The German Federal Office for Information Security (BSI) has established TR-03182 and TR-03108 as comprehensive frameworks for email security, with DMARC authentication playing a crucial role in protecting organizations from email-based cyber threats. As German organizations face increasing regulatory scrutiny and sophisticated phishing attacks, implementing BSI TR-03182 and TR-03108 compliant email security measures has become essential for maintaining robust cybersecurity postures.
This technical guide provides a complete implementation roadmap for achieving BSI TR-03182 and TR-03108 email security compliance through proper DMARC configuration and monitoring.
I. Understanding BSI TR-03182 & TR-03108 Email Security Requirements
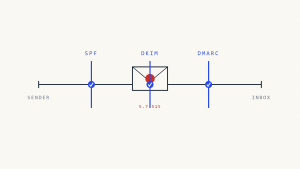
BSI TR-03182 “Secure Email Transport” and TR-03108 “Email Security Guidelines” provide detailed guidance for securing email communications in German organizations. Both frameworks emphasize email authentication protocols, including the essential DNS records for SPF, DKIM, and DMARC, alongside complementary security measures such as MTA-STS and TLS-RPT as foundational security controls.
The technical reports recommend implementing DMARC policies to prevent domain spoofing and establish authenticated email channels. The long-term goal under both frameworks is to enforce these security measures comprehensively, particularly under the BSI NIS2 Mandate which aims to enforce DMARC policies to p=reject sustainably across German critical infrastructure and essential services.
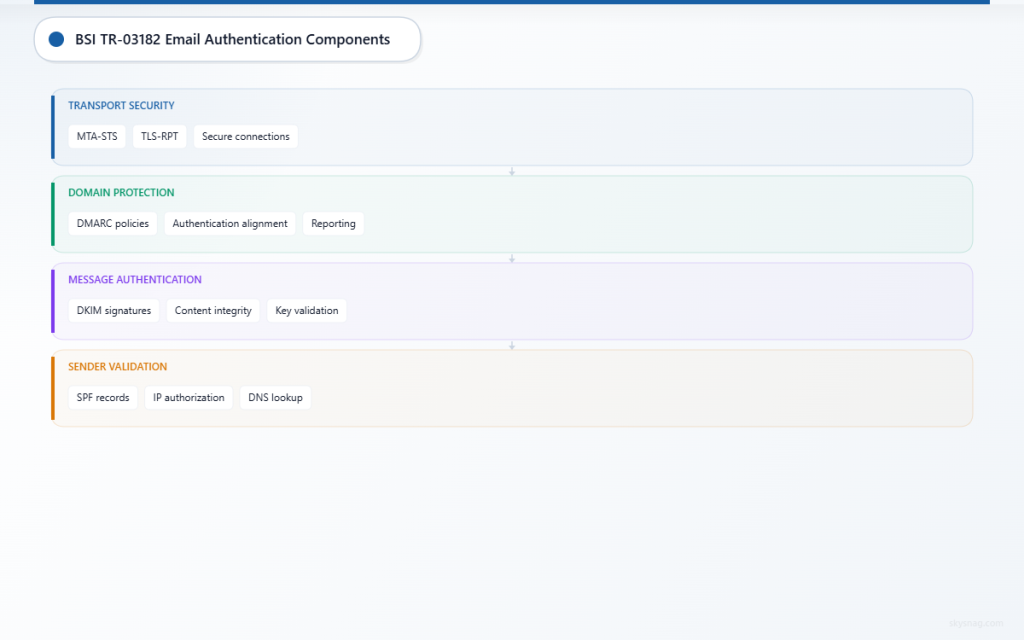
Key Email Authentication Components
SPF (Sender Policy Framework)
- Validates sending IP addresses against published DNS records
- Prevents basic email spoofing by unauthorized mail servers
- Forms the foundation for DMARC authentication
DKIM (DomainKeys Identified Mail)
- Provides cryptographic signatures for email authentication
- Ensures email content integrity during transmission
- Enables receiving systems to verify message authenticity
DMARC (Domain-based Message Authentication, Reporting and Conformance)
- Builds upon SPF and DKIM for comprehensive domain protection
- Provides policy instructions for handling authentication failures
