E-commerce businesses handle millions of customer emails daily, making them prime targets for cybercriminals seeking payment data, personal information, and access to customer accounts. A single compromised email containing order confirmations, shipping updates, or password resets can expose sensitive customer data and damage brand reputation.
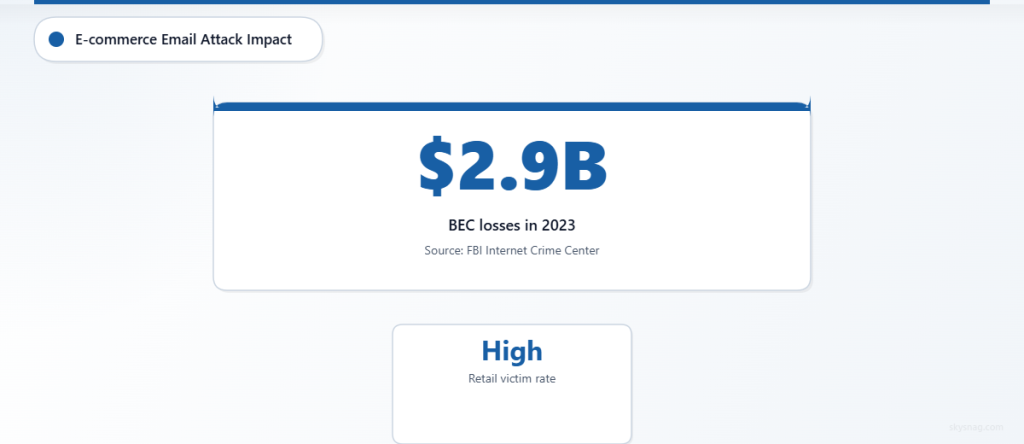
Retail organizations face unique email security challenges, from high-volume transactional messaging to sophisticated phishing attacks targeting both customers and internal teams. According to the FBI’s Internet Crime Complaint Center, business email compromise attacks resulted in over $2.9 billion in losses in 2023, with retail businesses representing a significant portion of victims.
This comprehensive checklist provides e-commerce teams with actionable steps to secure customer email communications, implement proper authentication protocols, and protect against common threats targeting online retail operations.
I. Understanding E-commerce Email Threat Landscape
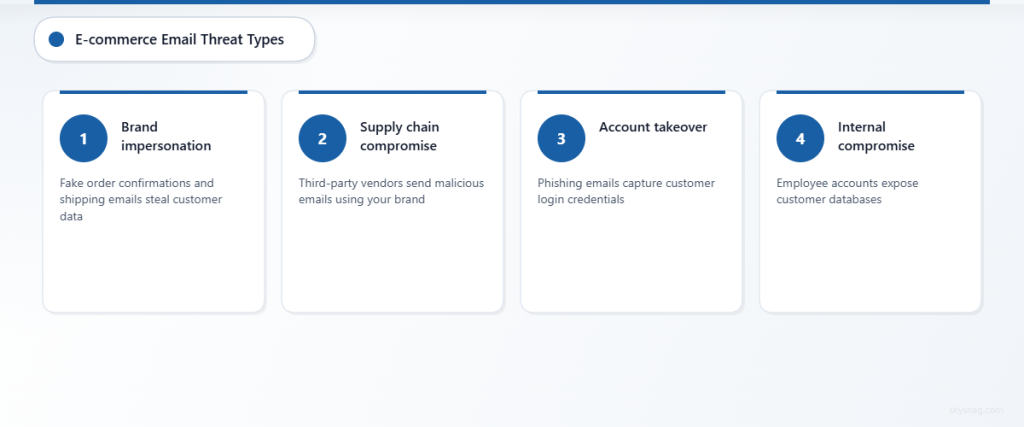
E-commerce email security threats have evolved significantly, with attackers specifically targeting the trust relationship between retailers and customers. Common attack vectors include:
Brand impersonation attacks exploit customer trust by mimicking legitimate retailer communications. These attacks often target customers during peak shopping seasons, using convincing order confirmation or shipping notification emails to steal credentials or payment information.
