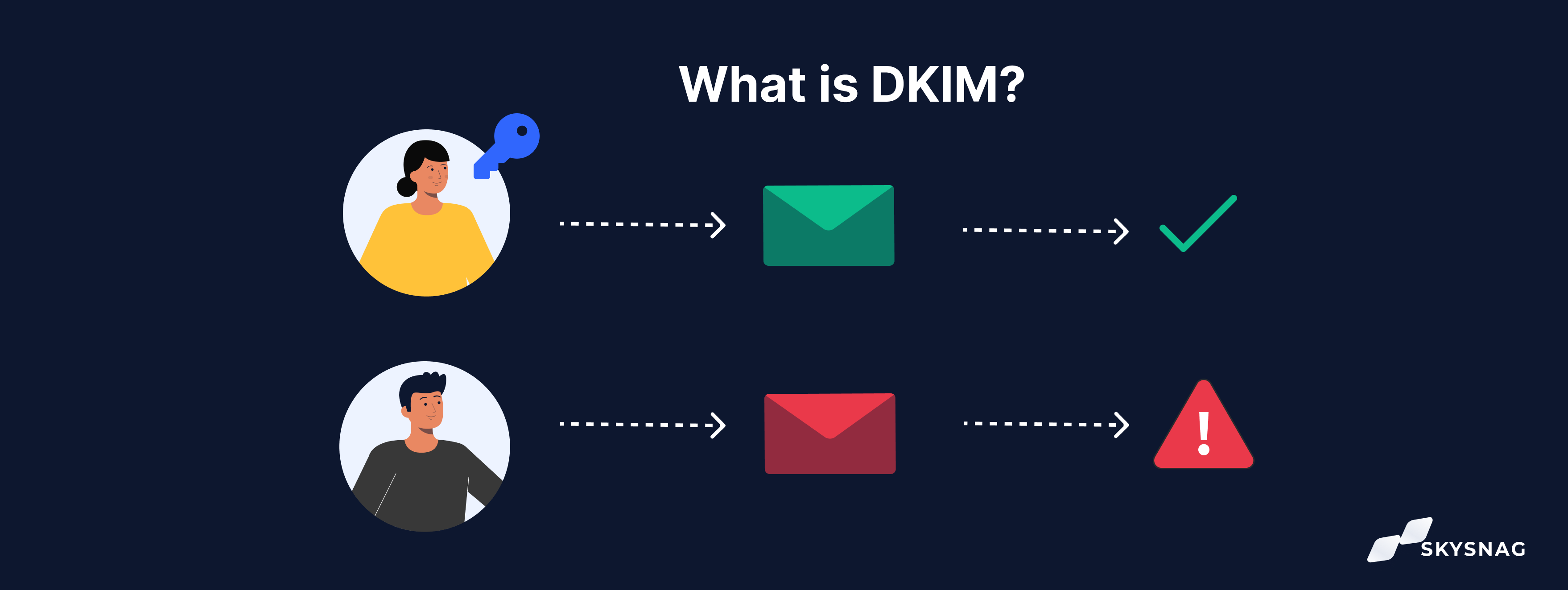
DKIM is an email authentication method that allows the receiving server to check if an email was sent and authorized by the owner of the email’s domain. The email is given a digital signature which is a header that is added to the message and secured with encryption.
Read more about the DKIM Signature
If an email is signed with a valid DomainKeys Identified Mail signature, it is certain that none of the message body or attachments have been altered from the time they were first sent until they arrive in your inbox. This means that when your receiver checks for a valid DKIM signature, it will be able to verify the integrity of all parts of the message. End users are not able to see DKIM signatures, the validation is done on the server level.
I. History of DKIM
The DomainKeys Identified Mail (DKIM) standard was developed in 2007 by a coalition of organizations including AOL, Google, Microsoft, and Yahoo! in order to help address the problem of email spoofing. DKIM uses public-key cryptography to verify that an email message has not been tampered with during transit and that it originated from the purported sender’s domain. It accomplishes this by adding a digital signature to each email message that can be used to verify the message’s authenticity.
In 2012, the Internet Engineering Task Force (IETF) published DomainKeys Identified Mail as an official standard (RFC 6376). Since then, it has been widely adopted by email service providers (ESPs) and other organizations as a way to help ensure the security and integrity of email messages.
