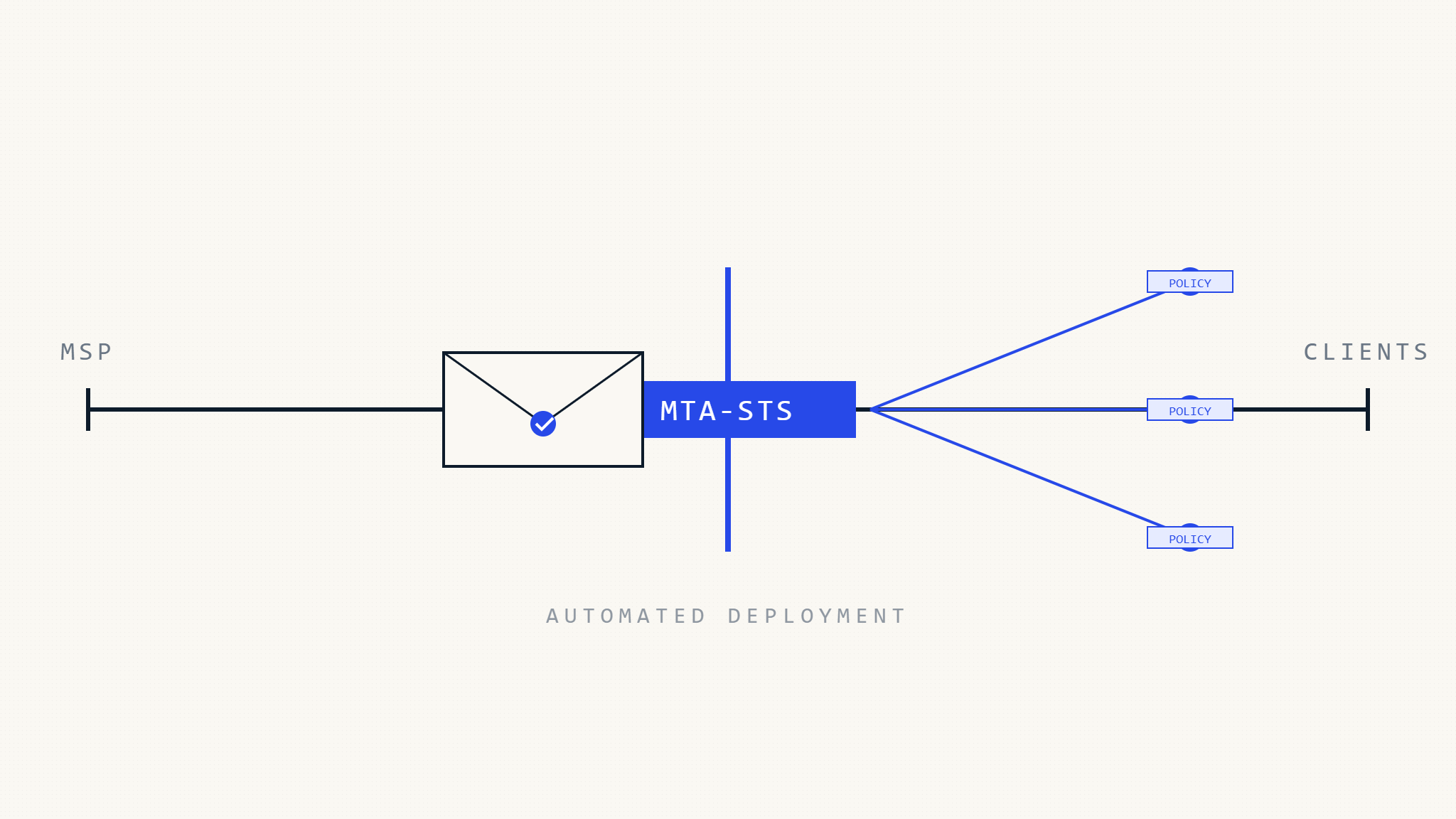
Managing email security across multiple client environments presents unique challenges for MSPs. MTA-STS (Mail Transfer Agent Strict Transport Security) deployment requires careful planning when serving diverse client bases with varying security requirements and technical infrastructures.
This comprehensive guide walks through scalable MTA-STS implementation strategies that enable MSPs to deliver consistent email security protection while maintaining operational efficiency across their entire client portfolio.
I. Understanding MTA-STS in Multi-Tenant Environments
MTA-STS enforces encrypted connections between email servers by publishing security policies that sending mail servers must follow. For MSPs, implementing MTA-STS across multiple client domains requires balancing standardization with customization.