- Generates detailed reports for security monitoring and compliance evidence
MTA-STS (Mail Transfer Agent Strict Transport Security)
- Enforces secure connections and certificate validation for email delivery
- Prevents man-in-the-middle attacks during email transmission
- Complements DMARC by securing the transport layer
TLS-RPT (TLS Reporting)
- Provides visibility into TLS connection failures and security issues
- Enables monitoring of email encryption effectiveness
- Supports compliance reporting for transport security measures
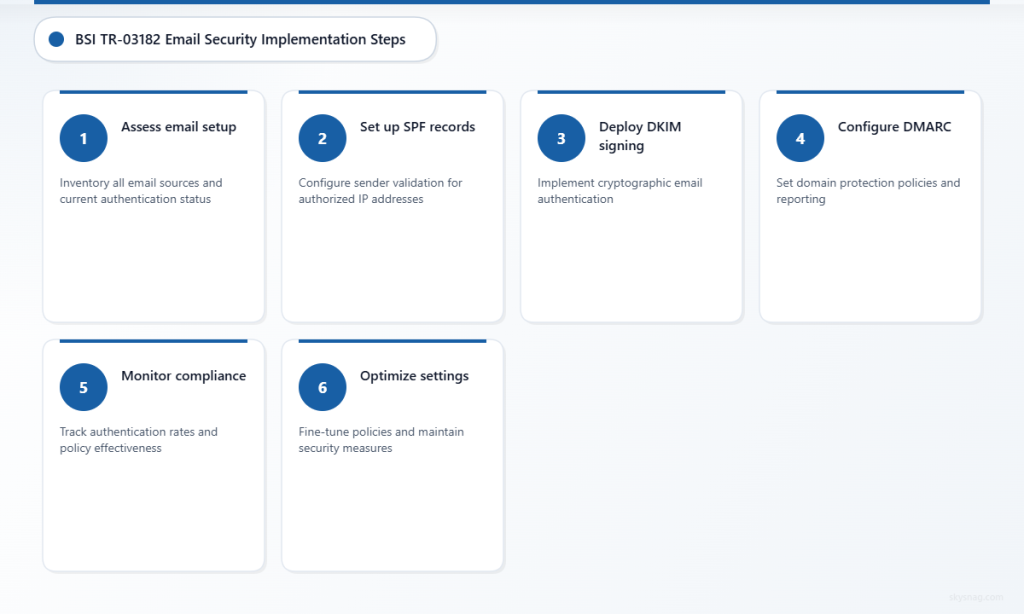
II. Step 1: Conduct Email Infrastructure Assessment
Before implementing BSI TR-03182 and TR-03108 email security controls, organizations must thoroughly assess their current email infrastructure and authentication status.
Inventory Email Sources
Document all systems authorized to send email on behalf of your organization:
- Primary mail servers and Exchange systems
- Marketing automation platforms and CRM systems
- Cloud applications with email notification capabilities
- Third-party services sending transactional emails
- Backup and disaster recovery email systems
Analyze Current Authentication Status
Use DNS lookup tools to check existing email authentication records:
dig TXT domain.com | grep "v=spf1"
dig TXT _dmarc.domain.com
dig TXT selector._domainkey.domain.comReview authentication headers in received emails to understand current SPF and DKIM alignment rates. This baseline assessment helps identify authentication gaps that must be addressed for BSI TR-03182 and TR-03108 compliance.
Document Email Flows
Map all legitimate email flows through your infrastructure, including:
- Internal user communications and automated system notifications
- Customer-facing communications and support ticket systems
- Business partner communications and vendor notifications
- Emergency communications and incident response procedures
III. Step 2: Implement SPF Records for Sender Validation
Proper SPF configuration forms the foundation of BSI TR-03182 and TR-03108 email security implementation. SPF records must accurately reflect all authorized sending sources while maintaining strict validation policies.