II. How DKIM Works
Each DKIM-signed email message contains a DomainKeys Identified Mail-Signature header field that includes the following information:
- The sender’s domain name
- A selector for the DKIM key used to sign the message (e.g., “dkim” or “20170914”)
- The signature algorithm used (e.g., “rsa-sha256”)
- A cryptographic signature generated using the sender’s private key
When a message is received, the receiving mail server can use the information in the DKIM-Signature header field to verify the message’s authenticity. To do this, it will need to retrieve the public key corresponding to the selector and sender domain from a DNS record (known as a TXT record). Once it has the public key, it can use it to verify the message signature and ensure that the message has not been tampered with.
III. Why Use DKIM?
DKIM is an important tool for fighting email spoofing, which is a type of cyber attack that involves sending emails that appear to come from a legitimate sender but are actually from a different source. Email spoofing can be used for a variety of malicious purposes, such as phishing attacks or malware propagation.
DomainKeys Identified Mail can help to protect recipients from email spoofing attacks by verifying the authenticity of each email message. By verifying that each message has not been tampered with and that it originated from the purported sender’s domain, DKIM can help to ensure that recipients are not tricked by spoofed emails.
In addition to protecting recipients from email spoofing, DKIM can also help to improve an organization’s email deliverability. This is because many ESPs use DomainKeys Identified Mail to verify
IV. DKIM Header Syntax
DKIM-Signature: v=1; a=rsa-sha256; c=simple/simple; d=skysnag.com;
s=brisbane;
t=1217574938; bh=KWSe46TZS2+p7aR67F1kVb6nXyo4=;
h=Received:Mime-Version:Date:Message-ID:Subject:From:To:Content-Type;
[email protected];
b=dzdVyOfAKCdLXdJOc9G2q8LoXSlEniSbav+yuU4zGeeruW+s4U4VgFyL2ckaVzRp
SeAgiU6p4T+YGmJ3fWZA4kZBVTBQ5VVq3kR5YDw7x5fg+oZ6+V1R+nYZ4pZBXNK3+
qkjxqhw4kXlBYjYwvSpYrcYTtYC1Q4E1dWotZHUZSo=
The fields in the DKIM-Signature header are defined as follows:
| Tag | Description |
| V | Version. The current version is 1. |
| a | The signature algorithm used. This document defines only the rsa-sha256 algorithm. |
| c | The signature canonicalization algorithm(s) used. This document defines two signature canonicalization algorithms: “simple” and “relaxed”. |
| d | The signing domain. The domain of the message sender. |
| s | The selector. A string that identifies the DomainKeys Identified Mail public key record associated with the signing domain. |
| t | Signature timestamp. The signature timestamp is the number of seconds since January 1, 1970 that represents when the signature was calculated. |
| bh | The body hash. A hash of the message body. |
| h | The signature headers field. A colon-separated list that identifies the header fields presented to the signing algorithm. |
| i | The signature identity. A string is used to indicate the scope of control that the signer has over the message. (This may be used, e.g., by a corporate user to assert that he/she is acting within the scope of his/her employment rights and responsibilities.) |
| z | The signature trailing headers field. A colon-separated list that identifies the header fields that appear after the signature, that is, the signature trailing headers. |
| b | The signature data. A signature is generated by the algorithm specified in the “a” tag. |
| x | A signature expiration timestamp. The signature expiration |
To sum up, The DKIM-Signature header is used to sign messages for DKIM verification. The header includes the version of DomainKeys Identified Mail being used, the algorithm used to generate the hash, the canonicalization posture for the sending domain, the selector for the public DKIM key, the email domain that signed the message, the identity of the signer, the value of a body hash, and the cryptographic signature of all the preceding information.
V. DKIM Verification
DKIM verification starts by making sure the version number meets the DomainKeys Identified Mail specification, the identity of the sender’s domain matches the domain set in the signature, and the “h=“ tag contains the From header field. If these all check out, the recipient server tries to retrieve the public key for the sending domain using the “d=“ and “s=“ tags.
