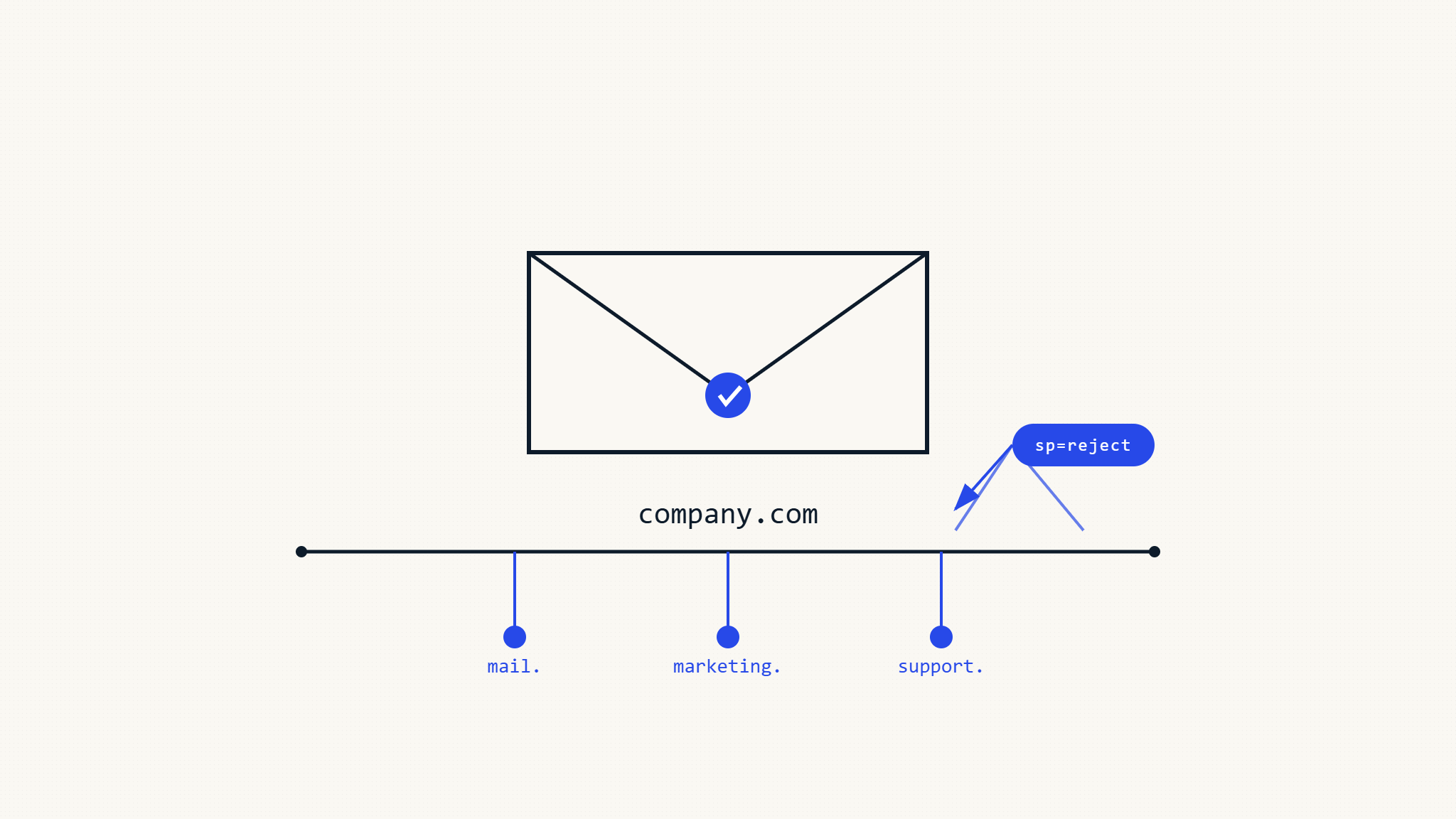
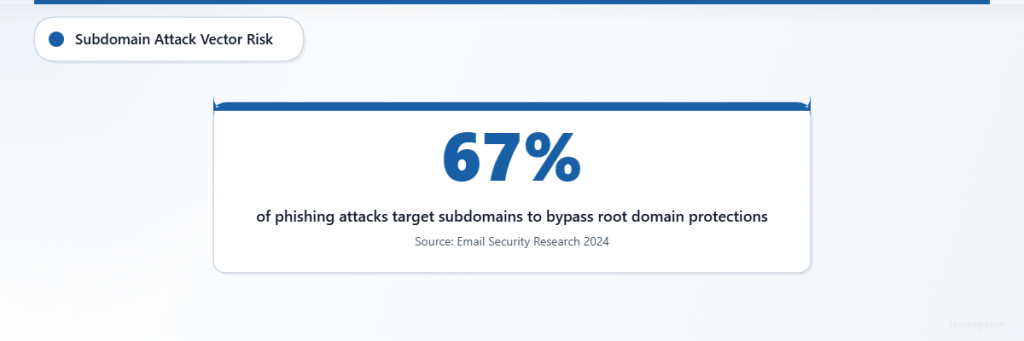
DMARC protection doesn’t stop at your root domain. While most organizations focus on securing their primary domain, cybercriminals increasingly target subdomains to bypass email authentication controls. Understanding DMARC subdomain policies and the sp tag configuration ensures comprehensive protection across your entire domain infrastructure.
