Honey trap attacks represent one of the most psychologically manipulative forms of social engineering in cybersecurity, exploiting human emotions and relationships to bypass technical security controls. In the context of email security, honey traps leverage romantic or personal attraction to deceive victims into compromising their organization’s data or systems.
Understanding these sophisticated deception tactics is essential for cybersecurity professionals, as attackers increasingly blend traditional social engineering with relationship-based manipulation to achieve their objectives.
I. What Is a Honey Trap in Cybersecurity?
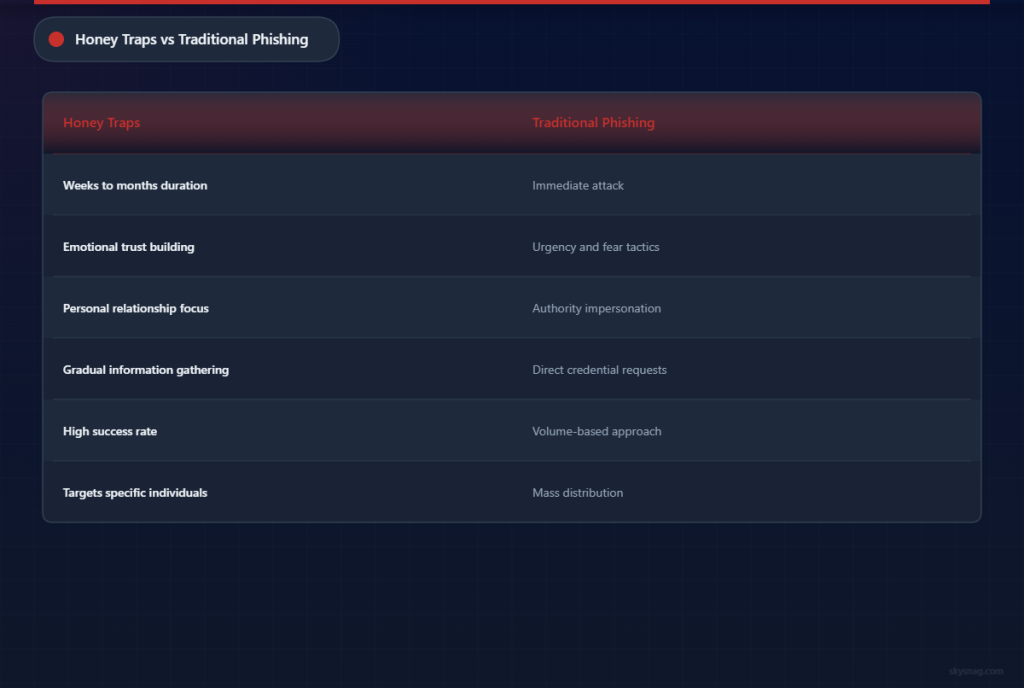
A honey trap in cybersecurity refers to a social engineering attack where cybercriminals create fake romantic or personal relationships to manipulate victims into divulging sensitive information, installing malware, or providing unauthorized access to systems. Unlike traditional phishing that relies on urgency or authority, honey traps exploit emotional connections and trust built over extended periods.
The term originates from espionage, where intelligence operatives would use romantic relationships to extract classified information. In modern cybersecurity, these tactics have evolved into sophisticated email-based campaigns that can persist for weeks or months before the actual attack occurs.
Key Characteristics of Email Honey Traps
Email honey traps typically exhibit several distinct patterns:
Relationship Building Phase: Attackers invest significant time developing what appears to be a genuine personal connection through email exchanges, often using stolen photos and fabricated backstories.
Gradual Trust Escalation: Rather than immediately requesting sensitive information, attackers slowly build credibility and emotional investment before making increasingly bold requests.
Professional Context Integration: Advanced honey traps incorporate workplace-specific knowledge, industry terminology, and company details to appear more credible to corporate targets.
Multi-Channel Coordination: Attackers often extend conversations beyond email to social media, messaging apps, or even phone calls to reinforce the relationship’s authenticity.