The standard defines how mail servers discover and validate security policies through DNS TXT records and HTTPS-hosted policy files. MSPs must consider how to scale this architecture across hundreds or thousands of client domains while maintaining centralized management and monitoring capabilities.
Key considerations include policy hosting infrastructure, certificate management, DNS coordination, and compliance reporting aggregation across all managed domains.
II. Pre-Deployment Planning and Architecture
Client Domain Assessment
Begin by cataloging all managed client domains and their current email infrastructure configurations. Document existing MX records, current TLS capabilities, and any legacy email systems that may require special handling.
Identify domains with shared hosting arrangements, custom email routing configurations, or compliance requirements that may influence MTA-STS policy settings. This assessment forms the foundation for your deployment strategy.
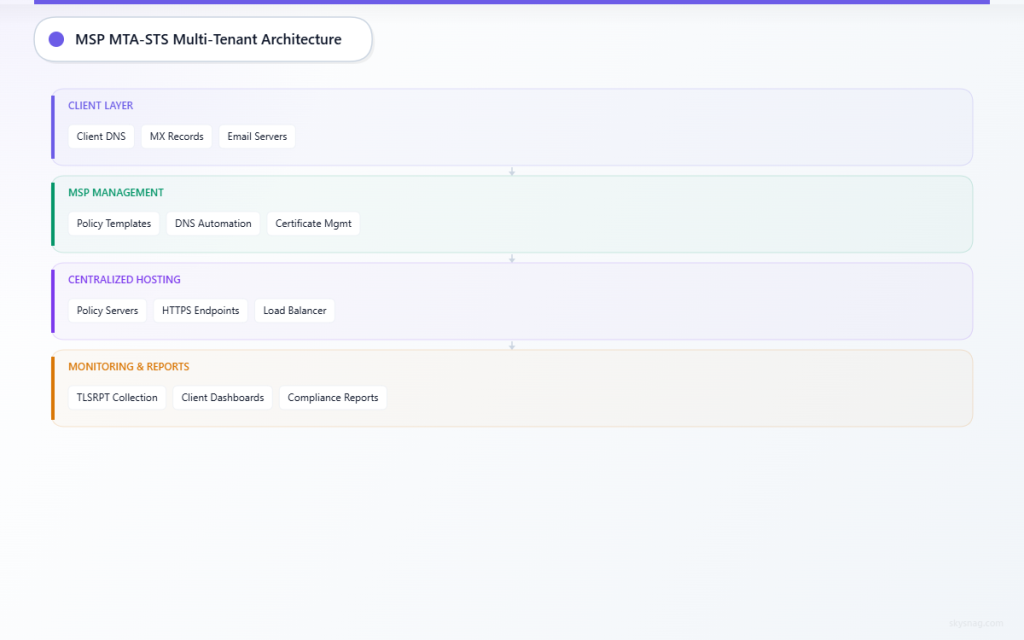
Infrastructure Requirements
Design a centralized policy hosting infrastructure capable of serving MTA-STS policies for all client domains. Consider using a dedicated subdomain structure that allows for per-client customization while maintaining operational simplicity.
Plan for SSL certificate management across all policy hosting endpoints. Wildcard certificates or automated certificate management through services like Let’s Encrypt can significantly reduce ongoing operational overhead.
III. Multi-Tenant MTA-STS Implementation Strategy
Centralized Policy Hosting Architecture
Implement a tiered hosting structure that serves MTA-STS policies from centralized infrastructure while allowing client-specific customizations:
https://mta-sts.client1.example/
https://mta-sts.client2.example/
https://mta-sts.client3.example/This approach provides operational consistency while maintaining the appearance of client-specific implementations. Use reverse proxy configurations to route requests to appropriate policy generators based on the requesting domain.
DNS Management Automation
Develop automated DNS record deployment processes that can quickly propagate MTA-STS records across client domains. Create standardized TXT record templates that reference your centralized policy hosting infrastructure.
For clients with existing DNS management processes, provide clear documentation and change requests that their teams can implement. Consider offering DNS management as an additional service for clients who prefer full MSP oversight.