Supply chain email compromise affects third-party vendors, payment processors, and logistics partners who have access to customer email addresses. When these partners’ email systems are compromised, attackers can send malicious emails that appear to come from trusted retail brands.
Account takeover attempts frequently begin with phishing emails designed to capture customer login credentials. Once attackers gain access to customer accounts, they can view order history, payment methods, and personal information.
Internal email compromise poses significant risks when employee email accounts are compromised, potentially exposing customer databases, payment processing information, and business operations data.
II. Technical Email Authentication Requirements
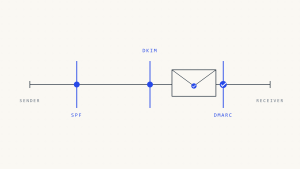
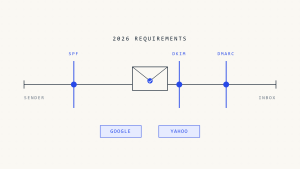
Email authentication protocols form the foundation of e-commerce email security, helping prevent domain spoofing and ensuring legitimate communications reach customers reliably.
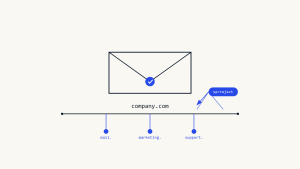
SPF (Sender Policy Framework) configuration requires careful management in e-commerce environments where multiple systems send email on behalf of your domain. Common sending sources include:
- Primary e-commerce platform (Shopify, Magento, WooCommerce)
- Email service providers for marketing campaigns
- Customer service platforms and helpdesk systems
- Payment processors sending transaction confirmations
- Shipping providers sending tracking notifications
DKIM (DomainKeys Identified Mail) implementation ensures email integrity and authenticity. E-commerce businesses should implement DKIM signing for all outbound email streams, including transactional emails, marketing communications, and automated notifications.
DMARC (Domain-based Message Authentication, Reporting and Conformance) provides visibility into email authentication failures and enables policy enforcement. For e-commerce businesses, DMARC reports reveal unauthorized use of your domain in phishing campaigns targeting customers.
Skysnag Comply simplifies email authentication management for retail businesses, providing automated monitoring of authentication failures and policy optimization recommendations specifically designed for high-volume e-commerce email environments.
III. E-commerce Email Security Implementation Checklist
Use this checklist as a practical starting point for securing your e-commerce email infrastructure. The specific requirements will depend on your platform, email volume, and third-party integrations, but these core elements apply to most retail operations.
Domain and DNS Security
- [ ] Configure SPF records to include all legitimate email sending sources, including e-commerce platforms, ESPs, and third-party services.
- [ ] Implement DKIM signing for all outbound email streams, with separate keys for transactional and marketing email systems.
- [ ] Deploy DMARC policy starting at p=none for monitoring, progressing to p=quarantine and ultimately p=reject based on authentication success rates.
- [ ] Register defensive domains for common typosquatting variations of your brand domain to prevent customer phishing attacks.
- [ ] Enable DNS security features like DNSSEC to protect against DNS hijacking attacks targeting email authentication records.
E-commerce Platform Email Configuration
- [ ] Review and secure email settings in your e-commerce platform admin panel, ensuring only authorized users can modify email templates and sending configurations.
- [ ] Implement email template approval workflows for transactional emails to prevent unauthorized modifications that could compromise customer trust.
- [ ] Configure proper From addresses and display names for all automated emails to maintain consistent brand identity and customer recognition.
- [ ] Set up email logging and monitoring for all platform-generated communications to track delivery issues and potential security incidents.
- [ ] Enable two-factor authentication for all admin accounts with email configuration privileges.