Configure Comprehensive SPF Records
Create SPF records that include all legitimate mail sources identified during your infrastructure assessment:
v=spf1 include:_spf.google.com include:mailgun.org ip4:203.0.113.0/24 -allSPF Mechanism Guidelines:
- Use “include:” mechanisms for third-party services with established SPF records
- Specify individual IP addresses with “ip4:” for dedicated mail servers
- Implement “~all” (soft fail) initially during testing phases
- Transition to “-all” (hard fail) once all legitimate sources are verified
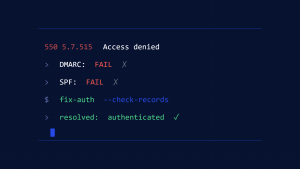
Validate SPF Implementation
Test SPF records using multiple validation tools and monitor email delivery metrics. Send test emails from all authorized sources and verify proper SPF authentication in message headers.
Monitor bounce rates and delivery failures during SPF implementation to identify any legitimate sources that were inadvertently excluded from authentication policies.
IV. Step 3: Deploy DKIM Signing Infrastructure
DKIM implementation provides cryptographic authentication that supports BSI TR-03182 and TR-03108 email security objectives. Organizations must configure DKIM signing for all outbound email sources.
Generate DKIM Key Pairs
Create unique DKIM key pairs for each sending domain and selector:
- Use 2048-bit RSA keys for strong cryptographic security
- Generate separate key pairs for different email sources when possible
- Implement key rotation procedures for ongoing security maintenance
Configure DKIM DNS Records
Publish DKIM public keys in DNS using the standard selector format:
selector1._domainkey.domain.com TXT "v=DKIM1; k=rsa; p=MIGfMA0GCSqGSIb3DQEBAQUAA..."Enable DKIM Signing
Configure all email systems to sign outbound messages with appropriate DKIM keys:
- Email servers must sign messages with corresponding private keys
- Third-party services require DKIM configuration through administrative interfaces
- Test DKIM signatures using email authentication validators
V. Step 4: Configure DMARC Policies for Domain Protection
DMARC implementation represents the culmination of BSI TR-03182 and TR-03108 email authentication deployment. Proper DMARC configuration provides policy-based protection against domain spoofing while generating compliance reporting data.
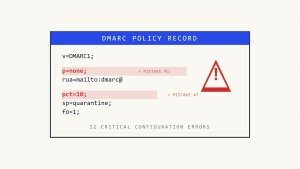
Start with Monitoring Mode
Deploy initial DMARC policies in monitoring mode to gather authentication data without impacting email delivery:
_dmarc.domain.com TXT "v=DMARC1; p=none; rua=mailto:[email protected]; ruf=mailto:[email protected]; sp=none; adkim=r; aspf=r;"Policy Parameters:
- p=none: Monitor authentication without enforcement
- rua=: Aggregate report destination for daily authentication summaries
- ruf=: Forensic report destination for detailed failure analysis
- adkim=r, aspf=r: Relaxed alignment for initial deployment
Analyze DMARC Reports
Skysnag Protect provides comprehensive DMARC report analysis capabilities that help organizations understand their email authentication landscape and identify security gaps. The platform processes aggregate and forensic reports to provide actionable insights for BSI TR-03182 and TR-03108 compliance.
Monitor DMARC reports for several weeks to identify:
- Authentication success rates across all email sources
- Legitimate senders failing SPF or DKIM validation
- Potential spoofing attempts and unauthorized sending activity
- Third-party services requiring additional authentication configuration
Implement Enforcement Policies
After achieving high authentication success rates, transition to enforcement policies:
_dmarc.domain.com TXT "v=DMARC1; p=quarantine; rua=mailto:[email protected]; ruf=mailto:[email protected]; sp=quarantine; adkim=s; aspf=s; pct=100;"Progress through policy enforcement levels:
- p=quarantine: Treat failing messages as suspicious
- p=reject: Block failing messages entirely
- Strict alignment (adkim=s, aspf=s): Require exact domain matching
VI. Step 5: Establish Monitoring and Compliance Reporting
BSI TR-03182 and TR-03108 compliance requires ongoing monitoring of email authentication effectiveness and security incident detection capabilities.
