Which email security measure should you use: DKIM or SPF? In this article, we’ll cover what these terms mean, when you should use them, and how they can help protect your email domains.
Email has never been more important, or more profitable for email crime networks. Today, fraudsters of all stripes spoof corporate email domains in phishing attacks and business email compromise (BEC) scams that fuel nearly $9 billion in business losses each year. Get impersonated in these attacks, and your company could face significant reputational damage in the marketplace.
So what is SPF (Sender Policy Framework)? And what is DKIM (DomainKeys Identified Email)? They both are important email security standards designed to help prevent hackers from spoofing your domains for use in email attacks targeting your customers, partners, and the general public.
I. How Domain Spoofing Works
A fraudster only needs to set up or compromise an SMTP server in order to fake an email. From there, they can change the email addresses for “From,” “Reply-To,” and “Return-Path” to make their phishing emails appear to be official communications from the person or company they are impersonating.
The Simple Message Transfer Protocol (SMTP), which email systems utilize to send, receive, or relay outgoing emails, lacks a mechanism for validating email addresses, which makes this identity fraud conceivable. Early email authentication methods like S/MIME did not catch on to effectively counter this problem. But starting in the middle of the 2000s, two new email security standards SPF and DKIM began to succeed where prior strategies had failed.
II. How SPF Works
SPF enables email senders to designate which IP addresses are permitted to send email from a specific domain, which is its most basic function. By publishing that policy as a TXT record in the DNS for the specified domain, for instance, a domain owner can specify that only IP 5.6.7.8.9 is permitted to send email from @YourCompanyURLHere.com.
By utilizing our SPF checker tool to search for SPF records, you may determine which servers are permitted to deliver emails for your domains.
Receiving email servers run a DNS record query on your sending domain to see if the IP address provided in the SPF record matches the IP address used to send the email. In the absence of this, the email will not pass authentication, assisting in the removal of malicious emails that try to take advantage of the connected
III. How DKIM Works
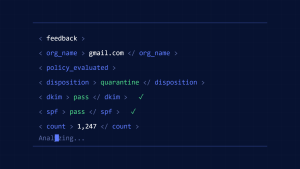
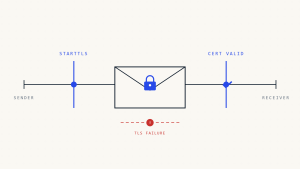
The public key(s) required to authenticate such digital signatures are made available by DKIM. Receiving email providers can then verify that the email hasn’t been altered while it’s in transit. The public key TXT record is requested from the transmitting domain’s DNS when an SMTP server receives an email with such a signature in the header. The recipient email service provider may flag the message as spam or ban the sender’s IP address entirely if the check is unsuccessful or the signature is missing.
IV. Which One is Better?
In the end, this is a “better together” situation rather than an either/or choice. This is due to the fact that SPF and DKIM both deal with a different, but equally important, aspect of email security. SPF makes it possible to verify whether an email claiming to be from your business was actually sent from one of your recognized IP addresses. Additionally, DKIM verifies that the email was not forged or changed before being sent to the intended recipient. However, it’s also crucial to remember that DKIM and SPF do not offer a comprehensive solution for email authentication, whether they are used alone or jointly.
For that, we’ll need to add an additional acronym to the conversation:
V. Why DMARC Makes All the Difference
Domain-based Message Authentication, Reporting & Conformance (DMARC), a common email authentication system that complements SPF and DKIM with a policy layer, was first proposed in 2012. Using DMARC, businesses can post guidelines that specify when email providers should rely on DKIM and SPF for a specific domain and what to do if messages don’t pass either of those checks.
The most stringent DMARC enforcement policy setting is rejected (p=reject), which instructs the receiving email server to reject email messages that fail DMARC authentication and prevent them from reaching their intended recipient. A DMARC record can be created and assigned to a DNS quite easily. However, establishing DMARC across a large number of domains can quickly become quite difficult for large enterprises.
Create a Skysnag account here to generate your DMARC record
VI. Conclusion
Skysnag automates DMARC, SPF, and DKIM for you to increase email deliverability. With that being said, avoid email spoofing attacks with Skysnag’s automated software which allows you to confirm the validity of emails. Sign up using this link for a free trial today and maintain a healthy domain name for your business.