Artificial intelligence has transformed cybersecurity landscapes, but perhaps nowhere more dramatically than in email-based brand impersonation attacks. As AI-generated phishing campaigns become increasingly sophisticated, organizations are rapidly adopting Brand Indicators for Message Identification (BIMI) as a critical defense mechanism against these evolving threats.
I. The AI Phishing Revolution
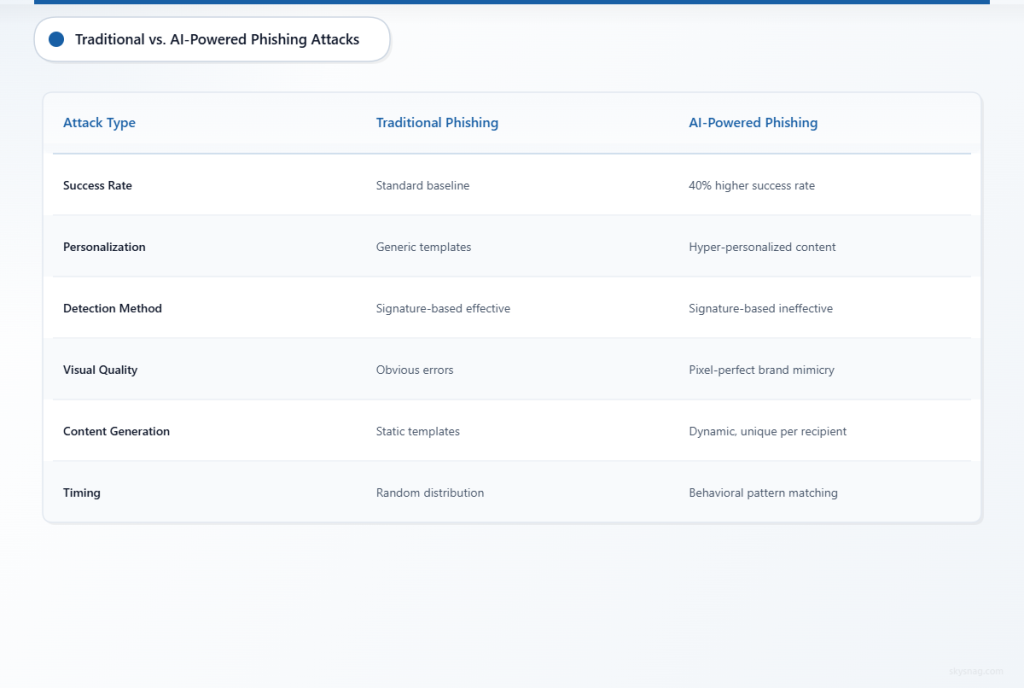
Modern AI phishing attacks have reached unprecedented levels of sophistication. Unlike traditional phishing campaigns that relied on generic templates and obvious grammatical errors, AI-powered attacks now generate personalized, contextually relevant messages that mirror legitimate brand communications with startling accuracy.
Recent threat intelligence indicates that AI-generated phishing emails achieve a 40% higher success rate compared to traditional methods. These attacks leverage machine learning algorithms to analyze genuine brand communications, creating near-perfect replicas that fool even security-aware recipients.
Key AI Phishing Characteristics in 2026
Hyper-Personalization: AI systems scrape social media, corporate websites, and data breaches to craft individually targeted messages that reference specific projects, colleagues, or company events.
Dynamic Content Generation: Advanced language models produce unique email content for each recipient, making signature-based detection methods largely ineffective.
Visual Brand Mimicry: AI-powered design tools replicate corporate logos, color schemes, and layouts with pixel-perfect precision, creating visually indistinguishable impersonations.
Behavioral Pattern Matching: Machine learning algorithms study legitimate sender patterns, timing communications to align with normal business operations and communication rhythms.
II. Brand Impersonation Attack Vectors
CEO Fraud Evolution
Traditional CEO fraud relied on simple display name spoofing and basic social engineering tactics. Today’s AI-powered versions analyze executive communication styles, meeting schedules, and travel patterns to craft highly convincing impersonation attempts.