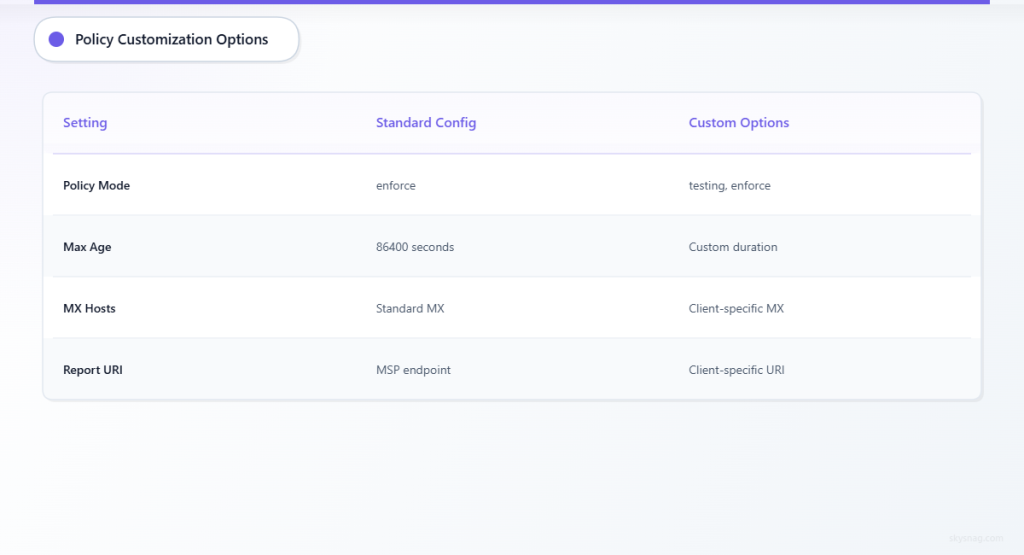
Policy Customization Framework
Design a policy management system that allows per-client customization while maintaining security best practices. Common customization requirements include:
Policy Mode Settings: Some clients may require “testing” mode during initial deployment, while others can implement “enforce” mode immediately based on their infrastructure maturity.
Maximum Age Configurations: Adjust policy caching durations based on client change management processes and infrastructure stability requirements.
MX Host Specifications: Customize allowed MX hosts based on each client’s specific email routing configuration and backup MX arrangements.
IV. Deployment Phases and Client Onboarding
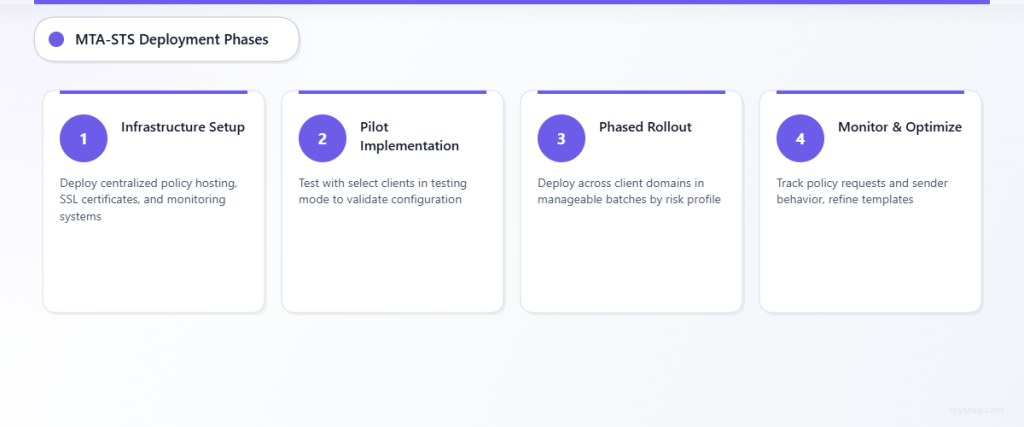
Phase 1: Infrastructure Preparation
Establish your centralized MTA-STS hosting infrastructure before beginning client deployments. Test policy serving capabilities, certificate management, and monitoring systems with a small subset of internal or pilot client domains.
Validate that your hosting infrastructure can handle the expected load from policy requests across your entire client base. Plan for traffic spikes that may occur during mass deployment phases.
Phase 2: Pilot Client Implementation
Select pilot clients representing different infrastructure types and complexity levels. Deploy MTA-STS in “testing” mode to validate policy delivery and identify any client-specific configuration requirements.
Monitor policy request patterns and sender behavior during the pilot phase. Use this data to refine your policy templates and identify common customization requirements that can be standardized across similar client types.