I. Understanding DMARC Subdomain Inheritance
DMARC operates on an inheritance model where subdomains automatically inherit the policy of their parent domain unless explicitly overridden. When you publish a DMARC policy for example.com, subdomains like mail.example.com and marketing.example.com inherit that same policy by default.
However, this inheritance only applies when no specific DMARC record exists for the subdomain. If marketing.example.com has its own DMARC record, it will use that policy instead of inheriting from the root domain.
Default Inheritance Behavior
Consider this root domain DMARC record:
_dmarc.example.com. IN TXT "v=DMARC1; p=quarantine; rua=mailto:[email protected]"Without explicit subdomain policies, all subdomains inherit the quarantine policy. This means:
- mail.example.com inherits p=quarantine
- shop.example.com inherits p=quarantine
- api.example.com inherits p=quarantine
This inheritance provides baseline protection but may not suit all organizational needs.
II. The DMARC sp Tag: Subdomain Policy Control
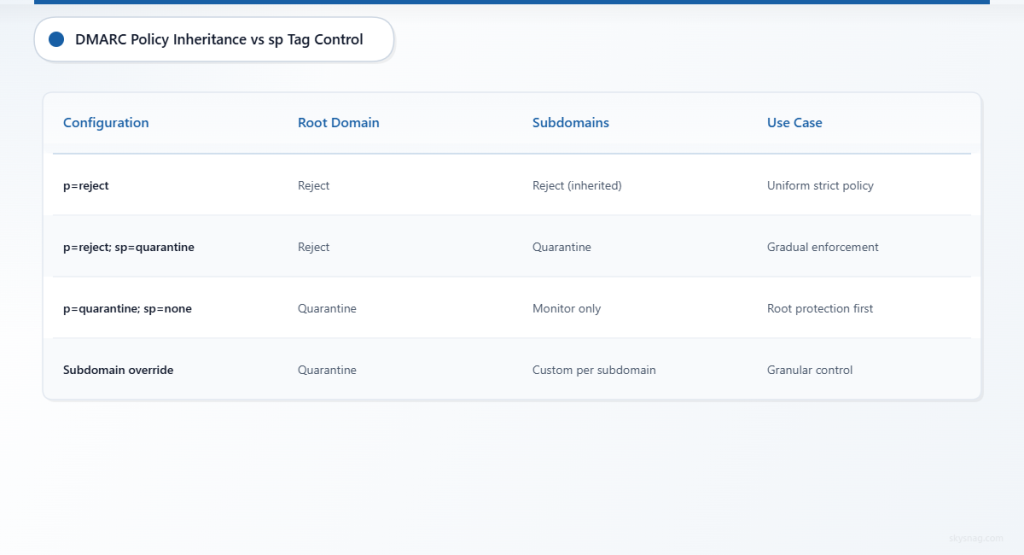
The sp (subdomain policy) tag allows organizations to specify different policies for subdomains while maintaining separate root domain policies. This granular control addresses scenarios where subdomains require different treatment than the primary domain.
sp Tag Syntax and Values
The sp tag accepts the same values as the main policy tag:
sp=none– Monitor subdomain authentication without enforcementsp=quarantine– Treat failing subdomain messages as suspicioussp=reject– Block subdomain messages that fail authentication
Strategic sp Tag Implementation
A common configuration combines strict root domain protection with gradual subdomain enforcement:
_dmarc.example.com. IN TXT "v=DMARC1; p=reject; sp=quarantine; rua=mailto:[email protected]"This policy:
- Rejects unauthenticated messages from the root domain
- Quarantines unauthenticated messages from subdomains
- Provides gradual enforcement while maintaining security
III. Advanced Subdomain Configuration Scenarios
Scenario 1: High-Security Root with Monitoring Subdomains
Organizations with critical root domain communications often implement strict root policies while monitoring subdomain activity:
_dmarc.example.com. IN TXT "v=DMARC1; p=reject; sp=none; rua=mailto:[email protected]; pct=100"This configuration protects the primary domain while gathering intelligence on subdomain usage patterns.
Scenario 2: Graduated Enforcement Across Domain Hierarchy
Some organizations prefer stepped enforcement levels:
_dmarc.example.com. IN TXT "v=DMARC1; p=quarantine; sp=none; rua=mailto:[email protected]"This approach allows monitoring of subdomain authentication while maintaining moderate root domain protection.