These attacks often coincide with public executive activities, leveraging AI to monitor social media, press releases, and corporate announcements to time fraudulent requests during periods when executives are likely unavailable for verification.
Vendor Impersonation Schemes
Supply chain attacks have evolved beyond basic invoice fraud. AI systems now impersonate trusted vendors by analyzing historical communication patterns, contract terms, and payment schedules. These attacks create fraudulent payment requests that align perfectly with expected vendor interactions.
Customer Service Exploitation
AI-powered attackers impersonate customer service representatives with unprecedented accuracy, using natural language processing to match brand voice, terminology, and response patterns. These attacks target both customers and employees, exploiting trust in official support channels.
III. BIMI as a Critical Defense Mechanism
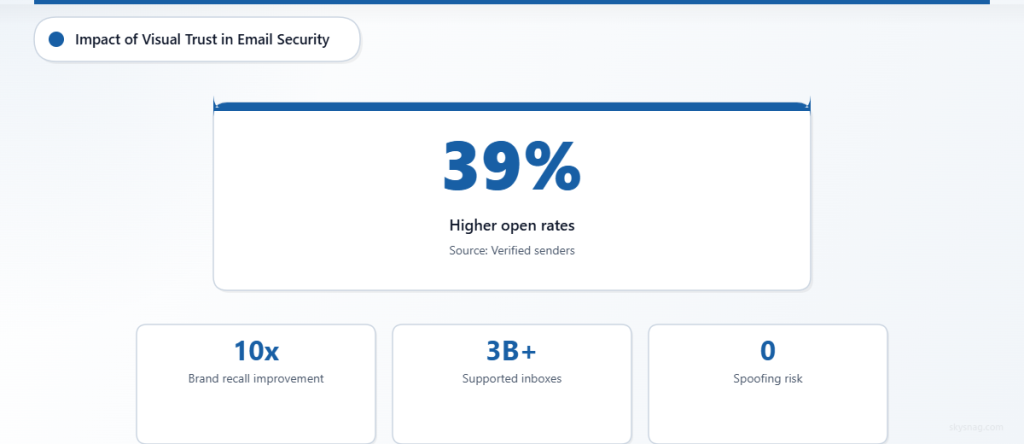
Brand Indicators for Message Identification (BIMI) has emerged as the frontline defense against AI-powered brand impersonation. By providing visual verification of sender authenticity directly within email clients, BIMI creates an immediate trust indicator that’s difficult for attackers to replicate.
Visual Trust Verification
BIMI displays verified brand logos alongside authenticated emails, providing recipients with instant visual confirmation of sender legitimacy. This immediate recognition helps users differentiate between genuine communications and sophisticated AI impersonations.
Unlike traditional text-based authentication methods that many users ignore, BIMI’s visual approach leverages natural human pattern recognition to identify authentic communications quickly.
Integration with Email Authentication
BIMI requires strict email authentication implementation, including SPF, DKIM, and DMARC policies set to enforcement mode. This creates a robust technical foundation that AI-generated attacks struggle to bypass, even with sophisticated spoofing techniques.
The visual component combined with technical authentication creates a multi-layered defense that addresses both human psychology and technical security requirements.
IV. Implementation Acceleration Trends
Executive-Driven Adoption
Board-level executives increasingly view BIMI implementation as essential brand protection. High-profile AI phishing incidents targeting executive communications have elevated BIMI from a technical consideration to a business imperative.
Security leaders report that BIMI adoption decisions now originate from executive leadership rather than IT departments, reflecting growing awareness of AI-powered threats among business decision-makers.
Customer Protection Focus
Organizations recognize that protecting customer communications requires proactive brand authentication. BIMI implementation has shifted from internal security focus to customer experience protection, acknowledging that brand impersonation attacks damage customer relationships and organizational reputation.
Compliance and Risk Management
Regulatory bodies and cyber insurance providers increasingly recognize BIMI as a reasonable security control for organizations handling sensitive communications. This external validation accelerates adoption among risk-conscious organizations.