Customer Communication Security
- [ ] Implement email encryption for communications containing sensitive customer information, such as account statements or personal data requests.
- [ ] Design email templates with clear visual indicators of authenticity, including consistent branding, official contact information, and security disclauses.
- [ ] Establish secure communication channels for password resets, account changes, and high-value transaction confirmations.
- [ ] Create customer education materials about identifying legitimate emails from your business versus phishing attempts.
- [ ] Implement email verification processes for account creation and significant account changes to prevent unauthorized access.
Third-Party Integration Security
- [ ] Audit all third-party services authorized to send email on behalf of your domain, removing inactive or unnecessary integrations.
- [ ] Establish security requirements for email service providers, including authentication protocols, data handling practices, and incident response procedures.
- [ ] Monitor third-party email authentication compliance through DMARC reports, identifying integration issues that could impact deliverability.
- [ ] Implement vendor risk assessments for any service provider handling customer email addresses or sending communications on your behalf.
- [ ] Maintain updated contact information and security protocols for all third-party email integrations.
Internal Team Email Security
- [ ] Deploy email security solutions that scan incoming messages for phishing attempts, malware, and suspicious attachments targeting employee accounts.
- [ ] Implement employee training programs focused on e-commerce-specific phishing threats, including fake vendor communications and customer impersonation attempts.
- [ ] Establish secure email practices for customer service teams handling sensitive customer information and payment details.
- [ ] Configure email retention policies that balance customer service needs with data privacy requirements and security best practices.
- [ ] Set up incident response procedures specifically for email security breaches affecting customer communications.
Monitoring and Compliance
- [ ] Implement continuous monitoring of email authentication success rates across all sending sources to identify configuration drift or attacks.
- [ ] Establish regular reviews of DMARC reports to identify new threats, authentication failures, and unauthorized domain usage.
- [ ] Document email security controls and procedures to support compliance audits and regulatory requirements.
- [ ] Create metrics and KPIs for email security effectiveness, including authentication success rates, phishing detection rates, and customer complaint trends.
- [ ] Schedule quarterly assessments of email security configuration to account for new integrations, platform updates, and evolving threat landscape.
IV. Automated Email Security Management
Managing email security across multiple e-commerce platforms, third-party integrations, and high email volumes requires automated monitoring and response capabilities. Manual management becomes impractical as businesses scale and integrate additional services.
Automated DMARC monitoring provides real-time visibility into authentication failures, helping identify configuration issues before they impact customer communications. This is particularly important during peak shopping seasons when email volumes spike and new sending sources may be temporarily added.
Policy automation ensures that email authentication settings remain properly configured as platforms update, integrations change, and new services are added. Without automation, authentication records can become outdated or incomplete, creating security gaps that attackers can exploit.
Skysnag Comply offers specialized email security automation for e-commerce businesses, including integration monitoring, policy optimization, and threat detection specifically designed for retail environments with complex email infrastructures.
V. Key Takeaways
E-commerce email security requires comprehensive protection spanning domain authentication, platform configuration, customer communications, and internal team practices. The high volume and complexity of retail email operations make automated monitoring and management essential for maintaining security without disrupting business operations.
Successful implementation focuses on three core areas: technical authentication protocols that prevent domain spoofing, secure communication practices that protect customer data, and continuous monitoring that identifies threats and configuration issues before they impact operations.
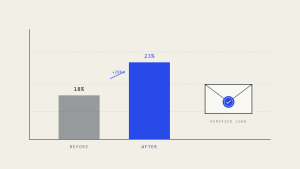
Regular assessment and optimization of email security controls ensures protection keeps pace with business growth, platform changes, and evolving threat landscape. Organizations that implement comprehensive email security see improved customer trust, better email deliverability, and reduced risk of costly security incidents.
Ready to secure your e-commerce email infrastructure? Explore Skysnag Comply for automated email authentication management designed specifically for retail businesses with complex email requirements.