II. How Email Honey Traps Work
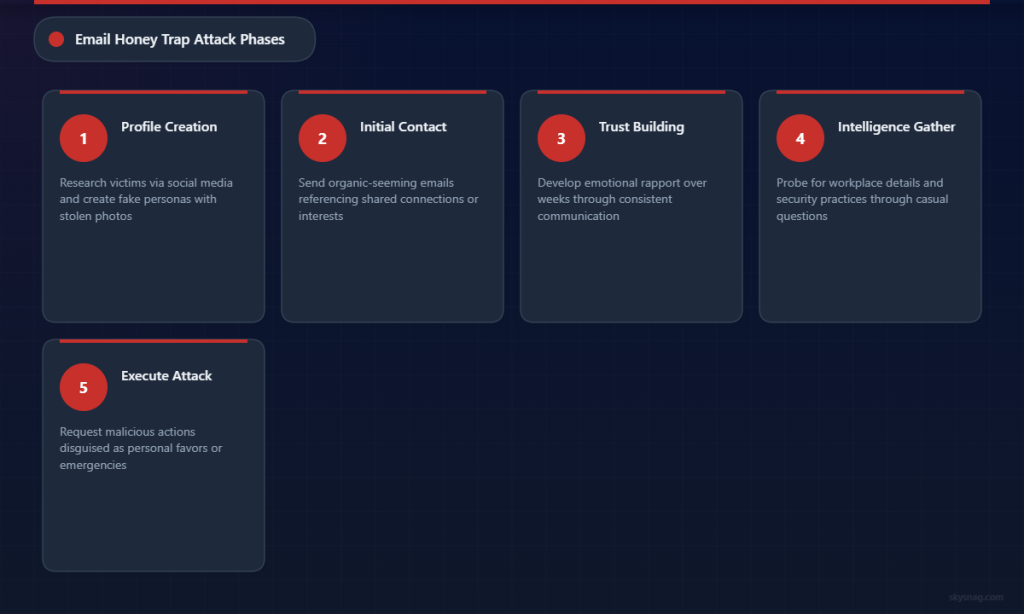
The anatomy of an email honey trap typically unfolds across several carefully orchestrated phases, each designed to deepen the victim’s emotional investment and lower their security awareness.
Initial Contact and Profile Creation
Attackers begin by researching potential victims through social media, professional networks, and public databases to understand their interests, relationship status, and professional responsibilities. They then create compelling fictional personas, often using attractive photos stolen from social media or stock photography sites.
The initial email contact appears organic and may reference shared connections, common interests, or professional associations. Advanced attackers might impersonate colleagues from partner organizations or industry contacts to establish immediate credibility.
Relationship Development
Once initial contact is established, attackers focus on building emotional rapport through regular email exchanges. They demonstrate active listening by remembering personal details shared by the victim and gradually share their own fabricated personal stories to create reciprocal intimacy.
This phase can last weeks or months, with the attacker carefully maintaining consistency in their persona while gathering intelligence about the victim’s work environment, security practices, and access privileges.
Information Gathering
As trust deepens, attackers begin probing for information that could facilitate broader attacks. They might ask seemingly innocent questions about workplace policies, technology systems, or upcoming business activities.
The requests escalate gradually from general industry discussion to more specific operational details, always framed within the context of the established relationship rather than obvious intelligence gathering.
Exploitation Phase
When sufficient trust has been established, attackers execute their primary objective. This might involve requesting the victim to open malicious attachments disguised as personal photos, click links to fake relationship-related websites that install malware, or provide credentials under fabricated emergency scenarios.
Some sophisticated honey traps culminate in requests for the victim to facilitate seemingly legitimate business transactions that actually enable financial fraud or data exfiltration.
III. Common Email Honey Trap Tactics
Cybercriminals employ various specific techniques to enhance the credibility and effectiveness of their honey trap campaigns.
Romance-Based Deception
Attackers create detailed romantic personas, often claiming to be traveling professionals, military personnel deployed overseas, or international business contacts who can only communicate via email. These scenarios explain limited communication channels while building emotional investment.
They leverage psychological principles like intermittent reinforcement, where sporadic but intense emotional exchanges create stronger psychological bonds than consistent communication patterns.
Professional Relationship Exploitation
Some honey traps focus on professional rather than romantic relationships, with attackers posing as industry peers, potential business partners, or colleagues from subsidiary companies. These approaches exploit professional networking instincts rather than romantic attraction.
This variant often proves effective against senior executives who regularly engage with external business contacts and may be more susceptible to professionally framed social engineering.
Crisis and Urgency Manipulation
Advanced honey traps incorporate artificial crisis scenarios where the fictitious persona suddenly requires urgent assistance. These manufactured emergencies leverage the established emotional connection to pressure victims into taking immediate action without following normal security protocols.
Common crisis scenarios include medical emergencies requiring financial assistance, legal troubles requiring document sharing, or business opportunities with tight deadlines requiring credential sharing.