V. Technical Implementation Challenges
Certificate Authority Requirements
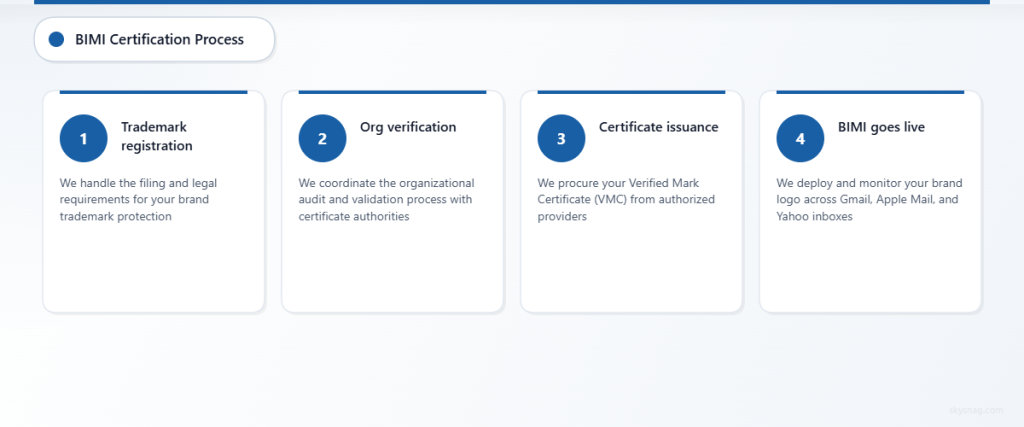
BIMI implementation requires Verified Mark Certificates (VMCs) from authorized Certificate Authorities, creating additional complexity and cost considerations. Organizations must navigate certificate procurement processes while maintaining brand consistency across multiple domains and subsidiaries.
Domain Configuration Complexity
Large organizations with complex domain structures face significant technical challenges when implementing BIMI across multiple brands, subsidiaries, and communication channels. Proper configuration requires coordination between security, marketing, and IT teams.
Email Client Support Variations
While major email providers support BIMI, implementation variations and display differences create inconsistent user experiences. Organizations must test BIMI appearance across multiple clients and adjust brand assets accordingly.
VI. Prevention and Protection Strategies
Comprehensive Email Authentication
Implement robust SPF, DKIM, and DMARC policies as BIMI prerequisites. Set DMARC to enforcement mode (p=reject) to prevent domain spoofing while ensuring legitimate emails authenticate properly.
Skysnag Certify provides automated email authentication management, simplifying DMARC implementation and ongoing policy optimization necessary for BIMI adoption.
Visual Brand Asset Management
Develop consistent brand assets optimized for BIMI display across different email clients. Create high-resolution logos that maintain clarity at small sizes while adhering to BIMI technical specifications.
Employee Awareness Training
Educate employees about AI-powered phishing characteristics and BIMI visual indicators. Training should emphasize the importance of logo verification while acknowledging that sophisticated attacks may still require additional verification steps.
Continuous Monitoring and Adjustment
Monitor BIMI implementation effectiveness through authentication reports and user feedback. Adjust policies and brand assets based on authentication failures and display issues across different email environments.
Incident Response Planning
Develop specific incident response procedures for AI-powered brand impersonation attempts. Include steps for rapid BIMI policy updates, communication with affected parties, and coordination with email service providers.
VII. Key Takeaways
AI-powered brand impersonation attacks represent a fundamental shift in email security threats, requiring organizations to adopt proactive visual authentication measures like BIMI. The sophistication of AI-generated phishing campaigns has made traditional detection methods insufficient, elevating BIMI from optional enhancement to essential security control.
Organizations implementing BIMI gain both technical protection through strengthened email authentication and psychological protection through visual trust indicators. As AI threats continue evolving, BIMI adoption provides measurable defense against increasingly sophisticated brand impersonation attempts.
The intersection of AI threats and email security demands immediate action. Organizations delaying BIMI implementation risk exposure to advanced impersonation attacks that traditional security measures cannot effectively counter.
Ready to protect your brand against AI-powered impersonation attacks? Implement BIMI with Skysnag Certify to establish visual trust indicators that defend against sophisticated phishing campaigns while strengthening your email authentication infrastructure.








