I. Understanding DMARC: A Comprehensive Guide by Skysnag
Introduction to DMARC
II. What is DMARC?
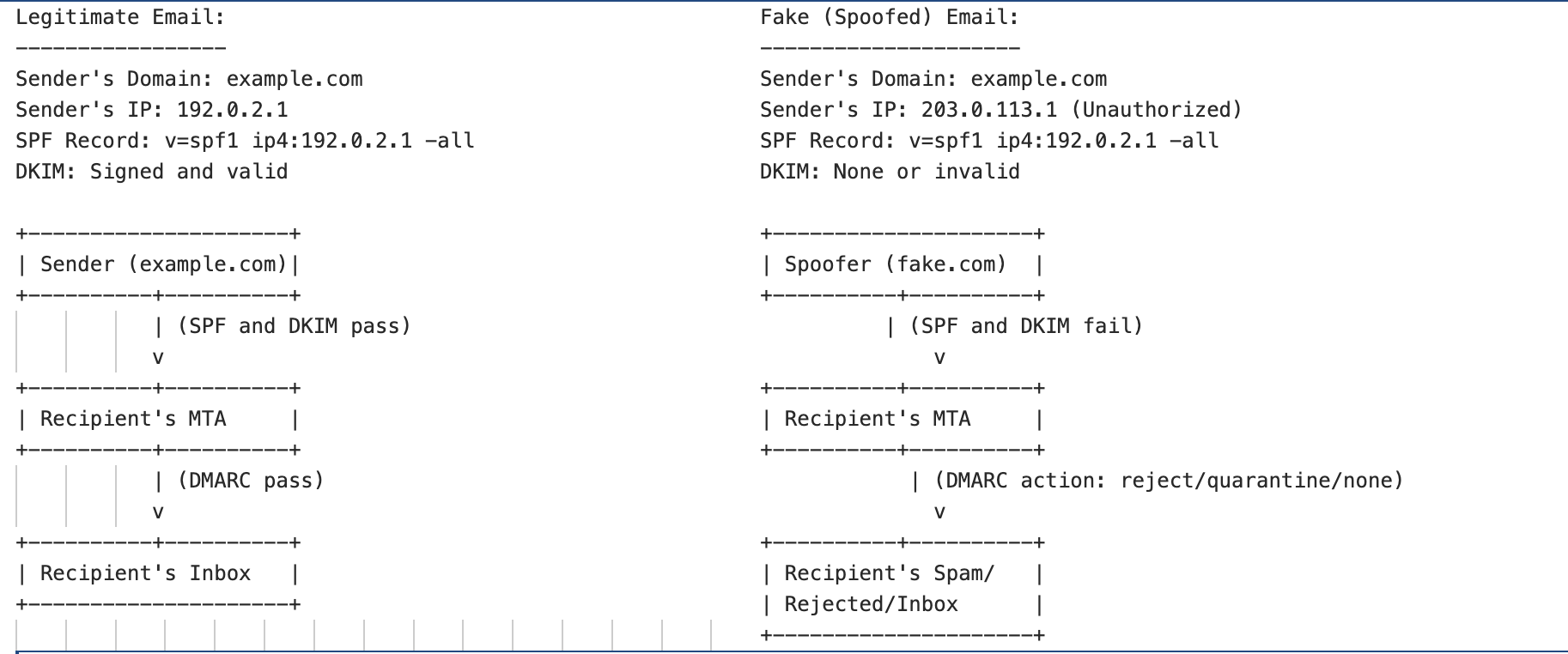
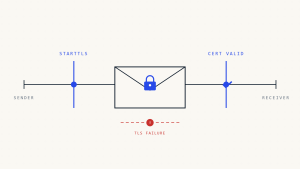
Domain-based Message Authentication, Reporting, and Conformance (DMARC) is an email authentication protocol that helps protect email domains from being used for phishing and spoofing attacks. DMARC builds on two existing authentication mechanisms: Sender Policy Framework (SPF) and DomainKeys Identified Mail (DKIM). By implementing DMARC, domain owners can specify how receiving mail servers should handle unauthenticated emails, reducing the likelihood of fraudulent emails reaching recipients’ inboxes.
Why is DMARC Important?
DMARC is crucial for enhancing email security and protecting users from phishing and other email-based threats. It allows domain owners to monitor and control how their domain is used in email communications, ensuring that only legitimate emails are delivered to recipients. DMARC also provides reporting capabilities, allowing domain owners to gain insights into email traffic and potential abuse.