Configure Automated Report Processing
Implement systems to automatically process and analyze DMARC reports:
- Parse aggregate reports for authentication trend analysis
- Alert on forensic reports indicating potential security incidents
- Generate compliance dashboards showing authentication success rates
- Archive reports for audit trail and compliance evidence
Create Security Monitoring Procedures
Establish operational procedures for responding to email authentication failures:
- Investigate forensic reports for potential spoofing attempts
- Update SPF and DKIM records when new email sources are deployed
- Monitor third-party service authentication status and policy changes
- Coordinate incident response procedures for email security events
Document Compliance Evidence
Maintain comprehensive documentation of BSI TR-03182 and TR-03108 email security implementation:
- Configuration records for SPF, DKIM, and DMARC policies
- Authentication success rate reports and trend analysis
- Incident response logs for email security events
- Policy review and update procedures with approval workflows
VII. Step 6: Maintain and Optimize Email Authentication
Ongoing maintenance ensures continued effectiveness of BSI TR-03182 and TR-03108 email security controls as organizational infrastructure evolves.
Regular Policy Reviews
Schedule quarterly reviews of email authentication policies:
- Verify all legitimate email sources maintain proper authentication
- Remove obsolete SPF includes and DKIM selectors for decommissioned systems
- Assess DMARC policy effectiveness and consider tightening enforcement
- Update documentation reflecting infrastructure changes
Key Rotation and Security Updates
Implement regular security maintenance procedures:
- Rotate DKIM keys annually or when security incidents occur
- Monitor for new email authentication standards and best practices
- Update DNS TTL values to enable rapid policy changes when required
- Test disaster recovery procedures including email authentication restoration
According to the Cybersecurity and Infrastructure Security Agency (CISA), organizations with comprehensive email authentication see significantly reduced success rates for phishing campaigns targeting their domains.
VIII. Advanced BSI TR-03182 & TR-03108 Implementation Considerations
Multi-Domain Organizations
Large German organizations often manage multiple domains requiring coordinated email authentication policies:
- Implement consistent authentication policies across all organizational domains
- Configure centralized DMARC reporting for unified security monitoring
- Coordinate subdomain policies (sp=) with organizational email usage patterns
- Establish delegation procedures for subsidiary domain management
Cloud Service Integration
Modern organizations rely heavily on cloud services that must integrate with BSI TR-03182 and TR-03108 email security frameworks:
- Configure SPF records to include all cloud-based email services
- Coordinate DKIM signing between cloud providers and organizational domains
- Implement DMARC policies that accommodate cloud service authentication patterns
- Monitor cloud service policy changes that might impact authentication alignment
International Communication Requirements
German organizations with international operations must balance BSI TR-03182 and TR-03108 compliance with global email communication needs:
- Consider regional email delivery requirements when implementing strict DMARC policies
- Coordinate with international subsidiaries for consistent authentication policies
- Monitor cross-border email authentication success rates
- Document compliance frameworks in different jurisdictions
IX. Key Takeaways
Implementing BSI TR-03182 and TR-03108 email security compliance requires a systematic approach to email authentication deployment and ongoing monitoring. Organizations must thoroughly assess their email infrastructure, implement comprehensive SPF and DKIM authentication, and deploy DMARC policies with appropriate monitoring and enforcement levels.
Success depends on careful planning, phased implementation, and continuous monitoring of authentication effectiveness. Skysnag Protect provides the advanced DMARC analysis and reporting capabilities necessary for maintaining BSI TR-03182 and TR-03108 compliance while protecting against evolving email-based security threats.
The investment in proper email authentication pays dividends through reduced phishing success rates, improved email deliverability, and demonstrable compliance with German cybersecurity best practices. Organizations that implement these controls position themselves to defend against sophisticated email threats while meeting evolving regulatory expectations.
Ready to implement BSI TR-03182 and TR-03108 compliant email security? Start with Skysnag Protect to deploy comprehensive DMARC monitoring and achieve robust email authentication compliance.