Federal agencies face unprecedented cybersecurity challenges when migrating email systems to the cloud. The Federal Risk and Authorization Management Program (FedRAMP) establishes mandatory email security controls that cloud service providers must implement to protect sensitive government communications and maintain compliance with federal security standards.
FedRAMP email security requirements extend far beyond basic encryption, encompassing comprehensive authentication protocols, access controls, and continuous monitoring capabilities that safeguard federal communications infrastructure against sophisticated cyber threats.
I. Understanding FedRAMP’s Email Security Framework
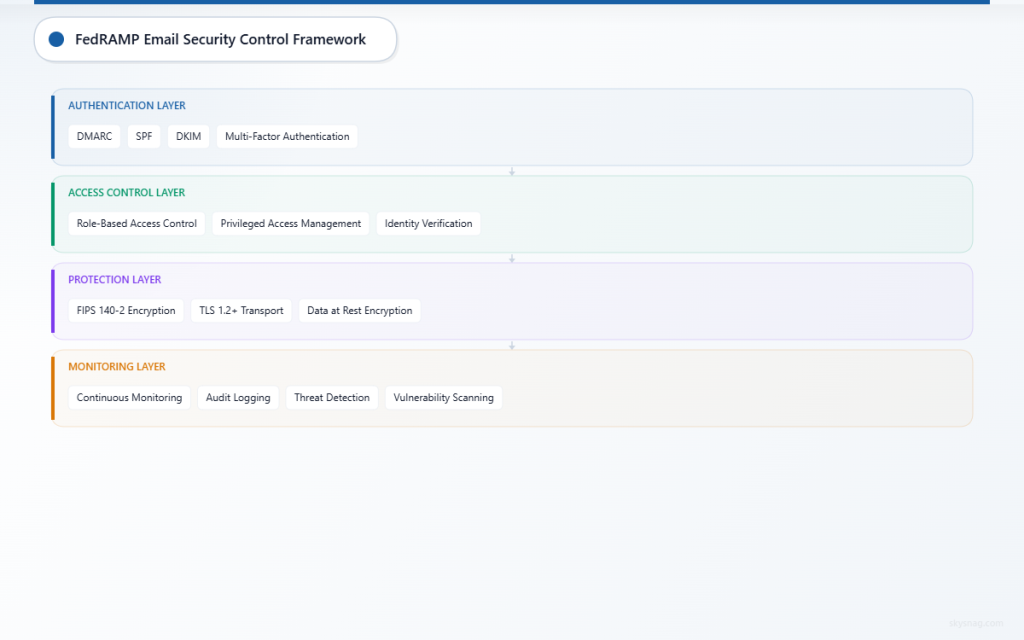
FedRAMP provides a standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services used by federal agencies. The program’s email security requirements are built upon the National Institute of Standards and Technology (NIST) Special Publication 800-53 security controls, adapted specifically for cloud environments.
Core Email Security Control Families
The FedRAMP security control baseline includes several control families directly impacting email security:
Access Control (AC): Ensures only authorized personnel can access email systems and data, with granular permissions based on roles and responsibilities.
Identification and Authentication (IA): Mandates multi-factor authentication and strong identity verification for all email system users.
System and Communications Protection (SC): Requires encryption of email data in transit and at rest, plus secure communication channels.
Audit and Accountability (AU): Establishes comprehensive logging and monitoring of all email system activities.
According to the General Services Administration, over 85% of federal agencies now rely on cloud-based email solutions, making FedRAMP compliance critical for maintaining operational security across government communications.
II. Federal Email Authentication Controls
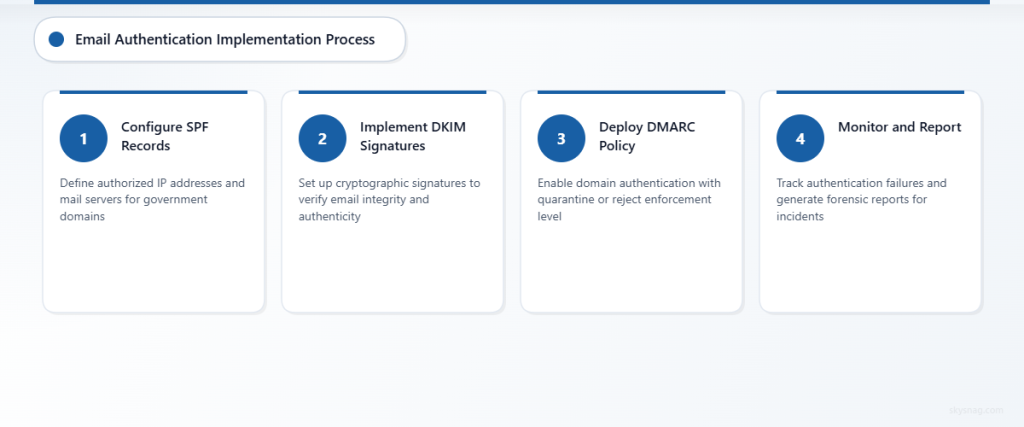
DMARC Implementation Requirements
Domain-based Message Authentication, Reporting, and Conformance (DMARC) serves as a cornerstone of federal email authentication strategy. FedRAMP requires cloud service providers to implement robust DMARC policies that:
- Authenticate sender domains to prevent email spoofing
- Provide detailed reporting on email authentication failures
- Enable policy enforcement to quarantine or reject suspicious messages
- Support forensic reporting for security incident investigation
Federal agencies must achieve DMARC policy enforcement at the “quarantine” or “reject” level, significantly reducing the risk of successful phishing campaigns targeting government personnel.