III. How DMARC Works
IV. Components of DMARC
DMARC relies on two key components: SPF and DKIM.
SPF (Sender Policy Framework)
SPF is an email authentication method that allows domain owners to specify which mail servers are authorized to send emails on their behalf. SPF records are published in the domain’s DNS and are checked by receiving mail servers to verify the sender’s authenticity.
DKIM (DomainKeys Identified Mail)
DKIM is another email authentication method that uses cryptographic signatures to verify the integrity and authenticity of an email message. DKIM signatures are added to email headers and are verified by receiving mail servers against the public key published in the domain’s DNS.
DMARC Policy Types
DMARC policies define how receiving mail servers should handle unauthenticated emails. There are three types of DMARC policies:
None Policy
This policy is used for monitoring purposes and does not affect email delivery. It allows domain owners to receive reports on email authentication results.
Quarantine Policy
This policy instructs receiving mail servers to quarantine unauthenticated emails, typically by placing them in the recipient’s spam or junk folder.
Reject Policy
This policy instructs receiving mail servers to reject unauthenticated emails, preventing them from reaching the recipient’s inbox.
V. Implementing DMARC
Steps to Set Up DMARC
- Ensure that SPF and DKIM are correctly implemented for your domain.
- Create a DMARC record with the desired policy and publish it in your domain’s DNS.
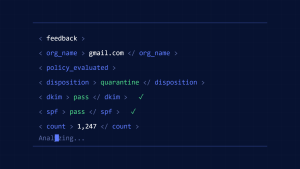
- Monitor DMARC reports to analyze email authentication results and make adjustments as needed.
DMARC Record Syntax
A DMARC record is a TXT record published in the domain’s DNS. It includes various tags that define the DMARC policy and reporting
options. Here is an example of a DMARC record syntax:
v=DMARC1; p=reject; rua=mailto:[email protected];
In this example, the v tag specifies the DMARC version, the p tag defines the policy (reject), and the rua tag indicates the email address to which aggregate reports should be sent.
VI. Benefits
- Enhanced email security: DMARC helps protect against phishing, spoofing, and other email-based attacks.
- Improved deliverability: DMARC-compliant emails are more likely to reach recipients’ inboxes, improving email deliverability rates.
- Visibility and control: DMARC provides domain owners with visibility into email traffic and control over how their domain is used in email communications.
- Brand protection: DMARC helps protect the reputation of a brand by preventing unauthorized use of its domain in fraudulent emails.
VII. Common Challenges and Solutions
- Misconfiguration: Incorrectly configured SPF, DKIM, or DMARC records can lead to email delivery issues. It’s important to carefully review and test configurations before implementing them.
- Monitoring and analysis: DMARC reports can be complex and challenging to analyze.
- Gradual implementation: It’s recommended to start with a “none” policy and gradually move to stricter policies (quarantine or reject) to minimize the risk of legitimate emails being blocked.
VIII. Conclusion
DMARC is a powerful email authentication protocol that provides domain owners with the tools they need to secure their email communications and protect their brand reputation. By implementing DMARC, organizations can gain visibility into email traffic, prevent email spoofing and phishing attacks, and improve email deliverability. While DMARC implementation may seem complex, the benefits it offers make it a valuable addition to any organization’s email security strategy.
IX. FAQs
1. What is the purpose of DMARC?
DMARC is designed to help domain owners protect their email domains from being used in phishing and spoofing attacks. It provides a way to specify how unauthenticated emails should be handled and offers reporting capabilities for monitoring email traffic.
2. How does DMARC differ from SPF and DKIM?
DMARC builds on SPF and DKIM by adding a policy layer specifying how receiving mail servers handle unauthenticated emails. DMARC also provides reporting features that allow domain owners to monitor email authentication results.
3. Can DMARC prevent all phishing attacks?
While DMARC is highly effective in preventing domain spoofing and certain types of phishing attacks, it is not a comprehensive solution. Organizations should use DMARC in conjunction with other security measures, such as employee training and email filtering.
4. How do I create a DMARC record for my domain?
To create a DMARC record, you need to define your DMARC policy, specify reporting options, and publish the record as a TXT record in your domain’s DNS. It’s important to test and validate the record before implementing it fully.
Create a Skysnag account to generate your DMARC record
5. What are the potential challenges of implementing DMARC?
Potential challenges include misconfiguration of SPF, DKIM, or DMARC records, complexity of monitoring and analyzing DMARC reports, and the need for gradual implementation to avoid blocking legitimate emails.