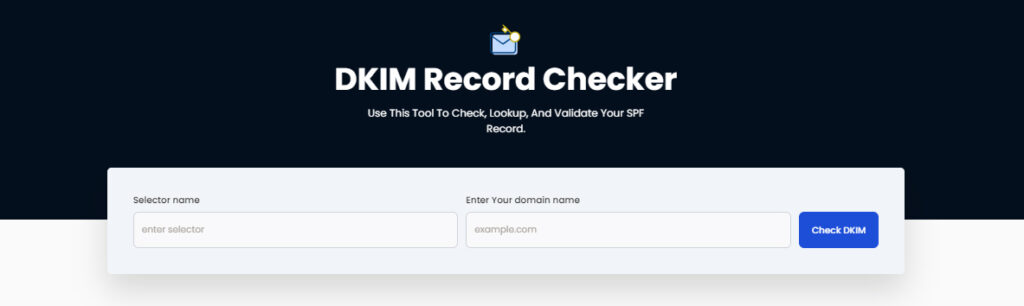
You can also use our free DKIM record checker tool to check and validate your record.
The public key is used to decrypt the encrypted hash that was sent along with the message. The receiving mail server then computes its own hash of the message. If the two hashes match, the message is allowed through.
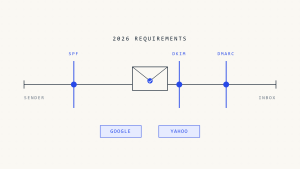
VI. Does DKIM Prevent Spoofing
DKIM alone doesn’t prevent spoofing. DKIM and DMARC work together to prevent spoofing. DomainKeys Identified Mail uses public-key cryptography to sign messages with a private key. The signature is then verified with a public key that is retrieved from the message sender’s DNS records. This ensures that only the owner of the private key can send messages that appear to come from the message sender’s domain. DMARC uses the results of DKIM and SPF checks to determine whether or not a message should be delivered. If DKIM or SPF fail, DMARC can instruct the receiving mail server to reject, quarantine, or deliver the message.
VII. DKIM role in deliverability
The key advantage of using DomainKeys Identified Mail is that it helps you to authenticate your email. By authenticating your email, you are telling your recipients that the message is coming from you and not from anyone else. This is important because it helps to improve your email deliverability.
When your email is authenticated, it is more likely to be delivered to the inbox instead of the spam folder. This is because authentication is one of the factors that ISPs use to determine whether an email should be delivered to the inbox or not.
Another advantage of using DomainKeys Identified Mail is that it can help you to avoid spam filters. This is because many spam filters use DomainKeys Identified Mail to determine whether an email is spam or not. If an email is not authenticated, it is more likely to be marked as spam.
Finally, using DKIM can help you to build a better reputation with ISPs. This is because ISPs often use DKIM to determine the sender’s reputation.
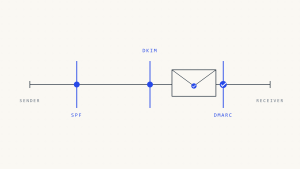
VIII. Relation between SPF, DKIM & DMARC
SPF and DMARC are used to authenticate email senders. DKIM is used to authenticate email messages.
SPF checks the sender’s IP address to ensure that it matches the IP address that is authorized to send emails to the sender’s domain.
DKIM uses cryptographic signatures to authenticate email messages. The signature is added to the message header, and the recipient can use the signature to verify that the message was not modified in transit and that it was sent by an authorized sender.
DMARC checks the SPF and DomainKeys Identified Mail authentication results for a message and determines whether the message should be delivered, quarantined, or rejected based on the sender’s configured policies.
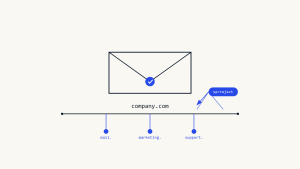
IX. How to set up a DKIM Key
The setup for DomainKeys Identified Mail is the same regardless of which ESP or mail server you use. You need to have a private key stored securely, and you need to share the public key in your domain’s DNS records. Like with SPF, DKIM uses DNS TXT records with a special format.
It’s generally considered best practice to rotate your DKIM keys regularly. The DKIM standard recommends rotating keys every quarter, and also recommends revoking old DKIM keys as part of the rotation process. The easiest way to manage this is by adding new keys and removing old ones from your DNS records a few days later. Skysnag is one of the only ESPs that makes this easy to manage by keeping your old private key active while your new public key propagates.
The best way to secure your domain’s email is by using DomainKeys Identified Mail in combination with SPF and DMARC. For more information on how these protocols work together to protect your domain, check out our other guides.
X. Conclusion
Skysnag’s automated DKIM solution helps you to inspect and verify your DKIM records while examining email messages’ origin and content in an effort to lower the amount of spam, phishing, and other harmful emails. In conjunction with this Skysnag automated software ensures your DKIM records are configured correctly. Get started with Skysnag and Sign up for a free trial today