IV. Protecting Against Email Honey Traps
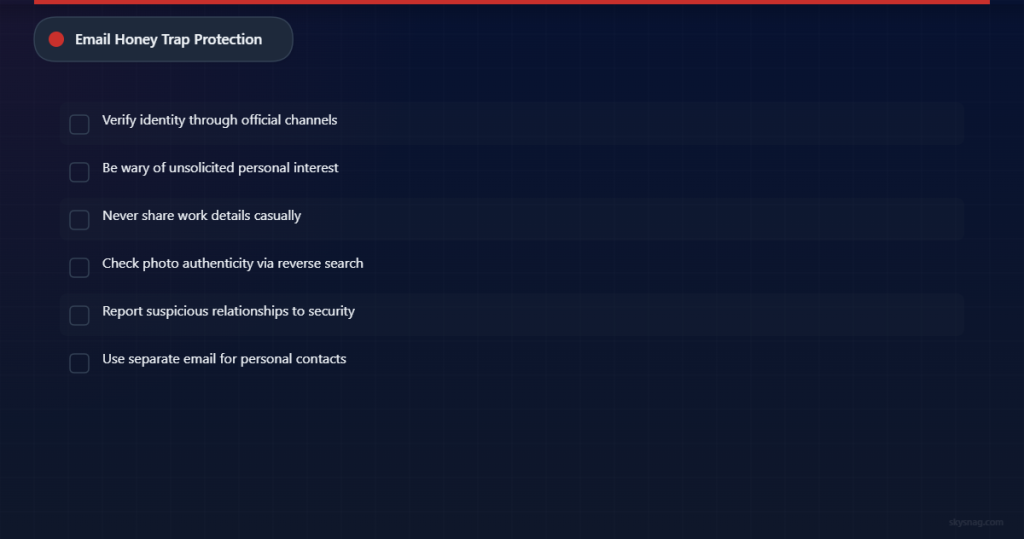
Defending against honey trap attacks requires a combination of technical controls, security awareness training, and organizational policies that account for the psychological sophistication of these threats.
Email Authentication and Security Controls
Implementing robust email authentication protocols provides the first line of defense against sophisticated social engineering attacks. Skysnag Protect (https://skysnag.com/protect/) enables organizations to configure DMARC policies that prevent domain spoofing and unauthorized email sending, making it significantly more difficult for attackers to impersonate trusted contacts or establish credible personas.
SPF and DKIM validation help ensure that emails claiming to be from legitimate domains are actually authorized by those domain owners, while DMARC reporting provides visibility into attempted impersonation attacks that might be part of honey trap campaigns.
Advanced email security solutions can also analyze communication patterns, flagging suspicious relationship-building behavior or unusual information requests that might indicate social engineering attempts.
Security Awareness Training
Traditional phishing awareness training often focuses on obvious threat indicators like urgent payment requests or suspicious links. Honey trap defense requires more nuanced education about relationship-based manipulation tactics.
Training programs should help employees recognize gradual information gathering attempts, understand the psychology of social engineering, and establish clear protocols for handling unsolicited personal communications in professional contexts.
Regular simulated honey trap exercises can help organizations assess their vulnerability to these longer-term deception campaigns and reinforce appropriate response procedures.
Policy and Procedural Controls
Organizations need clear policies governing employee communication with external contacts, particularly regarding information sharing and relationship disclosure requirements.
Policies should address acceptable use of corporate email for personal communications, mandatory reporting of suspicious relationship-building attempts, and escalation procedures when employees receive unusual requests from claimed personal contacts.
Technical Monitoring and Analysis
Security teams should implement monitoring capabilities that can detect unusual communication patterns, such as extended personal conversations with external addresses or gradual escalation in information requests.
Data loss prevention (DLP) solutions can help identify when employees are sharing sensitive information through email channels, regardless of whether the recipient appears trustworthy based on established communication history.
V. Industry Impact and Real-World Examples
Honey trap attacks have been documented across various industries, with particularly significant impact in sectors handling sensitive data or high-value intellectual property.
Financial services organizations frequently encounter honey traps targeting employees with access to customer data or transaction systems. These attacks often involve months of relationship building before attempting to extract account information or facilitate fraudulent transactions.
Government contractors and defense organizations face sophisticated nation-state honey trap campaigns designed to extract classified information or establish persistent access to sensitive systems.
Healthcare organizations have reported honey trap attempts targeting administrators with access to patient databases, with attackers building relationships over social media before transitioning to email-based information gathering.
VI. Key Takeaways
Honey trap attacks represent an evolution in social engineering that combines traditional phishing tactics with sophisticated psychological manipulation. These attacks exploit fundamental human needs for connection and trust, making them particularly effective against even security-aware individuals.
Organizations must recognize that technical security controls alone cannot defend against relationship-based deception. Effective defense requires comprehensive email authentication, targeted security awareness training, clear communication policies, and monitoring capabilities that can detect subtle social engineering patterns.
Understanding honey trap tactics helps security professionals develop more effective defense strategies and helps employees recognize when their natural social instincts might be exploited by cybercriminals. The time investment required for successful honey traps makes them attractive to sophisticated threat actors but also provides more opportunities for detection when organizations implement appropriate monitoring and reporting procedures.
By implementing robust email security controls like those available through Skysnag Protect and maintaining awareness of evolving social engineering tactics, organizations can better protect themselves against these emotionally manipulative cyber threats.