We’ll explain how to configure DMARC for your company’s email, including what you’ll need and how to add DMARC to your DNS. Just follow these DMARC setup steps!
Before we begin, here’s a high-level overview of how to add DMARC to your DNS with Skysnag.
- Create a Skysnag account to generate the record here
- Add your DMARC record into your DNS
- Select the TXT record type
- Add the host value
- Add the value information
- Validate the DMARC setup
For more details, read on. Or skip to the step-by-step instructions.
I. Why DMARC?
Email has never been more significant due to its extreme ubiquity and indisputable utility. Due to a serious defect, anyone can send email using someone else’s identity, hence it has never been secure. And because of that one fact, email is now worth $700 million per month to cybercriminals who use hacked business email accounts to pose as well-known companies and top executives in phishing attacks on users, clients, and the general public.
Organizations can avoid all of this with the use of DMARC. How? Read on.
II. DMARC Demystified
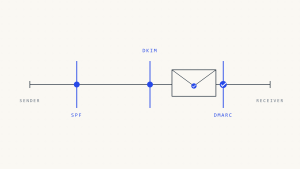
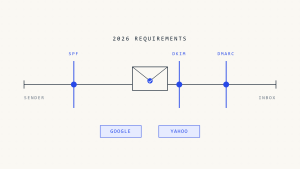
DMARC is an open standard authentication mechanism that works with SPF and DKIM to stop the fraudulent use of genuine brands in email attacks. It was first developed in 2012 by a group of industry professionals. Worldwide, more than 2.5 billion mailboxes have DMARC enabled.
With Skysnag having automated DMARC for you, you can:
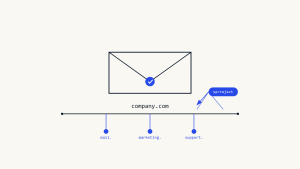
- Verify the legitimacy of all email sent from authorized sources, including your own infrastructure, business units, and third-party email partners, for your email-sending domains.
- Learn how your domains are being used legitimately and fraudulently so you can collaborate with takedown vendors to stop thieves from using your name in email scams.
III. What is a DMARC Enforcement Policy?
You can tell email receiving systems what to do when emails claiming to be from your approved domains fail authentication by setting a DMARC enforcement policy for your company. Among these regulations are:
- p=none: Email is delivered without restriction to its intended recipient.
- p=quarantine: Email that cannot be authenticated is delivered to the garbage folder of the intended recipient.
- p=reject: When an email’s authentication is unsuccessful, it is erased and never reaches its intended recipient.
IV. The Mechanics of DMARC
DMARC uses DNS as the mechanism for policy publication. DMARC records are hosted as TXT DNS records in a DMARC specific namespace, which is created by prepending “_dmarc” to the email domain.
For example, if the email domain “example.com” publishes a DMARC record, issuing a DNS query for the TXT record at “_dmarc.example.com,” will retrieve the DMARC record.
Email receiver systems use the policies published to inform how they process emails purporting to come from the sender’s email domain.
V. DMARC Setup Steps for Your DNS
You should have SPF and DKIM deployed and authenticating messages for at least 48 hours before setting up DMARC. Then, you can follow these DMARC setup steps to add DMARC to your DNS.
Step 1: Create a DMARC Record
- Create a Skysnag account to generate your DMARC record
Step 2: In your DNS, follow these DMARC setup steps to create a DNS TXT record
- Log into the management console of your DNS hosting provider, and while this can vary by provider, you want to locate the page that allows you to add a DNS TXT record
Step 3: In the Type box, select TXT Record Type
Step 4: In the Host Value box, enter _dmarc as the “host”
Step 5: In the TXT Value box, enter the record you created using the DMARC Record Creator
Step 6: Save the DMARC record
Step 7: Validate the DMARC setup
- Use Skysnag’s DMARC checker tool to verify that DMARC has been set up correctly
VI. Taking DMARC to Scale
It doesn’t take long to configure DNS for DMARC. However, DMARC must be configured with its strictest enforcement level, p=reject, in order to be effective against brand imitation.
With Skysnag, large enterprises have, however, been able to quickly reduce phishing-based brand impersonations to almost zero when deploying our automated DMARC solution. This not only has helped safeguard the reputation of our clients but also the effectiveness of revenue-generating email campaigns, as well as protection from expensive email scams. Sign up today using this link.