integration
The Mistake: Treating DMARC as a standalone tool without integration into broader security monitoring.
Why It Breaks Security: You miss sophisticated attacks that combine multiple vectors or evolve beyond basic email spoofing.
Integration Requirements:
- Connect DMARC data to SIEM systems for correlation analysis
- Link DMARC failures to brand protection monitoring
- Integrate with threat intelligence feeds for proactive defense
12. Missing Disaster Recovery Planning
The Mistake: No documented procedures for DMARC-related email delivery emergencies.
Why It Breaks Security: Emergency policy changes made without proper planning often create lasting security vulnerabilities.
Recovery Preparation:
- Document emergency contact procedures for DNS changes
- Create tested rollback procedures for policy modifications
- Establish communication protocols for delivery disruptions
Modern DMARC management platforms like Skysnag Protect automate many of these critical processes, providing continuous monitoring, intelligent policy recommendations, and integrated threat detection to prevent common implementation mistakes from compromising your email security posture.
IV. Key Takeaways
DMARC implementation success requires systematic planning, continuous monitoring, and careful attention to configuration details. The most critical mistakes involve rushing deployment without proper preparation, ignoring ongoing management requirements, and failing to integrate DMARC into comprehensive email security strategies.
Effective DMARC protection demands treating implementation as an ongoing security process rather than a one-time configuration task. Organizations that invest in proper planning, automated monitoring, and regular optimization achieve significantly better protection against email-based threats while maintaining reliable email delivery for legitimate communications.
Start your DMARC implementation journey with proper planning and professional guidance at Skysnag Protect to avoid these costly mistakes and achieve robust email security from day one.