Phase 3: Phased Rollout
Deploy MTA-STS across client domains in manageable batches, prioritizing clients based on risk profile, compliance requirements, or existing security program maturity. This phased approach allows for operational refinement and reduces the risk of widespread issues.
Maintain detailed deployment logs and client communication throughout the rollout. Provide clients with clear explanations of the security benefits and any potential impacts on email delivery.
V. Monitoring and Management at Scale
Centralized Reporting Infrastructure
Implement comprehensive monitoring that aggregates MTA-STS reports across all managed client domains. Deploy report collection endpoints that can handle the volume of TLSRPT reports generated across your entire client base.
Create client-specific dashboards that provide visibility into their email security posture while maintaining your ability to identify trends and issues across the broader client portfolio. Consider automated alerting for policy violations or delivery failures that require immediate attention.
Operational Workflows
Develop standardized procedures for common MTA-STS management tasks including policy updates, certificate renewal, and incident response. Create runbooks that technical staff can follow regardless of which client domain requires attention.
Establish escalation procedures for client-specific issues that may require policy customization or infrastructure changes. Maintain documentation that tracks customizations and their business justifications for future reference.
VI. Integration with Skysnag MSP/MSSP Comply
Skysnag MSP/MSSP Comply provides centralized MTA-STS management capabilities specifically designed for service provider environments. The platform offers multi-tenant dashboards that allow MSPs to monitor MTA-STS deployment status and effectiveness across their entire client portfolio.
The solution includes automated policy generation tools that can quickly deploy standardized MTA-STS configurations while maintaining the flexibility to accommodate client-specific requirements. Integrated reporting capabilities aggregate TLSRPT data across all managed domains, providing comprehensive visibility into email security posture.
Skysnag’s MSP platform also includes client-branded reporting capabilities, allowing you to provide professional security reporting to clients while maintaining your centralized operational oversight. This approach supports both your internal management needs and client communication requirements.
VII. Troubleshooting Multi-Tenant Deployments
Common Implementation Challenges
DNS Propagation Issues: Coordinate with client DNS administrators or DNS hosting providers to ensure timely record deployment. Maintain documentation of DNS contacts and change management processes for each client.
Certificate Management: Monitor SSL certificate expiration dates across all policy hosting endpoints. Implement automated renewal processes where possible, and maintain manual renewal procedures for clients with specific certificate requirements.
Policy Caching Problems: Understanding how different email providers cache MTA-STS policies helps troubleshoot delivery issues. Document policy change procedures that account for caching behavior and provide appropriate lead times for policy updates.
Performance Optimization
Monitor policy request volumes and response times across your hosting infrastructure. Plan for capacity scaling during peak usage periods and implement caching strategies that reduce server load while maintaining policy freshness.
Consider geographic distribution of policy hosting infrastructure for MSPs serving clients across multiple regions. This approach can improve policy retrieval performance and provide redundancy for critical client domains.
VIII. Compliance and Documentation Requirements
Client Communication and Consent
Maintain clear documentation of MTA-STS implementation scope and client authorization for each deployment. Some organizations have change management processes that require advance notification and approval for email security policy changes.
Provide clients with detailed explanations of MTA-STS benefits and any potential impacts on email delivery. Include information about policy hosting arrangements and data collection associated with TLSRPT reporting.
Audit Trail Maintenance
Document all MTA-STS deployments, policy changes, and customizations with appropriate timestamps and business justifications. This documentation supports both operational troubleshooting and compliance audit requirements.
Maintain records of client-specific customizations and their rationale for future reference. This information becomes valuable during client reviews, compliance assessments, or infrastructure changes that may affect MTA-STS implementation.
IX. Key Takeaways
MSP MTA-STS deployment requires balancing standardization with client-specific requirements while maintaining operational efficiency at scale. Success depends on careful pre-deployment planning, phased implementation approaches, and robust monitoring infrastructure.
Centralized policy hosting combined with flexible customization capabilities enables MSPs to deliver consistent email security protection across diverse client environments. Automated deployment and management processes reduce operational overhead while ensuring comprehensive coverage across the client portfolio.
Effective multi-tenant MTA-STS implementation positions MSPs to deliver advanced email security services while maintaining the operational efficiency required for profitable service delivery. The combination of standardized processes and flexible customization capabilities ensures client satisfaction while supporting scalable business growth.
Ready to implement scalable MTA-STS deployment across your MSP client base? Explore Skysnag’s MSP/MSSP solutions and discover how centralized email security management can enhance your service delivery capabilities while reducing operational complexity.