I. What is DMARC vulnerability?
DMARC vulnerability refers to errors that users make while implementing the protocol, which can range from simple syntax errors to more complex errors. Unless these vulnerabilities are troubleshot and the protocol is set up correctly, email security efforts may be invalidated. DMARC records offer many benefits to domain owners, including information about email sending sources and performance.
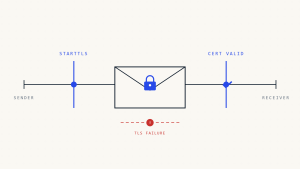
Email authentication verifies the legitimacy of email senders by checking the Mail From: header and the Return-path header. If the sender’s DNS contains the IP address that matches the email’s IP, SPF and subsequently DMARC passes for it, or else it fails. The probability of messages being delivered to clients is dependent on how accurately DMARC is configured. Existing vulnerabilities in an organization’s email security posture can weaken the chances of messages being delivered.
Protecting domains is a critical step in maintaining reputation. Several problems can arise from poor DMARC authentication, including issues with:
- Email deliverability,
- Increased vulnerability to email phishing and spoofing attacks
- Legitimate messages are marked as spam.
Domain owners can use our DMARC check tool to track allowed email senders and authenticate their DMARC records right now to address these problems.
II. DMARC Vulnerability Types
DMARC vulnerability: DNS Records Syntax Errors
A DMARC record is a TXT record that contains instructions for email receiving MTAs, separated by semicolons: For example
v=DMARC1; p=reject; rua=mailto:[email protected]; pct=100;
Small details, such as the mechanism separators (;), are essential in determining if your record is valid.
Create a Skysnag account to generate your DMARC record.
NOTE: If you already have a static DMARC record, you’d need to replace it with the generated Skysnag record to achieve compliance.
DMARC vulnerability: No DMARC Record Found
If you see a message saying your domain is missing a DMARC record, it means you don’t have a valid record published on your DNS.
To fix this, you need to create a TXT record for DMARC on your DNS, starting with v=DMARC1. Remember to define a policy (reject/quarantine/none) for your emails!
A common misconception among users is that a DMARC policy with p=none is enough to protect their domain against attacks. If the sender’s DNS contains the IP address that matches the email’s IP, SPF and subsequently DMARC passes for it, or else it fails.
A less strict policy can be beneficial if you’re only interested in monitoring your email channels, and not necessarily enforcing protection. However, it is recommended that you switch to a more strict policy once you feel confident.
We have placed this under the DMARC vulnerability category because most users implement DMARC to gain a higher degree of protection against attacks. Therefore, a policy with zero enforcement can be of no value to them.
DMARC vulnerability: p=none
This error message is often the result of not having an enforced DMARC policy. If you have a domain that is set to none, it is vulnerable to phishing attacks. It is recommended that you change your policy to p=reject/quarantine as soon as possible. To do this, you need to modify your DNS record from p=none to p=quarantine
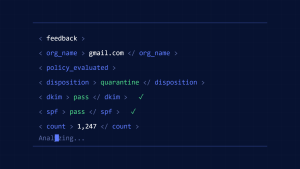
III. Fix DMARC Vulnerabilities
Skysnag’s automated DMARC solution fixes DMARC vulnerabilities instantly and securely while giving protection against phishing and spoofing by confirming that an email message came from the domain it claims to have come from. Skysnag generates DMARC reports for you that aid in investigating potential security problems and identifying potential risks from impersonation attacks. Get started with Skysnag by signing up using this link for a free trial today and increase email deliverability.