SPF and DKIM Integration
Sender Policy Framework (SPF) and DomainKeys Identified Mail (DKIM) work alongside DMARC to create a comprehensive email authentication ecosystem:
SPF Controls: Define authorized IP addresses and mail servers permitted to send email on behalf of government domains, preventing unauthorized senders from impersonating federal agencies.
DKIM Signatures: Provide cryptographic signatures that verify email integrity and authenticity, ensuring messages haven’t been tampered with during transmission.
Cloud service providers must demonstrate proper implementation and management of these authentication protocols during FedRAMP assessment processes.
III. Security Control Implementation for Cloud Providers

Encryption and Data Protection
FedRAMP mandates that cloud service providers implement Federal Information Processing Standards (FIPS) 140-2 validated encryption modules for protecting email data. This includes:
- Transport Layer Security (TLS): All email communications must use TLS 1.2 or higher encryption protocols
- Data at Rest Encryption: Email storage systems must encrypt data using approved cryptographic standards
- Key Management: Proper handling and rotation of encryption keys according to federal guidelines
Continuous Monitoring Requirements
Cloud service providers must establish comprehensive monitoring capabilities that track email system security status in real-time. The Cybersecurity and Infrastructure Security Agency reports that continuous monitoring has reduced security incident response times by up to 70% across federal agencies.
Key monitoring requirements include:
- Real-time threat detection and alerting
- Automated vulnerability scanning and assessment
- Comprehensive audit logging of all system activities
- Regular security control effectiveness assessments
Access Controls and Identity Management
FedRAMP requires implementation of robust access control mechanisms aligned with federal identity management standards:
Role-Based Access Control (RBAC): Users receive access permissions based on their specific job functions and security clearance levels.
Multi-Factor Authentication (MFA): All email system access must require at least two authentication factors, typically combining passwords with hardware tokens or biometric verification.
Privileged Access Management (PAM): Administrative access to email systems requires additional security controls and monitoring.
IV. Implementation Best Practices
Assessment and Authorization Process
Cloud service providers seeking FedRAMP authorization for email services must undergo rigorous security assessment processes:
- Documentation Review: Comprehensive evaluation of security implementation documentation and policies
- Technical Testing: Hands-on assessment of security controls and their effectiveness
- Vulnerability Assessment: Identification and remediation of potential security weaknesses
- Ongoing Monitoring: Continuous assessment of security posture and compliance status
Integration with Existing Federal Infrastructure
Successful FedRAMP email security implementation requires seamless integration with existing federal cybersecurity infrastructure, including:
- Einstein Network Monitoring: Compatibility with DHS’s network monitoring and intrusion detection systems
- Continuous Diagnostics and Mitigation (CDM): Integration with government-wide cybersecurity monitoring programs
- Trusted Internet Connections (TIC): Compliance with federal network access requirements
Solutions like Skysnag Comply help organizations maintain continuous compliance with FedRAMP email security requirements through automated monitoring and reporting capabilities that align with federal standards.
Vendor Selection Criteria
Federal agencies evaluating cloud email providers should prioritize vendors that demonstrate:
- Current FedRAMP authorization at appropriate impact levels
- Proven track record of maintaining compliance status
- Robust incident response and recovery capabilities
- Transparent security documentation and reporting processes
V. Compliance Monitoring and Reporting
Automated Compliance Validation
Modern FedRAMP email security implementations leverage automated tools to continuously validate compliance with federal requirements. These systems provide:
- Real-time monitoring of email authentication protocols
- Automated generation of compliance reports for federal oversight
- Integration with government security information and event management (SIEM) systems
- Proactive alerting for potential compliance violations
Reporting Requirements
Cloud service providers must maintain detailed documentation of their email security posture, including:
Monthly Compliance Reports: Comprehensive summaries of security control effectiveness and any identified vulnerabilities.
Incident Response Documentation: Detailed records of security incidents, response actions, and remediation efforts.
Continuous Monitoring Results: Regular updates on security control assessments and system performance metrics.
The Office of Management and Budget requires federal agencies to report email security metrics quarterly, emphasizing the importance of robust monitoring and documentation capabilities.
VI. Key Takeaways
FedRAMP email security requirements establish comprehensive protections for federal government communications in cloud environments. Success requires implementation of multi-layered security controls including robust email authentication protocols, encryption standards, and continuous monitoring capabilities.
Cloud service providers must demonstrate compliance through rigorous assessment processes and maintain ongoing security posture through automated monitoring and reporting. Federal agencies benefit from enhanced email security, improved threat detection, and standardized compliance frameworks that reduce cybersecurity risks across government operations.
Organizations seeking to meet FedRAMP email security requirements should prioritize comprehensive authentication implementations, continuous compliance monitoring, and integration with existing federal cybersecurity infrastructure to ensure successful authorization and ongoing compliance.
Ready to strengthen your email security posture? Explore Skysnag Protect for comprehensive email authentication and monitoring solutions that support federal compliance requirements.