The Skysnag Blog
October 11, 2023
What is Phishing Simulation?
According to IRONSCALES survey, on the current Findings from State of cybersecurity, 81% of firms worldwide have seen an increase […]
Explore insights

October 11, 2023
Can my domain have more than one DKIM record?
October 11, 2023
Why you should not DIY DMARC or use a reporting tool

October 11, 2023
How to enable DKIM for Communicator?

October 11, 2023
How to Set Up DKIM for Infusionsoft?
October 11, 2023
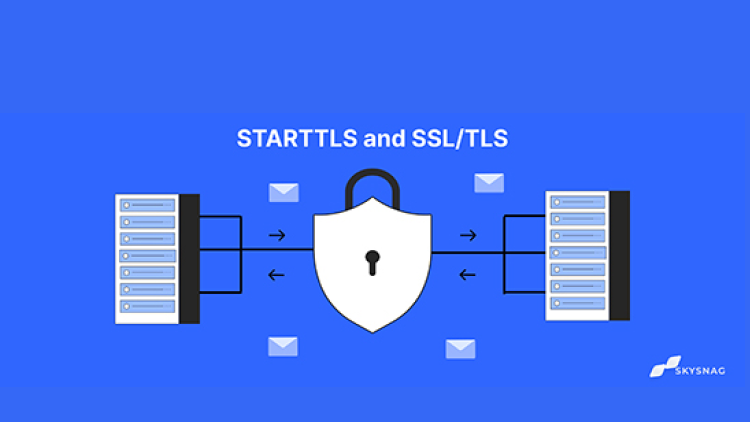
STARTTLS and SSL/TLS? Email Encryption explained
October 11, 2023
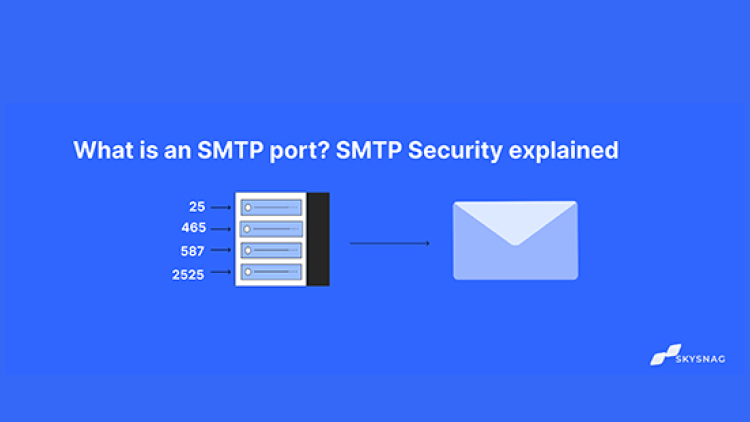
What is an SMTP port? SMTP Security explained
October 11, 2023
What is Domain Spoofing?
October 11, 2023
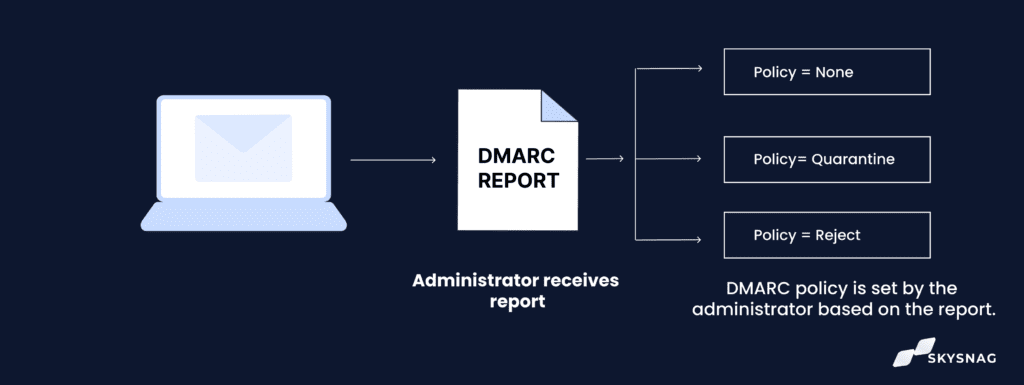
All you need to know about DMARC Reports
October 11, 2023
What is a DKIM Selector and how does it work?
October 11, 2023
3 Steps to Fix “No DMARC Record Found”

October 11, 2023
How to Set Up a DKIM Record for Intercom?

October 11, 2023