Scenario 3: Subdomain-Specific Override Records
For precise control, organizations can publish specific DMARC records for individual subdomains:
_dmarc.marketing.example.com. IN TXT "v=DMARC1; p=reject; rua=mailto:[email protected]"
_dmarc.api.example.com. IN TXT "v=DMARC1; p=none; rua=mailto:[email protected]"These records override both root domain and sp tag policies for their respective subdomains.
IV. Subdomain Discovery and Monitoring
Effective subdomain DMARC implementation requires comprehensive subdomain discovery. Organizations often underestimate their subdomain footprint, missing critical attack vectors.
Common Overlooked Subdomains
Security teams frequently miss these subdomain categories:
- Development and staging environments (dev.example.com, staging.example.com)
- Third-party integrations (webhook.example.com, api.example.com)
- Legacy applications (old.example.com, archive.example.com)
- Regional or departmental subdomains (us.example.com, hr.example.com)
DMARC Reporting for Subdomain Visibility
DMARC aggregate reports provide visibility into subdomain email activity. The rua tag in your root domain policy receives reports for all subdomains unless they have specific DMARC records with different reporting addresses.
Skysnag Protect automatically discovers and monitors subdomain activity through DMARC report analysis, helping organizations identify previously unknown email-sending subdomains.
V. Implementation Best Practices
Gradual Subdomain Policy Deployment
Start with monitoring across all subdomains before implementing enforcement:
- Phase 1: Deploy
p=none; sp=noneto establish baseline reporting - Phase 2: Move to
p=quarantine; sp=nonefor root domain protection - Phase 3: Implement
p=quarantine; sp=quarantinefor comprehensive coverage - Phase 4: Progress to
p=reject; sp=rejectafter validation
Alignment Requirements and Subdomains
DMARC alignment requirements apply equally to subdomains. For subdomain messages to pass DMARC:
- SPF must align with the subdomain (relaxed) or exact match (strict)
- DKIM signatures must align with the parent domain (relaxed) or subdomain (strict)
Consider alignment implications when configuring subdomain policies, especially for marketing automation and transactional email services.
Testing Subdomain Configurations
Before implementing enforcement policies, test subdomain configurations thoroughly:
- Verify SPF records include all subdomain sending sources
- Ensure DKIM signatures align properly with domain policies
- Monitor DMARC reports for unexpected subdomain authentication failures
- Test email delivery from all active subdomains
VI. Compliance and Subdomain Coverage
Organizations subject to regulatory requirements should ensure comprehensive subdomain coverage supports their compliance objectives. While specific regulations may not explicitly mandate DMARC subdomain policies, comprehensive email authentication demonstrates due diligence in protecting against phishing and spoofing attacks.
Industries handling sensitive data often implement strict subdomain policies as part of broader cybersecurity frameworks. The sp tag provides the flexibility to balance security requirements with operational needs across different subdomain functions.
VII. Common Subdomain Policy Mistakes
Overly Permissive Subdomain Policies
Setting sp=none indefinitely creates persistent blind spots in email security coverage. While monitoring phases are important, organizations should progress toward enforcement policies based on reporting data.
Inconsistent Policy Logic
Implementing stricter root domain policies while maintaining permissive subdomain policies can create security gaps. Attackers may target weakly protected subdomains to bypass root domain controls.
Missing Subdomain Discovery
Deploying DMARC policies without comprehensive subdomain discovery leaves unknown attack vectors unprotected. Regular subdomain enumeration and monitoring ensures comprehensive coverage.
VIII. Advanced sp Tag Considerations
Wildcard Subdomain Implications
The sp tag applies to all current and future subdomains under the root domain. This includes dynamically created subdomains and wildcard DNS configurations. Organizations using dynamic subdomain creation should carefully consider sp tag implications for automated systems.
Multi-Level Subdomain Inheritance
For multi-level subdomains (like mail.marketing.example.com), DMARC inheritance follows the organizational domain structure. The most specific available policy applies, whether from the immediate parent, organizational domain, or root domain.
IX. Integration with Email Security Platforms
Modern email security platforms like Skysnag Protect provide centralized management of subdomain DMARC policies, automatically tracking policy inheritance and identifying configuration gaps. This visibility proves essential for organizations managing complex domain infrastructures.
Automated policy management helps ensure consistent protection levels across root domains and subdomains while providing the flexibility to implement granular controls where business requirements demand different approaches.
X. Key Takeaways
DMARC subdomain policies provide essential protection beyond root domain coverage. The sp tag offers flexible policy control, allowing organizations to balance security requirements with operational needs across different subdomain functions.
Successful subdomain DMARC implementation requires comprehensive subdomain discovery, gradual policy deployment, and ongoing monitoring through aggregate reports. Organizations should avoid common pitfalls like overly permissive policies and inconsistent enforcement logic.
Skysnag Protect simplifies subdomain DMARC management through automated discovery, centralized policy control, and comprehensive reporting across your entire domain infrastructure.