If your organization relies extensively on email for both external and internal communications, DMARC failure for your messages is cause for concern. In this article, we’ll better understand how Skysnag will assist you in fixing this when it happens. Let’s look at some definitions first for a better understanding of how to fix this problem.
I. What is DMARC?
DMARC, or Domain-based Message Authentication, Reporting, and Conformance is an email authentication protocol that is designed to help protect email users from spam, phishing, and other types of email-based attacks.
II. How does DMARC work?
DMARC works by verifying that an email message is from the sender that it claims to be from, and then reporting any suspicious activity to the email recipient’s ISP or email provider.
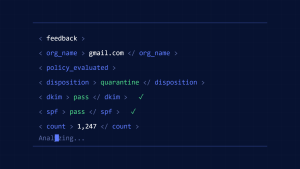
The DMARC protocol uses email authentication policies and reporting to detect and prevent email spoofing. DMARC works by validating the alignment of both the “From:” and “Return-Path:” headers of an email message to ensure that they match the domain from which the message was sent. If the message fails DMARC validation, it can be reported, blocked, or quarantined by the receiving email server.
III. What causes a DMARC fail?
Finding the cause of DMARC failure can be challenging. To help you as the domain owner work toward a quicker resolution, I will go over some common failures and the variables that lead to them.
DMARC Alignment
A DMARC alignment failure occurs when the domain in the “From:” header of an email does not match the domain specified in the DMARC record for that email. This can happen if the email was sent from a different email address than the one specified in the DMARC record, or if the email was forwarded from another email address.
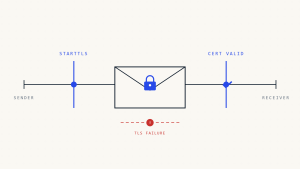
Misconfigured Key
A misconfigured key is the primary cause of DKIM failure. The DNS record’s public key is used by the email recipient to validate the signature. Verification is unsuccessful if the key is flawed.
This states that the message was changed after it was signed. This might occur if the message is forwarded or if it passes through a mailing list that changes it in some way.
Some email service providers use a testing key that is not DNS-published to sign each message. Thus, they can try out their DKIM implementation without having any negative effects on their users, so be aware.
Absence of Sending Sources in DNS
Remember that when you configure DMARC for your domain, receiving MTAs run DNS searches to validate your transmitting sources. As a result, unless all of your permitted sending sources are listed in your domain’s DNS, the recipients of your emails will not be able to locate them in your DNS, resulting in DMARC failure for those sources. Therefore, be sure to make entries on all your permitted third-party email suppliers that are authorized to send emails on behalf of your domain, in your DNS, to ensure that your genuine emails are always sent.
IV. Authenticate DMARC for third-party email senders
In order to fully verify DMARC, third-party senders need to implement DMARC for their clients. They can help to ensure that messages from these sources are properly authenticated and that any spoofed messages are detected and blocked. This is especially important for organizations that receive a lot of emails from third-party sources, such as partners, vendors, and customers. By authenticating these messages, organizations can help to protect themselves from email-based attacks that use spoofed messages from these sources.
V. How to fix DMARC failure with Skysnag?
There are a few things you can do to fix DMARC failure with Skysnag these include:
1. Check your DNS records with Skysnag to ensure they are correct and up-to-date.
2. Use our free SPF and DKIM record checker tools to confirm email authentication protocols are correctly configured.
3. Subsequently, we assist you in transitioning to a mandated policy that will eventually help you develop immunity against domain spoofing and phishing attacks.
We recommend that you sign up with our free DMARC Checker tool and monitor DMARC to avoid these failures.
Learn why SPF and DKIM pass but DMARC fails.
VI. Conclusion
It is just as necessary to set up your DMARC record as it is to define an authorized valid domain in your SPF TXT record and to set up your DKIM key. Skysnag automates DMARC, SPF, and DKIM for you, saving you the trouble and time required for manual configuration
Create a Skysnag account here to generate your DMARC record
Avoid DMARC failures right away and use Skysnag’s automated software to safeguard your domain’s reputation and keep away from compromised business emails, password theft, and potentially significant financial losses. Sign up using this link and monitor your email flow with Skysnag