DMARC Explained
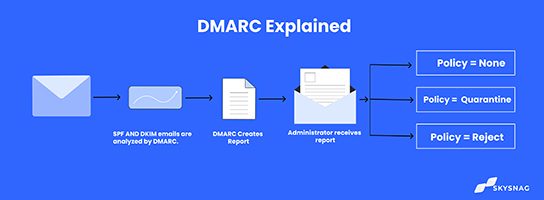
DMARC builds on the widely deployed sender and recipient protocols such as SPF & DKIM. DMARC adds reporting capability from receivers to senders, to identify authentication protocol failures and protect the domain from misusage.
DMARC is the only technology that authenticates the header “From” domain and makes sure it is trustworthy in any outbound email. The domain admin creates a DMARC record in the Domain Name System and adds a policy to tell receiving mail servers what to do with emails that fail authentication.
SPF and DKIM
Sender Policy Framework (SPF) is an email protocol that permits an organization to specify who can send an email on its behalf. Organizations can add senders within an SPF record published in the Domain Name System (DNS).
During mail delivery, SPF allows the recipient mail server to verify that a message appearing to come from a given domain is sent from an IP address approved by the domain’s administrators. The list of the allowed IP addresses of email senders and the IP addresses of third-party providers is published in the DNS record of that domain. Creating Publishing and checking SPF records is the most reliable way to stop phishing and other email attacks. It detects any forged IP address and fails it.
DKIM (DomainKeys Identified Mail) is an email authentication mechanism that allows a recipient’s mail server to confirm that the domain administrator has authorized an email from that specific domain by attaching a digital signature to a message. The digital signature assures that no email elements have been changed since it was attached.
DKIM uses “public-key cryptography” to verify that an email message was delivered from an authorized mail server, which helps detect forgery and dangerous emails like spam.
Why is DMARC important?
As more and more businesses move to the cloud, targeting user data has become more lucrative for hackers; increasing password theft, bank accounts, credit cards, and more.
Email is an easy target for criminals to take advantage of user trust in renowned brands. Email spoofing has become more widespread since simple actions like inserting the logo of a reputable brand makes an email appear legitimate for many users.
Most internet users can’t distinguish a real message from a fake one, and large mailbox providers have to choose which messages to deliver and which ones might harm users.
By having Domain-based Message Authentication, Reporting, and Conformance enforcement in place, domain owners, from large to small businesses, can protect their business emails and reputation against phishing, spoofing, brand abuse, and other cybercrimes.
How does DMARC work?
DMARC builds on the widely deployed sender and recipient protocols such as SPF and DKIM. According to the policies defined actions in the DMARC record, emails are handled.
DMARC tells the receiver what to do with an email according to the SPF & DKIM checks. If a policy is at (p=none) it means that all emails are being delivered whether they are passing authentication checks or not.
To deploy Domain-based Message Authentication, Reporting, and Conformance enforcement, you need to issue a DMARC record within the DNS. A DMARC record is a text entry inside the DNS record that informs the world of your email domain’s policy according to SPF and DKIM status. SPF and DKIM pass based on identifier alignment, but DMARC may fail.
DMARC records help Internet Service Providers (ISPs) prevent malicious email practices, such as domain spoofing. These records are published in the DNS as text (TXT) resource records (RR) and decide what the receiver sever reacts to the non-aligned mail it receives. Check what a DMARC record looks like by typing < dig txt _dmarc.domain.com in your terminal.
Create a Skysnag account to generate your DMARC record.
How do policies work?
DMARC has 3 policies that can be specified by the domain owners.
- p=none ( Only monitors outbound emails, no action is taken)
- p=quarantine ( sends unauthorized emails to the spam folder)
- p=reject (****The best and ultimate goal of implementing DMARC. This policy ensures that unauthorized email doesn’t get delivered at all)
Do I need DMARC?
Suppose you’re a business, and you send commercial or transactional emails. In that case, it’s essential to use email authentication techniques to validate that an email is actually from you or your company. This will help protect your reputation and ensure that customers receive legitimate messages from you. DMARC is an essential tool for protecting your domain from fraudulent email. When properly configured, it can help mail servers determine how to evaluate messages that claim to be from your company. This helps improve your deliverability and protect your reputation. Standards like Domain-based Message Authentication, Reporting, and Conformance are a must for any organization that sends emails.
What is a DMARC report?
DMARC reports are generated by receiving mail servers. There are two formats of DMARC reports:
- Aggregate reports XML documents containing statistical data about the emails received that claim to be from a specific domain. Aggregate reports are designed to be machine-readable. A DMARC report specifies authentication outcomes.
- Forensic reports are individual copies of failed authentication messages, each included in a whole email message using an AFRF format. Forensic information is used to identify fraudulent domains and websites and troubleshoot domain authentication difficulties.
Conclusion
Skysnag’s automated DMARC solution strengthens protection against phishing and spoofing by confirming that an email message came from the domain it claims to have come from. Skysnag generates DMARC reports for you that aid in investigating potential security problems and identifying potential risks from impersonation attacks. Get started with Skysnag and sign up for a free trial today.