If you’re new to email authentication, it’s likely that you’ve run up terms like DMARC, DKIM, and SPF and want to better understand them so you can choose which one works for you.
I. DMARC
A method for validating emails called Domain-based Message Authentication, Reporting, and Conformance (DMARC) was created to identify and stop email spoofing. DMARC also provides a means for email senders and recipients to share information about messages that fail DMARC authentication.
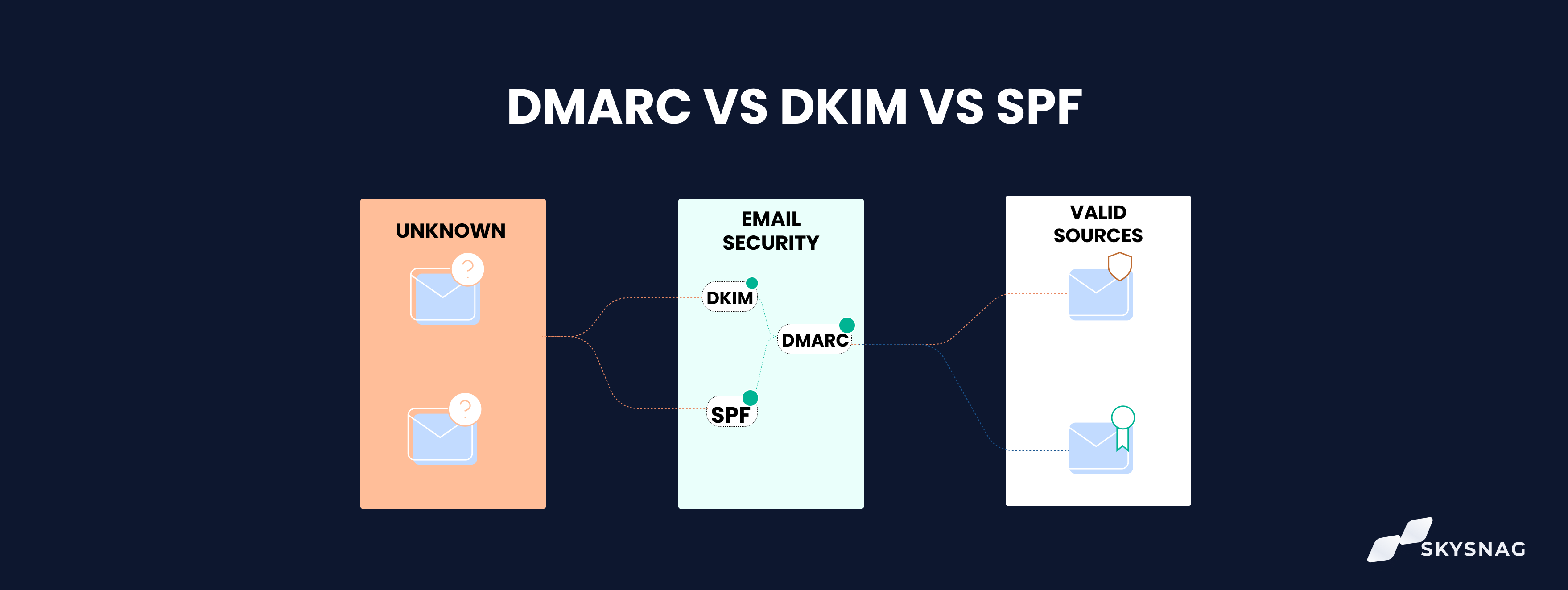
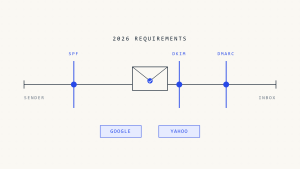
SPF and DKIM are the other two techniques that DMARC is made to cooperate with. DMARC adds to the authentication given by SPF and DKIM by prescribing how email recipients should cope with failures in SPF or DKIM authentication. Email senders and recipients can transmit information about messages that are not authenticated by DMARC using DMARC.
II. DKIM
DKIM enables a business to assume responsibility for message transmission in a way that mailbox providers can verify. Cryptographic authentication allows for this verification.
To sign email communications on behalf of a domain, DKIM employs public-key cryptography. When an email message is signed with DKIM, the recipient can use the DKIM key to verify that the message was truly sent by the stated sender and that the message has not been altered in transit.
III. SPF
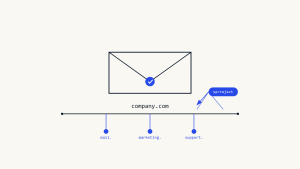
Email spoofing can be found using the Sender Policy Framework (SPF), a technique for validating emails. The act of creating emails using a falsified sender address is known as email spoofing. Email senders can define through SPF which IP addresses are permitted to send emails on their domain’s behalf. Receivers of emails can use the SPF data published by senders to confirm that emails claiming to be sent from a specific domain are actually sent from IP addresses that are allowed by that domain.
SPF is a quick and efficient method for spotting various email spoofing attempts, although it is not error-proof. SPF alone cannot stop all email spoofing attempts, but it can be used in conjunction with other anti-spoofing tools, like DMARC, to increase the likelihood of email spoofing detection and prevention.
IV. DMARC vs SPF vs DKIM
It’s important to comprehend the differences between DMARC vs SPF vs DKIM.
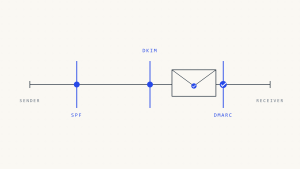
A DNS TXT record is used to declare who is allowed to send emails on behalf of the domain. The recipient’s server checks the SPF record of the sending domain when an email is sent to see if the IP address of the sender is permitted to send emails on the domain’s behalf. If the IP address is prohibited, the email will be marked as spam.
DKIM verifies that an email hasn’t been changed while it’s being forwarded. DKIM is used to verify that an email has not been tampered with in transit. It stores a public key that can be used to confirm the legitimacy of an email in a DNS TXT record. The recipient’s server uses the public key to check that an email hasn’t been altered during transmission when one is sent.
When an email is sent, the recipient’s server checks the sending domain’s DMARC record to determine whether the sender’s IP address is authorized to send emails on the domain’s behalf. The email will be labeled as spam if the IP address is not permitted in SPF.
The DKIM public key is also used by the recipient’s server to confirm that the email hasn’t been tampered with while in transit.
V. Is DMARC deployable without DKIM?
Yes. Even without a DKIM record in your DNS, it is still possible to publish a DMARC record. This is due to the requirement that your emails pass either SPF or DKIM authentication, not both in order to be deemed DMARC compliant.
Create a Skysnag account to generate your DMARC record.
VI. Conclusion
Skysnag automates DMARC, SPF, and DKIM for you, saving you the trouble and time required for manual configuration. Unlock insights, bypass email authentication configuration issues including SPF and DKIM; and protect your domain from spoofing with strict DMARC enforcement, all autonomously with Skysnag. Get started with Skysnag and sign up using this link for a free trial today.