Email services provided by third parties facilitate crucial business communications. Businesses and startups alike frequently like outsourcing their marketing and business emails. This calls for the use of third-party services to manage everything from lists to events to deliverability monitoring.
Let’s dive in:
I. Why is it crucial for third-party senders to comply with DMARC?
By integrating DMARC with all of your third-party email senders, you can stop malware, phishing, and spoofing attacks from infiltrating your domain. While companies keep in touch with their clients and potential consumers, email is essential to the success of any organization. It is widely employed as a key tool for market research and communication. Regardless of the email service provider you choose, make sure to ask if they can send DMARC-compliant emails on your behalf.
In order for DMARC compliance to be genuinely effective, third-party email senders must have a DMARC record. If not, they can put your business at risk of fraudulent impersonation attempts.
Create a Skysnag account to generate your DMARC record.
II. How to make Third-party Vendors DMARC-Compliant
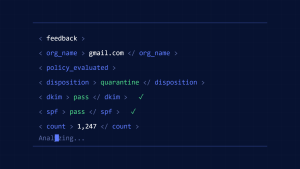
A third-party vendor must have both a valid SPF record and a valid DKIM signature in order to be DMARC-compliant. Once set up, they can build a DMARC record detailing what should happen to email communications that fail DMARC authentication.
The third-party senders domain, which it will use to send emails on your behalf, should have the DMARC record published in the DNS (Domain Name System).
The third-party senders should check their email communications after the DMARC record has been set up to make sure they are not being faked and that they are adhering to the DMARC standard. If not, they should take action to fix the problem.
III. Steps to take when Integrating Third-Party Senders
Working with third-party senders is frequently important and beneficial for the organization’s progress. Here are several steps to accomplish it:
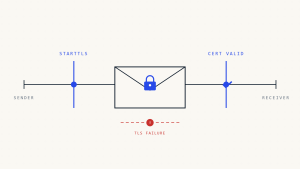
SPF Records Must Be Obeyed When Sending Messages
By adding an include:third party.tld in the SPF record, this can be achieved. Instead of using an include: approach, certain organizations may demand explicit IP addresses to be entered into the domain’s SPF record.
Deploy DKIM Signing into Practice for the Current Domain
Make sure you are signing with at least a 1024-bit size when configuring a DKIM signature. The signing domain (d=) and the communication’s sending domain need to be compatible.
IV. Final thoughts
With Skysnag, businesses have, however, been able to quickly reduce phishing-based brand impersonations to almost zero when deploying our automated DMARC solution. This not only has helped safeguard the reputation of our clients but also the effectiveness of revenue-generating email campaigns, as well as protection from expensive email scams. Get started with Skysnag and sign up using this link to stay protected from impersonation attacks.